Overview
Since the beginning of the conflict between Russia and Ukraine, the war in real world has been in full swing. Although it has reached a stalemate stage, the attack and defence in the cyberspace continues. Among them, the Ukrainian organization The IT Army of Ukraine and the Russian organization KillNet are the most powerful and representative. NoName057(16) and DDosia, which were exposed by Avast, are also new forces among them, mixed with other large and small organizations. The two camps have launched many attacks with DDoS attacks as weapons.
QiAnXin Threat Intelligence Center has also conducted long-term monitoring of DDoS attack activities around the world. This article sorts out the attack activities of the Russian and Ukrainian camps targeting important targets in the fourth quarter of 2022, and conducts in-depth analysis of individual cases.
Typical Attack Activities
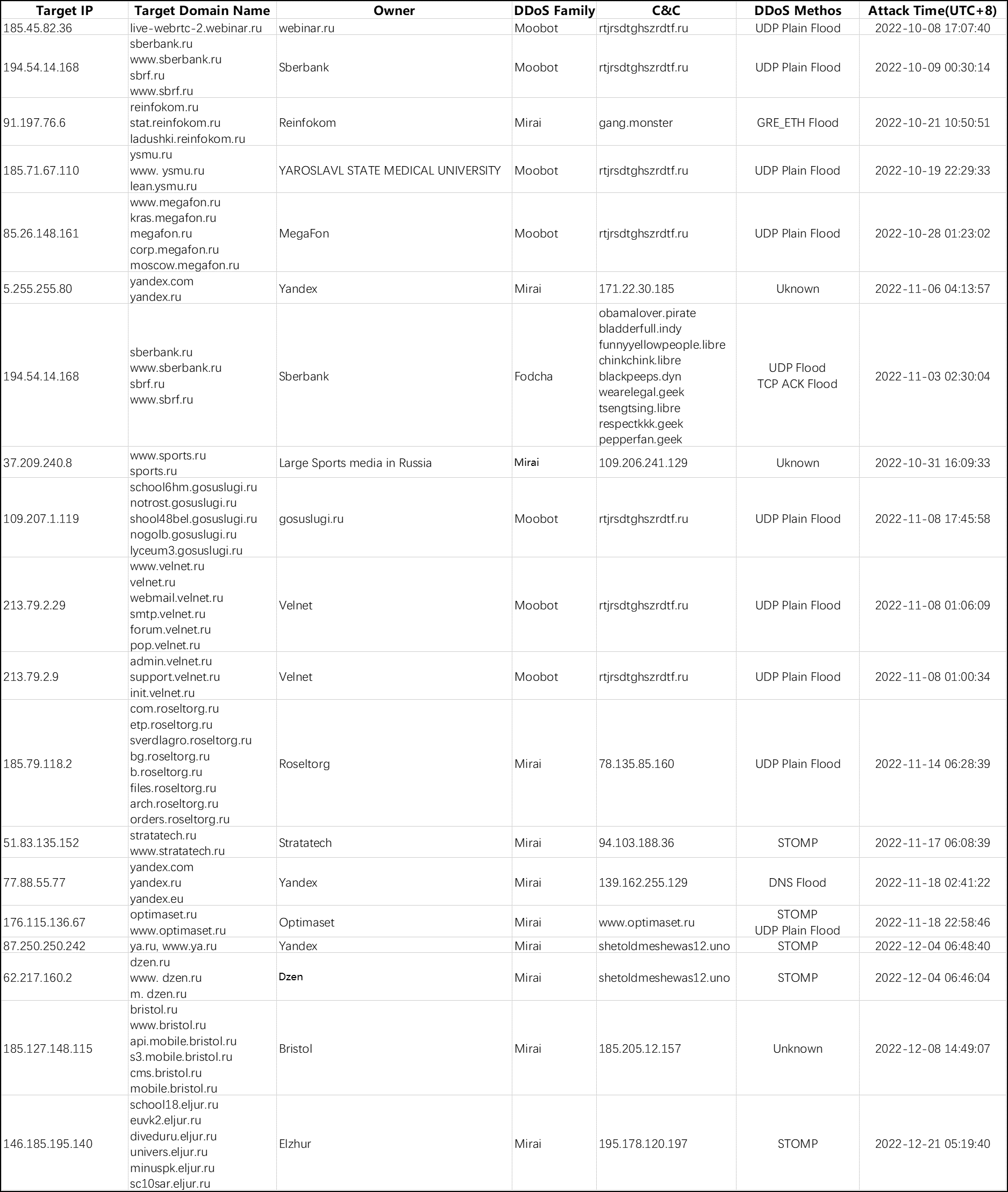
We have made statistics on the DDoS attack incidents of Russia and Ukraine in the fourth quarter of 2022, and some of the DDoS attack activities against Russian important targets are listed as follows:
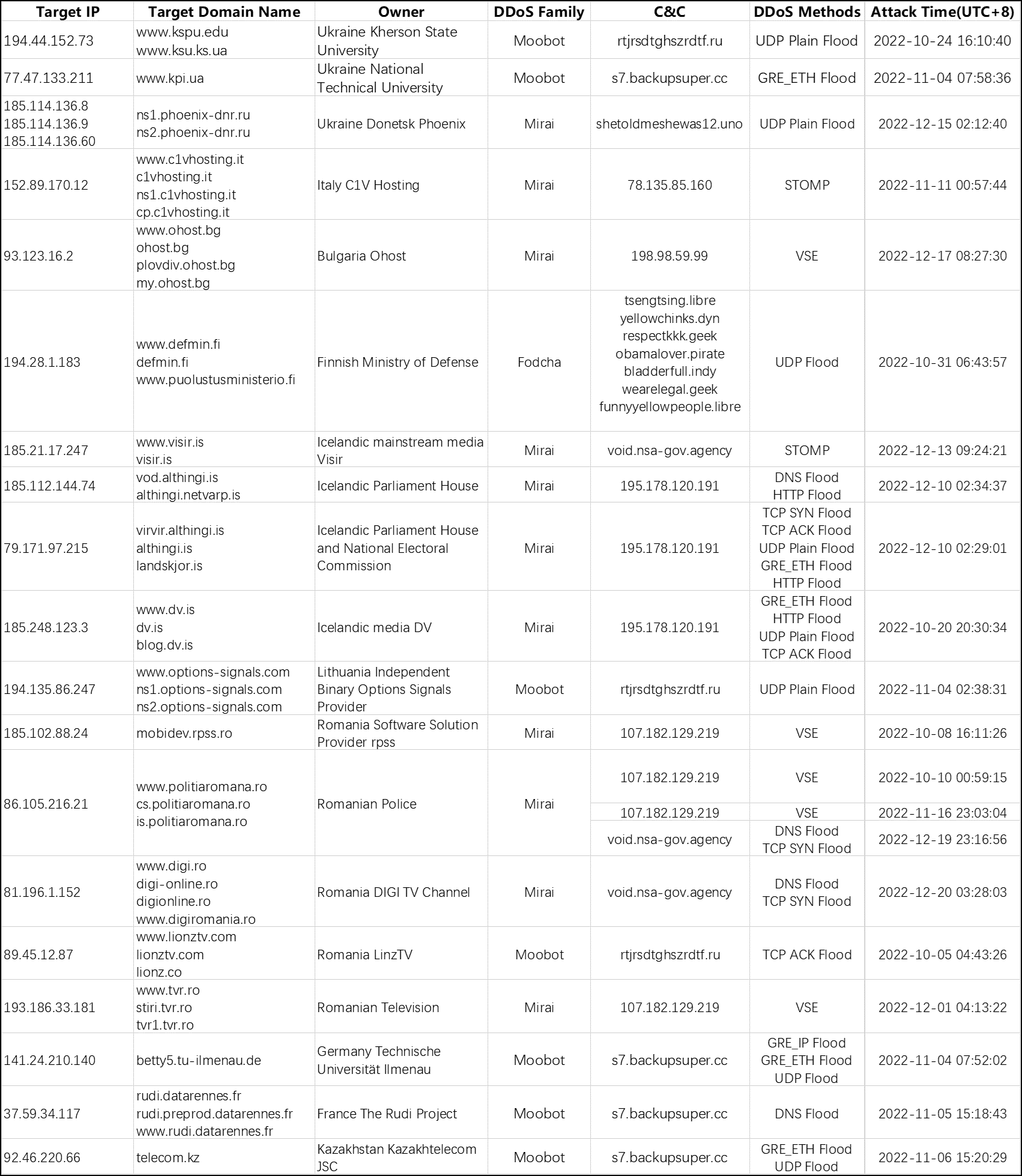
And then some of the DDoS attack activities against Ukraine important targets:
It can be seen that the most commonly used botnet family for launching DDoS attacks by both camps is Mirai, followed by Moobot, and Fodcha occasionally joins in to launch a large wave of attacks.
There also same C&Cs has attacked both Russian and Ukrainian targets. Generally, there is a DDoS attack platform that provides DDoS attack rental services behind this kind of C&Cs. In addition, it can also be seen that there are many hybrid attacks mixed with various DDoS attack methods. In theory, this can improve the success rate of DDoS attacks and increase the protection cost of the victim.
Botnet case study
While focusing on botnet and DDoS attack activity in the context of the Russia-Ukraine conflict, we noticed a suspicious Moobot family botnet with a C&C domain of s7.backupsuper.cc. This Moobot botnet has some features such as:
(1) The C&C domain name was registered in early October 2022, the first valid A record IP was resolved at the end of October, and then the IoT device vulnerability CVE-2016-6563 was used to spread immediately
(2) At first, there was a fixed Scanner IP 185.122.204.30 that exploited IoT device vulnerabilities to spread malware binary, which is located in Moscow, Russia, and the spread continued until 2022.11.13
(3) Within a few days of starting the spread, it frequently attacked important targets belonging to countries that had frictions with Russia, and rarely attacked other targets. After the attack, it stopped and did not launch any subsequent attacks.
Based on this evidence, we have reason to suspect that the controller behind it may be a pro-Russian person or organization.
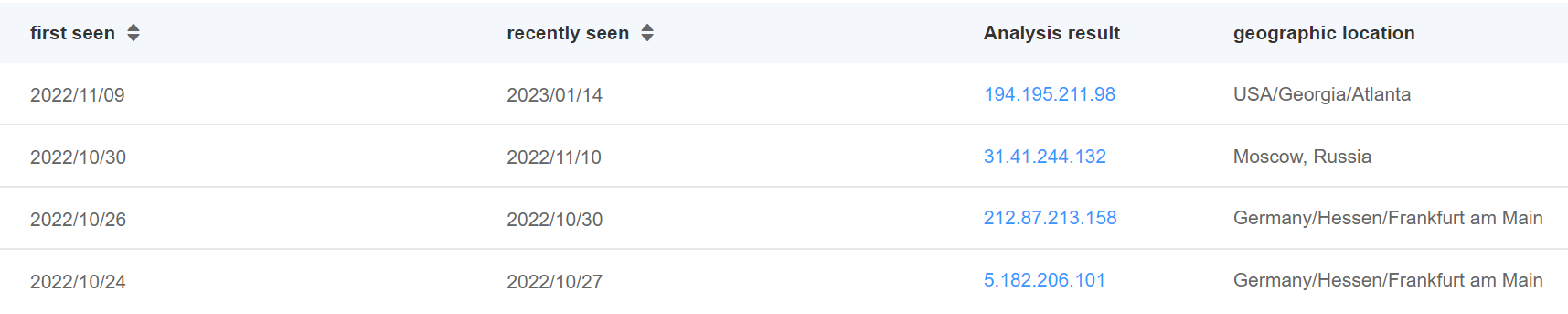
According to our threat intelligence data, the __backupsuper.c__c domain name was registered on 2022-10-03, and s7.backupsuper.cc was launched on 2022-10-24, and a total of 4 IPs have been resolved so far.
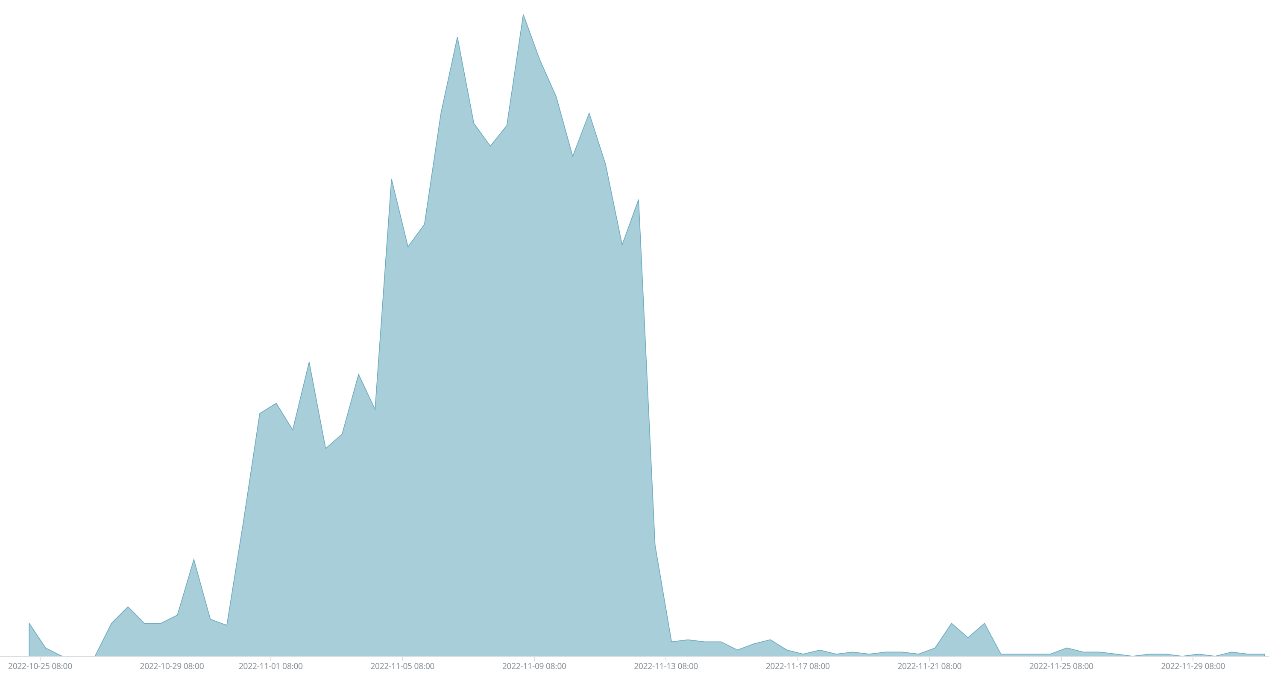
In addition, according to our PassiveDNS data, the C&C domain name launched a large wave of dissemination immediately after it went online. The access to the domain name immediately hit a spike, followed by a slight ups and downs, but the overall number of visits tended to decline. This shows that the samples of this family did control a large number of compromised devices at first, but due to various reasons, the number of compromised devices controlled by this family gradually decreased.
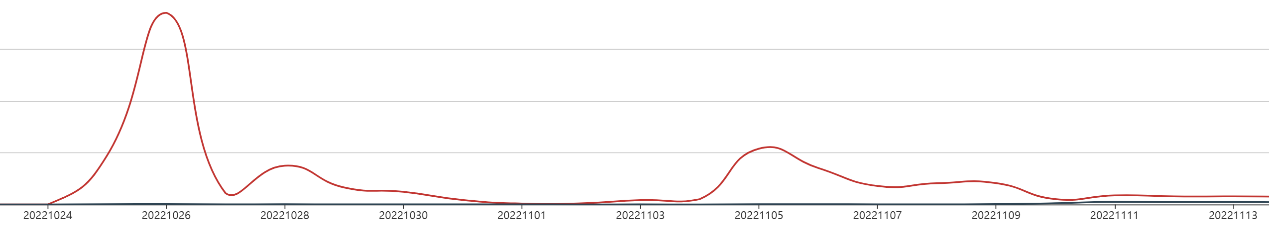
The monitoring data of our Unknown Threat Monitoring System shows that the botnet sample first spread through the CVE-2016-6563 vulnerability and immediately infected a large number of devices. The CVE-2017-17215 vulnerability was added to the later samples to start the worm-like propagation. In this way, the botnet spreads through a combination of fixed IP scanners exploiting vulnerabilities and worm-like propagation, but according to our PassiveDNS data, it may not infect too many devices in the later stage. The peak period of spreading malicious samples of this botnet is from 2022.10.30 to 2022.11.13. The overall spreading trend is as follows.
After the botnet exploits the vulnerability to successfully infect the device, it will download and execute a malicious shell script. The malicious shell script will violently download Moobot samples of multiple architectures and try to execute them. According to the code in the malicious shell script, the malicious sample constructed by the attacker supports the following CPU architectures:
- ARM5
- ARM6
- ARM7
- M68K
- PPC
- SH4
- x86
- x86-64
- MIPS
- MIPSLE
Now the download links for the malicious samples spread by this family are all unavailable, but it is not ruled out that new spreads will be launched in the future, or similar new botnets will appear, and we will continue to pay attention.
Summary
Since the Russian-Ukrainian conflict, the real-world war has entered a stalemate, but the attack and defence between the two camps in cyberspace has always been fierce. In addition to relatively secretive organizations, there are also different attack organizations in both camps that have been making various attack activities public, attracting more people's attention or even joining their activities, among which encrypted Ransomware, data erasure and DDoS are common attack methods .
In addition to the emergence of new forces, such as NoName057(16) Bobik and DDosia, the organizations involved in DDoS attacks on both sides, or attack tools, or Botnet families, the attack activities of Botnet families that have been exposed in the industry, such as Mirai/Moobot/Fodcha, etc., should not be underestimated. watch for. We will continue to monitor attacks from both camps.