1. Overview
Recently, the Threat Monitoring System of QiAnXin Threat Intelligence Center monitored that a botnet written in GO language was spreading through multiple vulnerabilities. After analysis, it was confirmed that the sample belonged to the discovered botnet family Kaiji.
Kaiji botnet was exposed by MalwareMustDie in 2020, and then Intezer did an in-depth analysis about this malware. Its variant was also called Chaos by Black Lotus Labs (the Threat Intelligence division of Lumen Technologies). In July 2022, Sangfor Further Eye Lab published an article stating that the Kaiji botnet was being reconstructed. This year we found that the botnet had resurfaced and upgraded.
When correlating variants of Kaiji botnet, analysts accidentally discovered that the Kaiji botnet is related to a giant botnet rental group we are tracking -- Ares.
2.Ares Group
2.1 Group Name
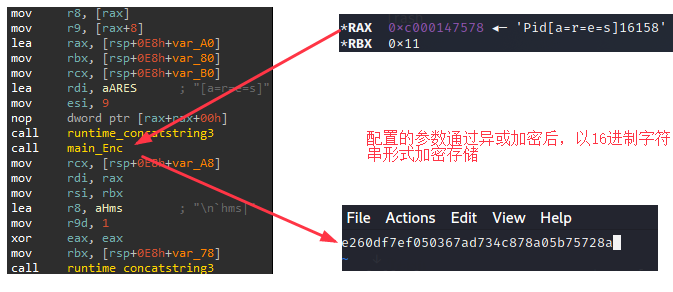
We named the hacking group “Ares” for three reasons. First we found that the creators who built the Kaiji variant called it "ares". Second, the new variant configuration uses "[a=r=e=s]" as a separator. And last, recently we found that multiple assets of the hacking group were uniformly changed to the same login page, and in the page the group also calls itself " Ares" and writes an English slogan "look before you leap".
2.2 Group Assets
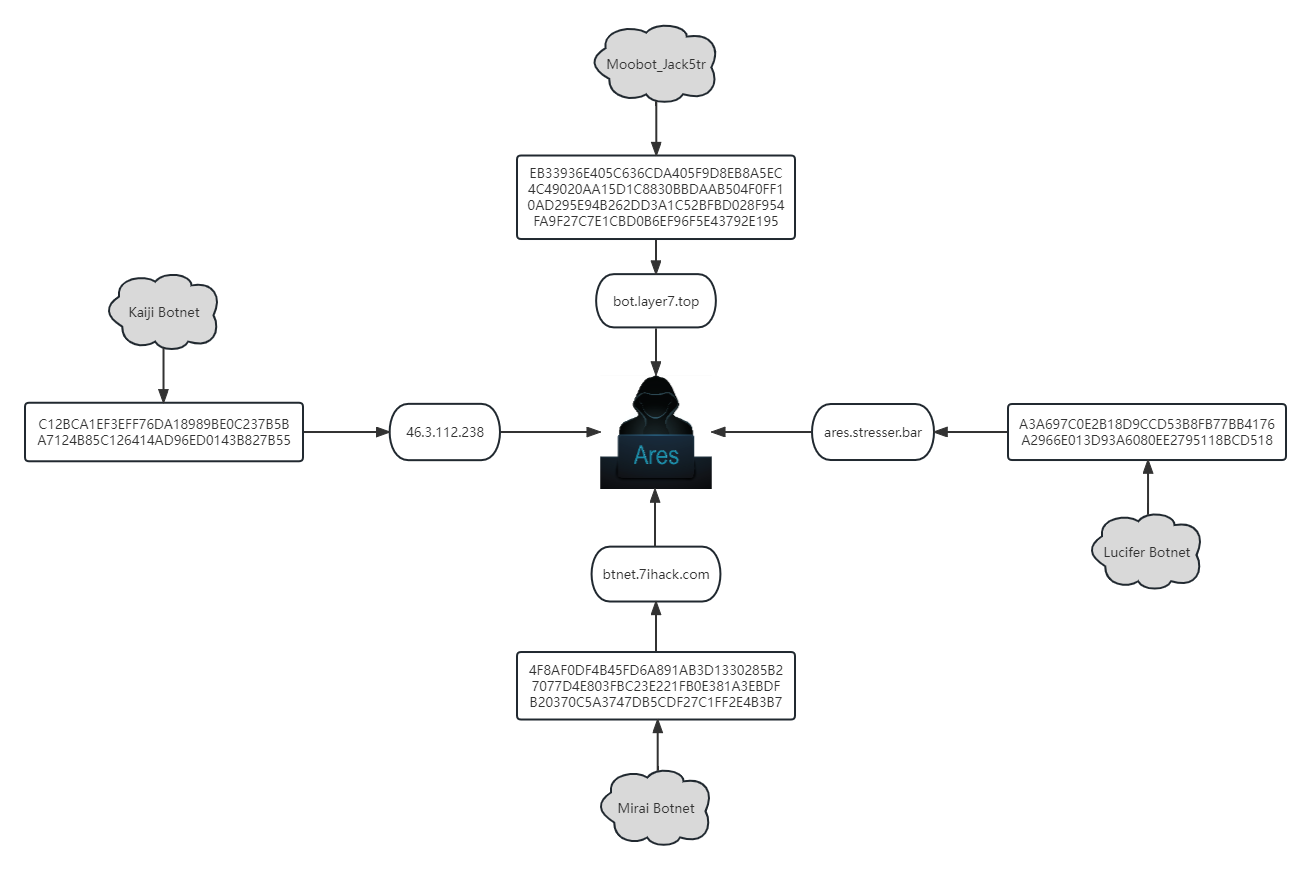
In addition to Kaiji botnet, the Ares group also owns several other families of botnets, including Mirai, Moobot, and Lucifer. Its Moobot family is so numerous and modified from the original , so we named this variant Moobot_jack5tr when we started tracking this group last year.
Assets and associations are shown below:
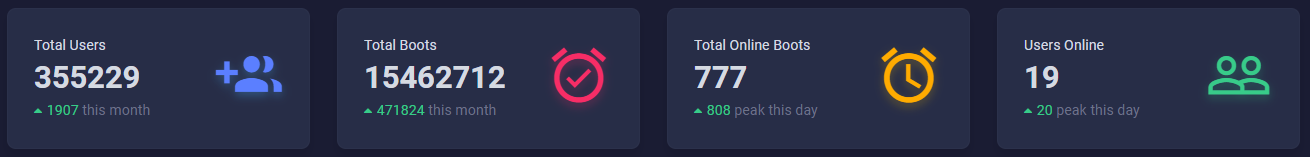
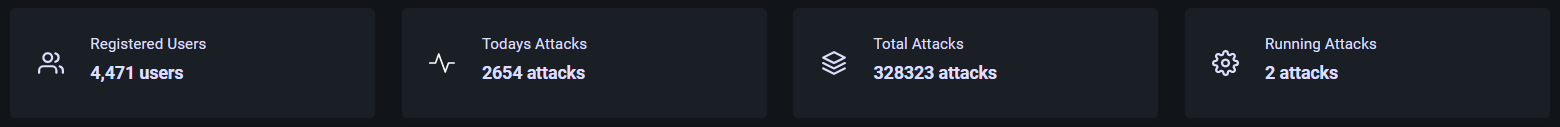
2.3 Giant Rental Botnet
Ares group owns an enormous botnets and provides rental services. It operates several rental platforms, the following graphs show data of some of the platforms owned by the group. From these graphs it can be seen that these platforms attracted plenty of users and launched a large number of DDoS attacks.
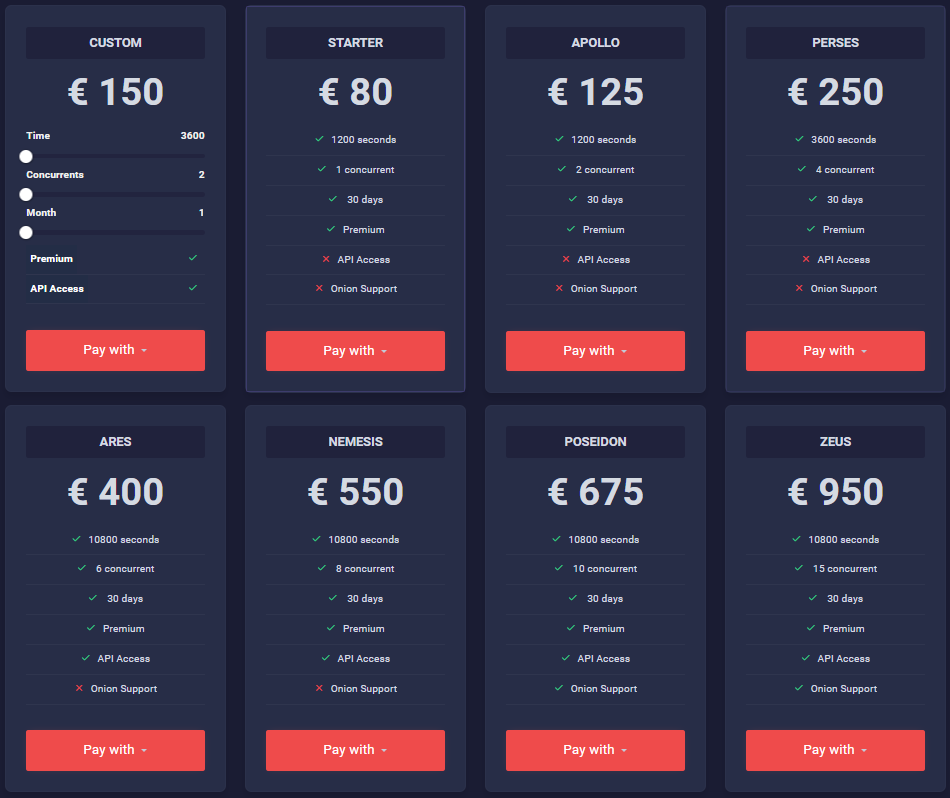
The price section for DDoS attack leasing is as follows.
2.4 Mining Activities
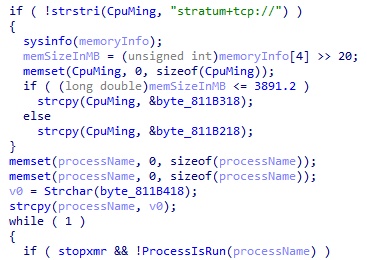
In addition to the botnet, Black Lotus Labs disclosed that the group has distributed XMRig for mining operations. Our analysis this time also found that the Lucifer family botnet samples distributed by the group will create separate threads for XMRig mining in addition to DDoS attacks and remote command execution.
2.5 Members of The Group
The Kaiji botnet was attributed to China by the Intezer team and the MalwareMustDie group when it was exposed. The reason for this is that the function naming of the family's samples and the way instructions are parsed are in Chinese pinyin or Chinese characters, which was also confirmed when we analyzed the assets of the Ares group -- the group is used to using Chinese for annotations in its web pages.
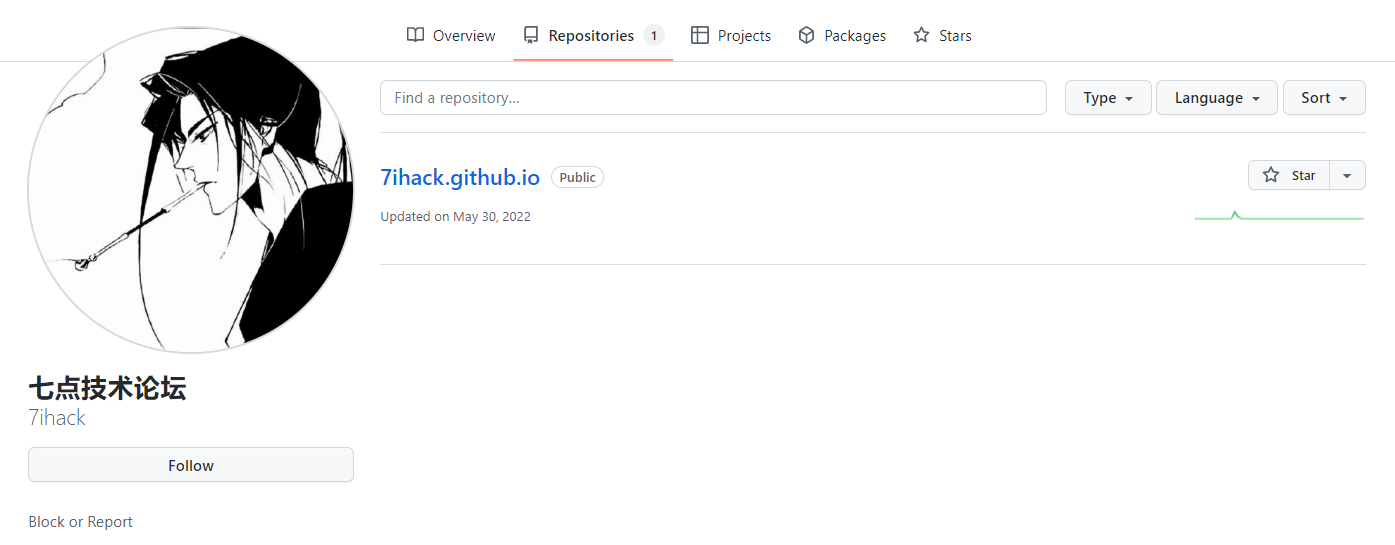
Meanwhile, a developer who was a suspected member of the group was found when tracing the source, and the member used to run a hacking technology discussion forum.

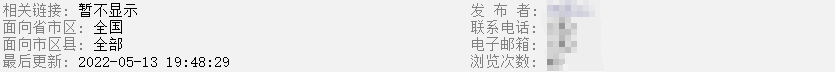
Last year the member also purchased advertising services for the forum.
The forum has currently changed to a DDoS service rental platform (the attacker legitimately interprets this new service as stress testing) and claims not to allow attacks on government, banking or educational sites.
2.6 Attack Movement
In the process of monitoring jack5tr, we found that the group was involved in the Russian-Ukrainian cyber war. In early November last year, we monitored jack5tr's DDoS attacks on important targets of the Ukrainian camp, and we are unable to determine whether the attack came from the Ares group or from a user who rented the group's attack service.
The CC domain of Moobot_jack5tr, which participated in this attack against Ukraine, is " s7.backupsuper.cc ".
3. Analysis of Kaiji Variants
The new variant of Kaiji contains the string "Pro" (in English) in its beacon package, so we named the variant Kaiji_Pro.
We focus on analyzing the similarities and differences of the new variants, using the x86-64 sample as an example for analysis, as follows.
| Name | linux_amd64 |
| Size | 5234688 bytes |
| MD5 | A7124B85C126414AD96ED0143B827B55 |
3.1 Configuration Files
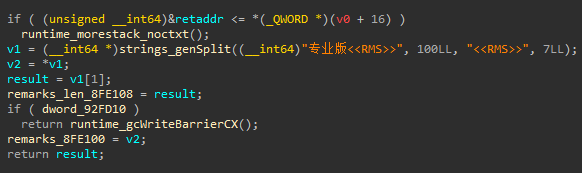
Configuration files are used in Kaiji_Pro to store its commands. The sample runs with a encrypted configuration file named ".walk.lod" on local machine, with paths selected from "/dev", "/etc", "/mnt", "/opt", "/sys", "/usr", "/run", "/var/run", "/tmp". Configuration commands separated by separator "[a=r=e=s ]".
| - | - |
|---|---|
| Parameters | Meaning |
| Pid | Reading this parameter will kill the process corresponding to the PID. |
| Begin、End | Describes a range of IP addresses that replace the source IP when carrying out DDoS attacks. In earlier versions these two parameters were controlled only by C2 instructions, called ipbegin and ipend respectively. |
| Backdoor | Backdoor mode flag bit, affecting C2 selection. |
| Remarks | Bot mark, default is "Pro". |
The configuration file supports 5 parameters: Pid, Begin, End, Backdoor, and Remarks. Pid is the Pid number of the sample process; Begin and End are used to record an IP range, if this parameter is configured, in some subsequent ddos attacks (syn, ack, udp), the IP of this range will be used to work as preference IP address; Backdoor parameter marks whether the sample is in backdoor mode, which may affect the selection of sample C2; Remarks records the mark of the sample, and by default this parameter is "Professional" in Chinese.
3.2 Means for Hiding
Similar to older versions of Kaiji, Kaiji_Pro has taken extensive measures to ensure the invisibility and persistence of samples. This section uses a lot of older Kaiji code, but since this code has not been rigorously tested, some of the code will lead to some unintended results.
Kaiji_Pro's hidden locations and startup methods are listed below.
| - | - |
|---|---|
| Malicious programs | Startup method |
| /etc/opt.services.cfg | Write a shell script “/etc/32677”, the script starts opt.services.cfg every 60 seconds and this script is started and run by the sample. |
| /usr/lib/libgdi.so.0.8.1 | Write a shell script “/.mod”, and the script program is configured as a crontab task. |
| /lib/system-mark | Inject shell scripts under the paths "/etc/rc.d/init.d/", "/etc/init.d/", "/etc/rc.d/" to call execution. |
| ls、ps、ss、dir、netstat、find、lsof under the “/usr/bin/” | Run when the user executes the command. |
| /tmp/seeintlog | Be called after the execution of the real command when run through disguise system commands. |
| /usr/sbin/ifconfig.cfg | Inject files: "/etc/rc.local", "/etc/rc.d/rc.local", "/etc/init.d/boot.local" to run. |
| /etc/profile.d/bash_cfg | Write the script "/etc/profile.d/bash_cfg.sh" to invoke execution. |
| /boot/System.mod | 1.Inject the service configuration file "/usr/lib/systemd/system/quotaoff.service" to start via service 2.Use the audit2allow tool, add the policy module for SELinux and install it using the semodule 3.Add the dns-tcp4 service, whose configuration file points to the malicious program |
3.3 Bugs in New Variant
There are multiple bugs in the Kaiji_Pro sample.
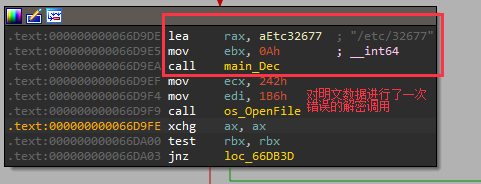
Kaiji_Pro tries to copy the sample "/etc/opt.services.cfg" file and write and run a persistent sh script at "/etc/32677". However, the author made one call to the decryption function for the plaintext sh script filename, which caused the sh script filename to become garbled and finally resulted in the malicious sh script not being executed.
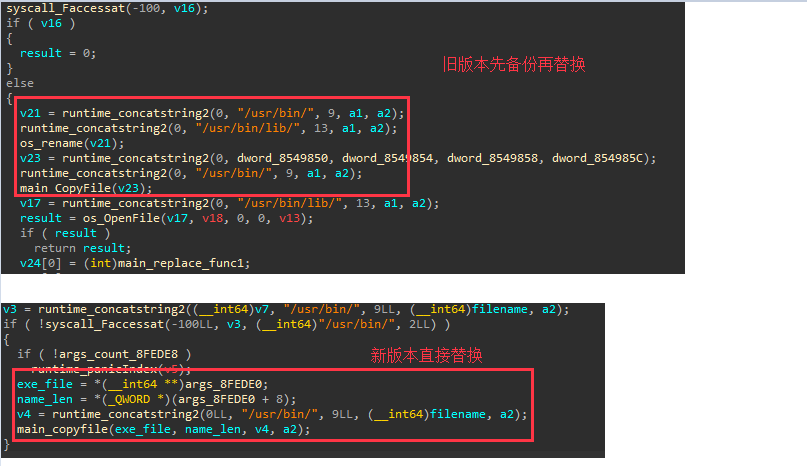
The sample tries to replace the ls, ps, ss, dir, netstat, find, and lsof command files under "/usr/bin/", causing the user to execute the malicious sample first when using the above commands on the compromised machine. The real command file is called under "/usr/lib/include/" at sample runtime by judging the filename and outputting the command. However, due to some missing code, the "/usr/lib/include/" path will be empty. Eventually, the machine will not be able to execute the above commands properly.
We speculate that the latest variant sample was written by a new member of the Ares group, who was not as familiar with the sample.
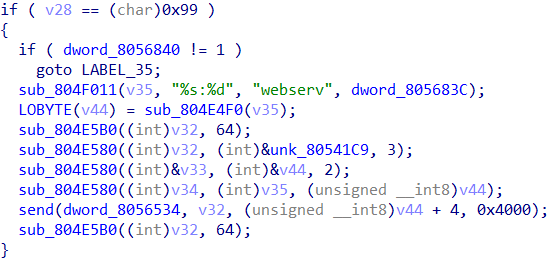
3.4 Communication Protocols
The communication between Kaiji_Pro and C2 is encrypted using TLS, and compared to the old version, the new version no longer uses "<<<<<!!! >>>>>" for message separation. Besides, a new data header consisting of 50 bytes of hard-coded data with variable and meaningless 4 bytes has been added.
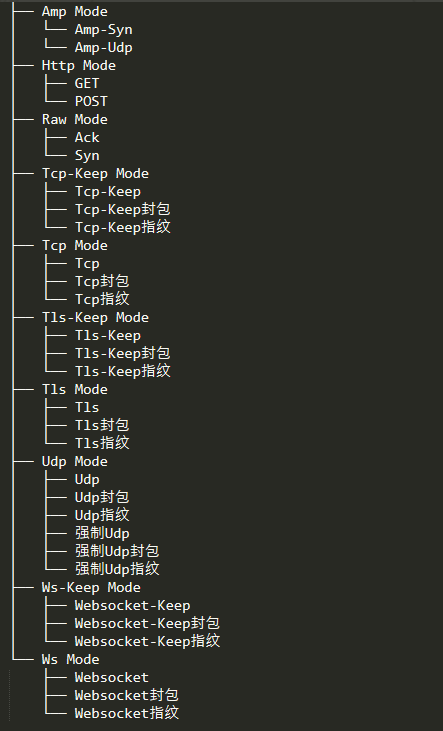
Commands issued include modify bot configuration, functional commands, attack commands. Compared to the old version it adds support for the type of attack for the Websocket protocol, the author's classification of its attack types are as follows.
3.5 Dissemination Methods
This spreads through exploits with password blasting, and recently used exploits are shown in the table below.
| - | - |
|---|---|
| Vulnerability | Vendor |
| CVE-2021-22204 | ExifTool |
| CVE-2021-22205 | Gitlab |
| CVE-2017-0144 | Windows SMB |
| CVE-2014-8361 | Realtek SDK |
| MVPower DVR - Shell Command Execution | MVPower DVR |
4. Analysis of Moobot_jack5tr
Moobot_jack5tr is a large botnet owned by the group, the variant is modified by Moobot_Xor. Take the x86 sample here as an example, mainly to analyze the differences with the original version. the sample information is as follows.
| Name | huax86 |
| Size | 55632 bytes |
| MD5 | EB33936E405C636CDA405F9D8EB8A5EC |
4.1 Command-line Execution
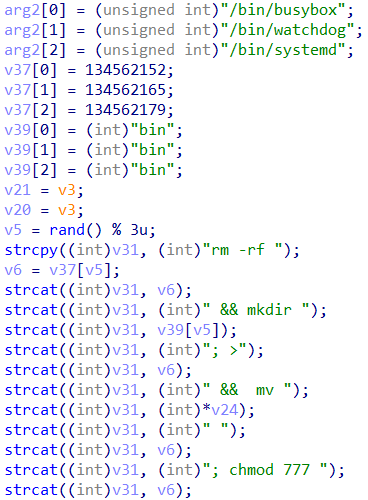
This variant has a distinctive feature, after the main function starts it will first splice a command string to execute, the main purpose of the command line is to create a bin directory for hiding sample, the name is randomly selected from the normal program names such as busybox, watchdog, systemd, etc.
4.2 Start the httpd Service
When Moobot_jack5tr is run, it opens a random httpd port and uploads the port information to C2, which is used to continue propagating the sample. In short, it opens a mini web service to use the lost host as one of the nodes for sample propagation.
4.3 Communication Protocols
The communication protocol and other functions of Moobot_jack5tr are basically the same as Moobot_Xor, and the uplink packet is still "33 66 99".
5. IoCs
MD5:
EB33936E405C636CDA405F9D8EB8A5EC
4C49020AA15D1C8830BBDAAB504F0FF1
0AD295E94B262DD3A1C52BFBD028F954
FA9F27C7E1CBD0B6EF96F5E43792E195
C12BCA1EF3EFF76DA18989BE0C237B5B
A7124B85C126414AD96ED0143B827B55
A3A697C0E2B18D9CCD53B8FB77BB4176
A2966E013D93A6080EE2795118BCD518
4F8AF0DF4B45FD6A891AB3D1330285B2
7077D4E803FBC23E221FB0E381A3EBDF
B20370C5A3747DB5CDF27C1FF2E4B3B7
C&C:
Moobot_jack5tr:
104.244.76.7: 56999
s7.backupsuper.cc:56999
vds.hostlookl.cc:56999
adsl.testapiss.online:56999
gang.monster:56999
control.rawrgaming.icu:56999
Kaiji_pro:
www.chaosii.com
www.2s11.com
llkh.net
998n.f3322.net
23.224.143.170:8000
193.29.15.178:19329
193.29.15.178:32677
205.185.117.18:8080
104.218.236.103:32677
163.197.248.66:8888
205.185.117.18:8888
23.224.143.170:8888